Explore how AirSnitch attacks undermine Wi-Fi security, bypassing encryption and client isolation. Learn actionable defenses.


Explore how AirSnitch attacks undermine Wi-Fi security, bypassing encryption and client isolation. Learn actionable defenses.

Block’s 40% workforce cut highlights AI’s impact on labor and market dynamics. Understand its implications for investors and the tech sector.

Unlock the secrets to writing high-performance Julia code with actionable tips and advanced techniques for optimization.
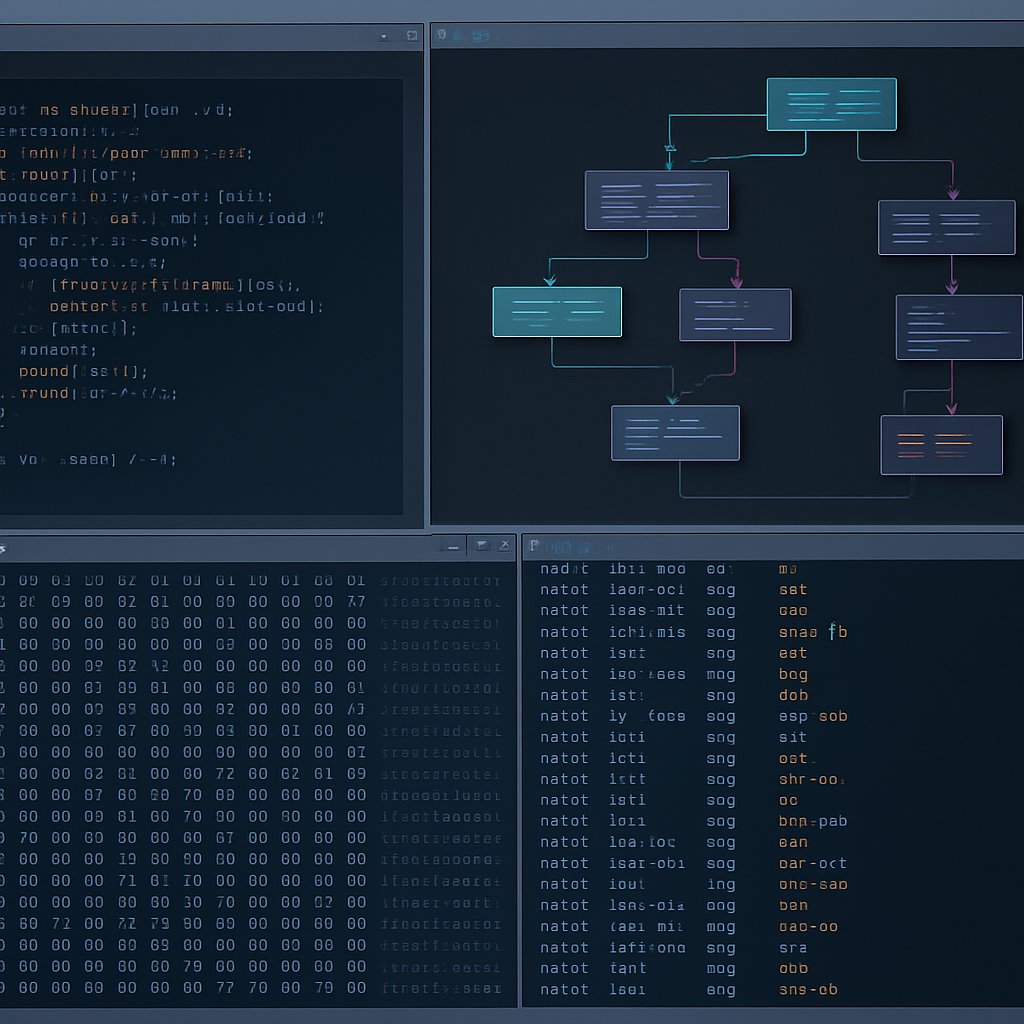
Explore advanced Ghidra techniques for reverse engineering, including automation and handling edge cases in binary analysis.

Learn how to effectively integrate Ghidra into SOC architecture for streamlined binary analysis and enhanced incident response.

Unlock the power of Ghidra for reverse engineering with this comprehensive guide, exploring its features, installation, and common pitfalls.

Explore Google’s Nano Banana 2, a cutting-edge AI image generator that merges speed and quality. Learn about its features, applications, and implications.

Prepare for security audits with actionable insights on evidence collection, common findings, and best practices for compliance.