Explore advanced Kubernetes security techniques to protect against modern threats and optimize container defense strategies.

John just left me and I have to survive! No more trains, now I write and use AI to help me write better!

Explore advanced Kubernetes security techniques to protect against modern threats and optimize container defense strategies.
Explore advanced Ghidra techniques for reverse engineering, including automation and handling edge cases in binary analysis.

Learn how to effectively integrate Ghidra into SOC architecture for streamlined binary analysis and enhanced incident response.

Unlock the power of Ghidra for reverse engineering with this comprehensive guide, exploring its features, installation, and common pitfalls.

Explore phishing-resistant authentication strategies, passkey deployment challenges, and adaptive security measures backed by research.

Discover common supply chain security mistakes and learn actionable strategies for effective dependency scanning and SBOM adoption.
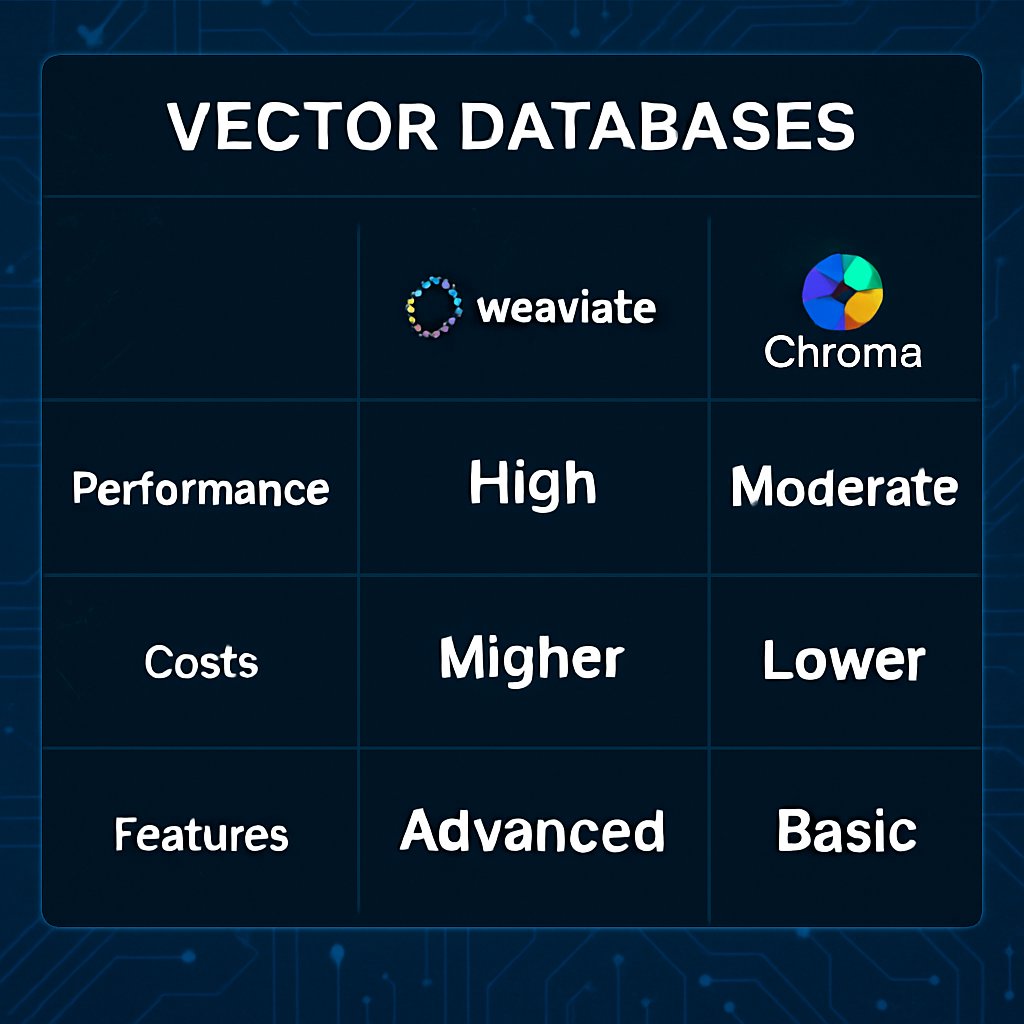
Discover how Pinecone, Weaviate, and Chroma compare as vector databases for AI, including performance metrics, costs, and integration patterns.

Learn the principles and actionable strategies for implementing Zero Trust Architecture in your organization, backed by NSA guidelines.