
Container Security Best Practices: Strengthening Your Posture
Strengthen your container security posture with our comprehensive guide on best practices and actionable controls for production environments.

Strengthen your container security posture with our comprehensive guide on best practices and actionable controls for production environments.
Master Linux hardware hotplug events with udev and netlink for reliable automation and monitoring in production systems.

Explore the key differences between GDPR and CCPA compliance, focusing on dual compliance strategies and enforcement implications.

Discover how to maximize productivity with Google Workspace CLI for automation. Learn practical tips and security considerations for effective workflows.
Explore NanoGPT Slowrun: a benchmark for data-efficient language modeling with unlimited compute and fixed data, achieving 5.5x efficiency gains.

Compare RAG stacks for enterprise knowledge bases, focusing on architecture, vector databases, and performance benchmarks.
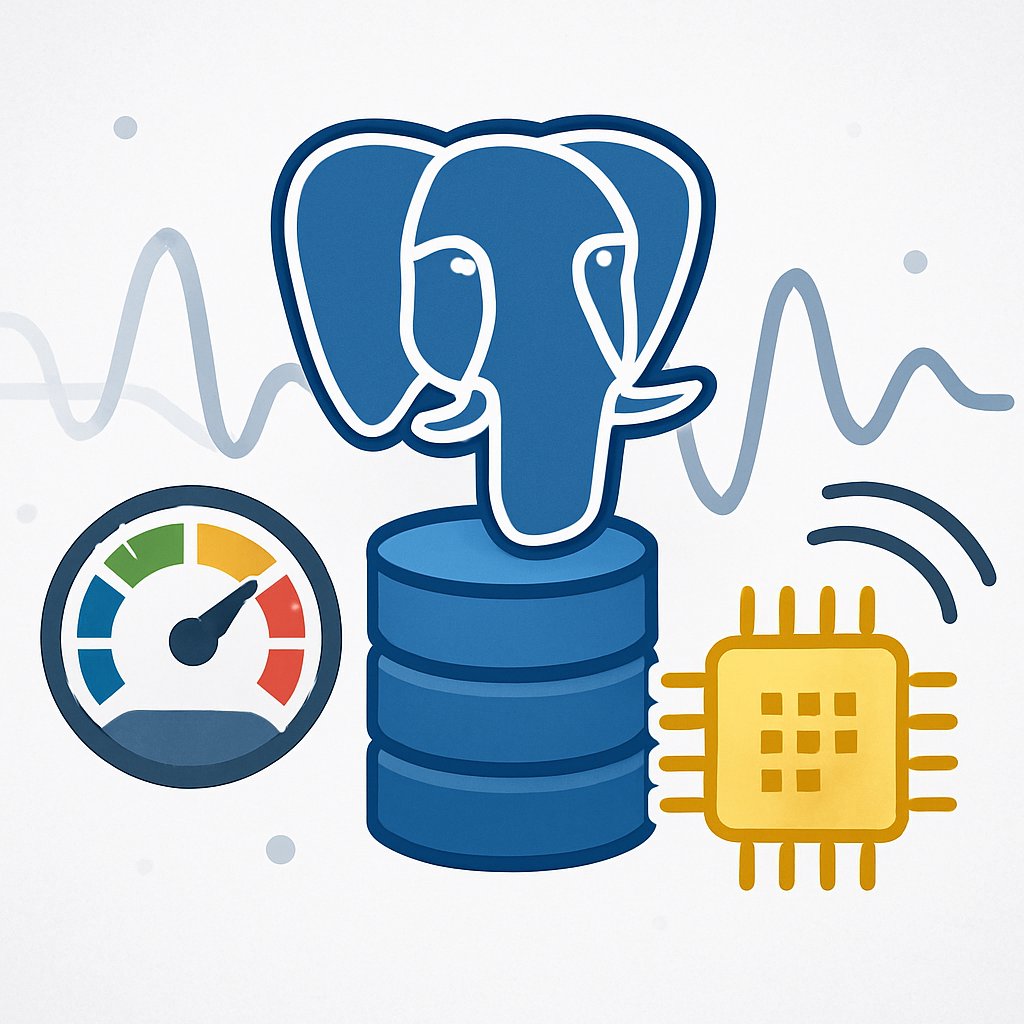
Learn how to enhance PostgreSQL performance using pg_jitter for efficient JIT compilation, with practical examples and configurations.

Learn how to operationalize GDPR Article 25 with practical strategies for Privacy by Design, DPIAs, and data minimization.
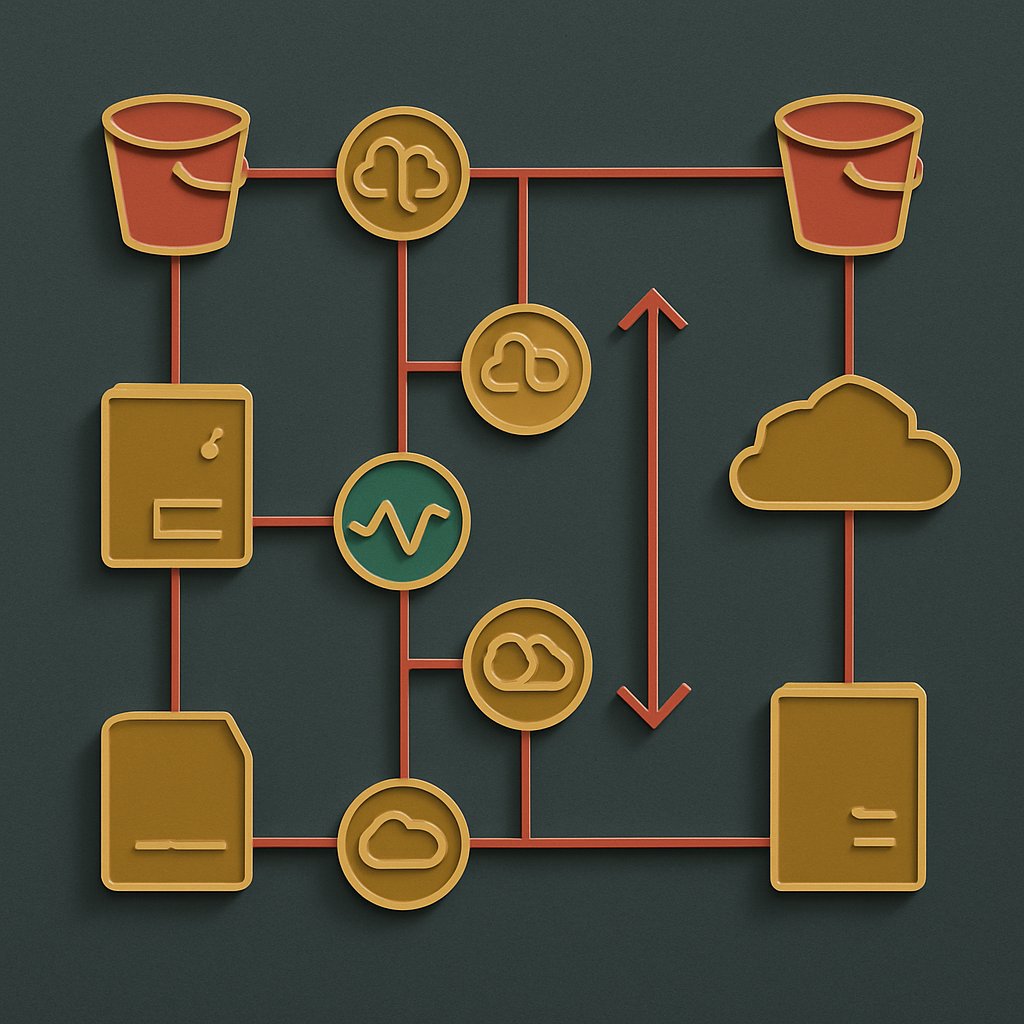
Learn about the AWS Middle East outage, its implications, and how to future-proof your cloud infrastructure against geopolitical risks.
Explore how the new obsidian-headless client enables automation and scripting for Obsidian vaults, transforming workflows for power users.

Implementing GDPR compliance is vital for organizations handling EU personal data. This checklist covers essential steps for operational success.

Explore advanced Kubernetes security techniques to protect against modern threats and optimize container defense strategies.