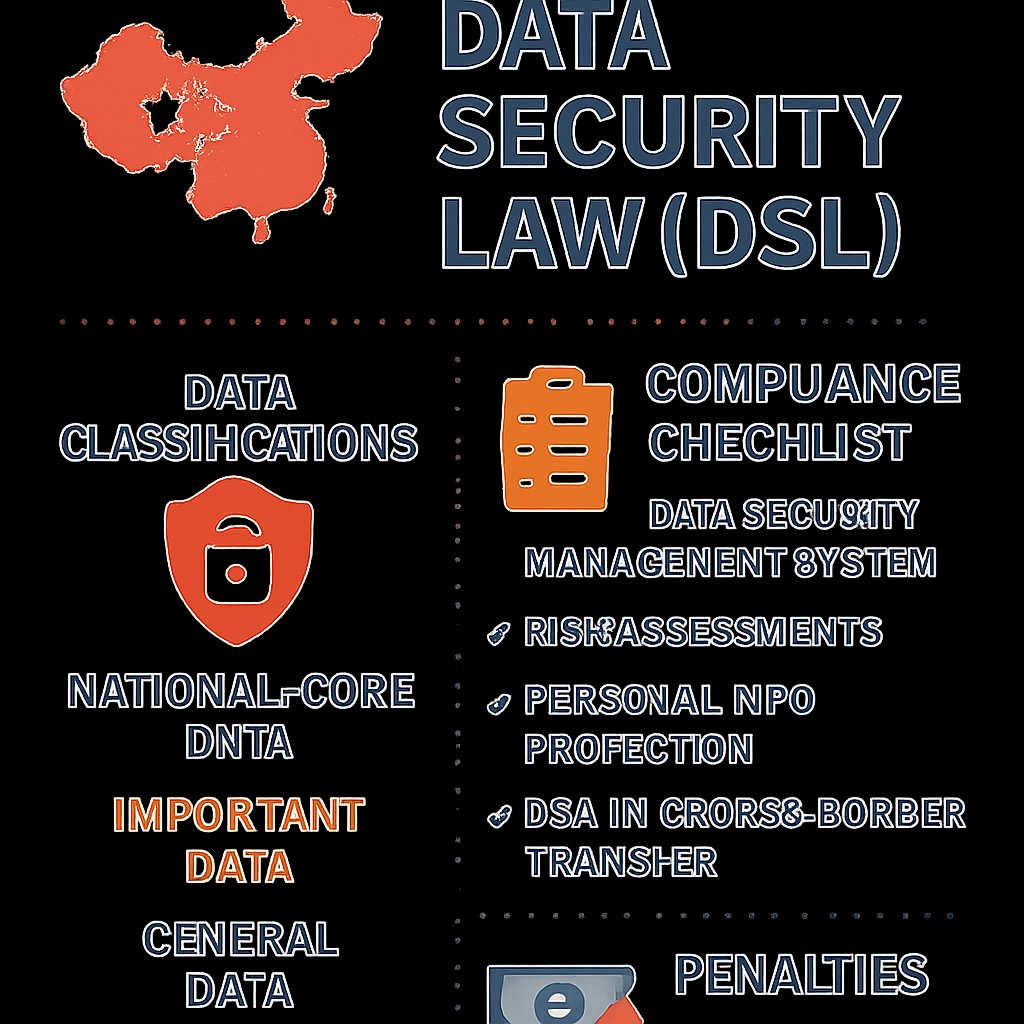
China’s Data Security Law (DSL): Key Compliance Insights
Learn about China’s Data Security Law (DSL), key data classifications, national security reviews, and compliance strategies for foreign companies.
February 23, 2026
8 min read