
Comprehensive Guide to Vendor Risk Management
Understand vendor risk management essentials and compliance frameworks. Learn actionable strategies to enhance third-party security and oversight.

Understand vendor risk management essentials and compliance frameworks. Learn actionable strategies to enhance third-party security and oversight.

Implementing GDPR compliance is vital for organizations handling EU personal data. This checklist covers essential steps for operational success.

Explore advanced Kubernetes security techniques to protect against modern threats and optimize container defense strategies.

Explore how AirSnitch attacks undermine Wi-Fi security, bypassing encryption and client isolation. Learn actionable defenses.
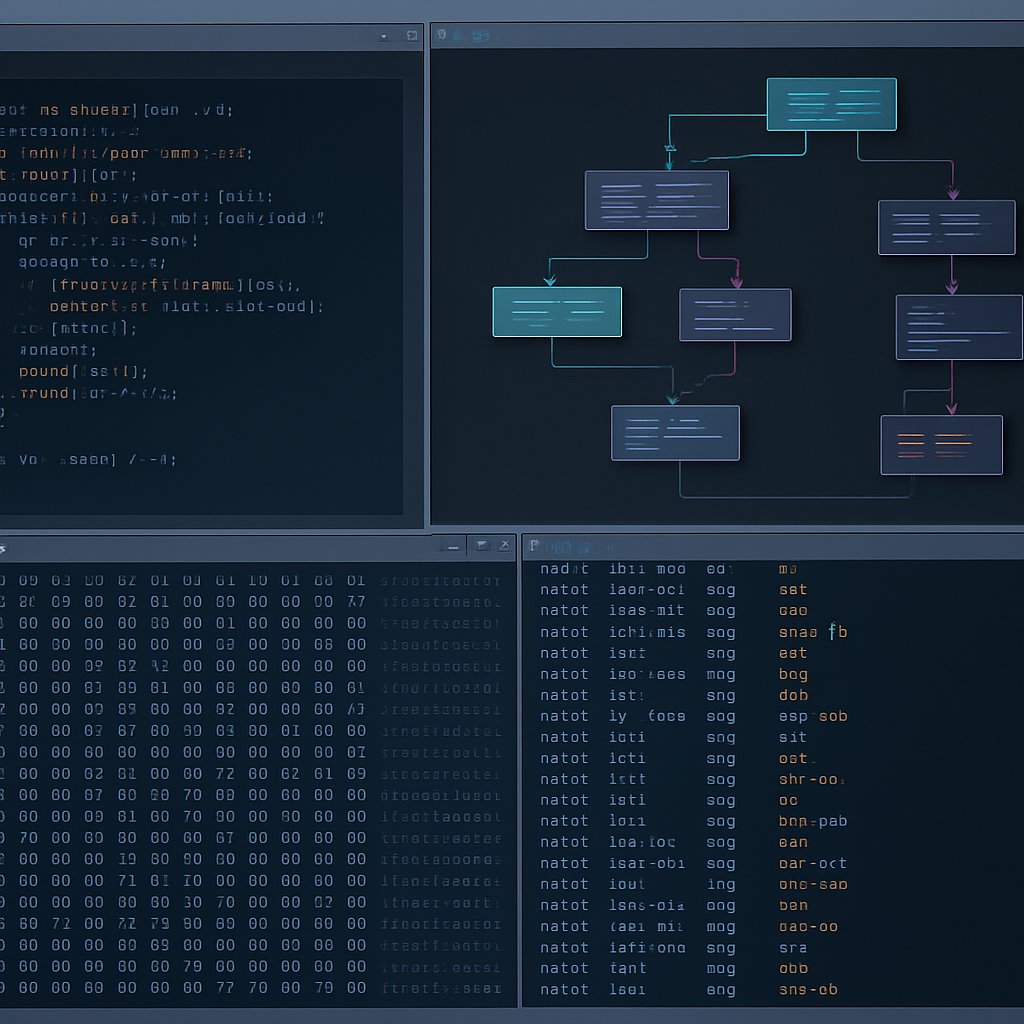
Explore advanced Ghidra techniques for reverse engineering, including automation and handling edge cases in binary analysis.

Learn how to effectively integrate Ghidra into SOC architecture for streamlined binary analysis and enhanced incident response.

Unlock the power of Ghidra for reverse engineering with this comprehensive guide, exploring its features, installation, and common pitfalls.

Prepare for security audits with actionable insights on evidence collection, common findings, and best practices for compliance.

Explore Windows 11 Notepad’s Markdown support, the CVE-2026-20841 vulnerability, and best practices for secure documentation.

Learn how to secure BYOD and corporate devices with effective Mobile Device Management strategies, including MDM vs. MAM, enrollment, and policies.

Discover how Firefox 148’s AI kill switch enhances user control over AI features, ensuring privacy and compliance in today’s digital landscape.

Explore phishing-resistant authentication strategies, passkey deployment challenges, and adaptive security measures backed by research.