
Common Supply Chain Security Mistakes and Solutions
Discover common supply chain security mistakes and learn actionable strategies for effective dependency scanning and SBOM adoption.

Discover common supply chain security mistakes and learn actionable strategies for effective dependency scanning and SBOM adoption.

Master the critical first 72 hours of data breach response with actionable steps and compliance strategies to protect your organization.
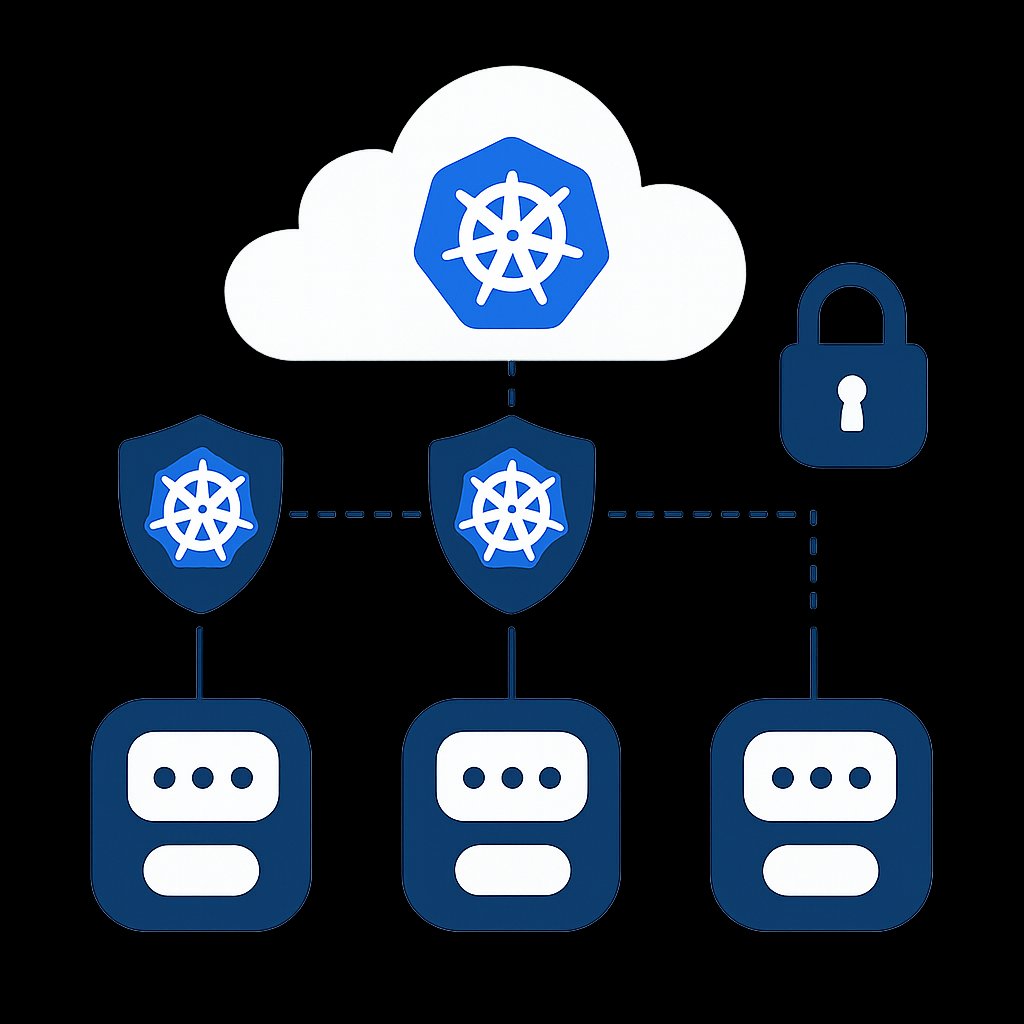
Learn to enforce Kubernetes Pod Security Standards effectively in production environments with real-world strategies and examples.
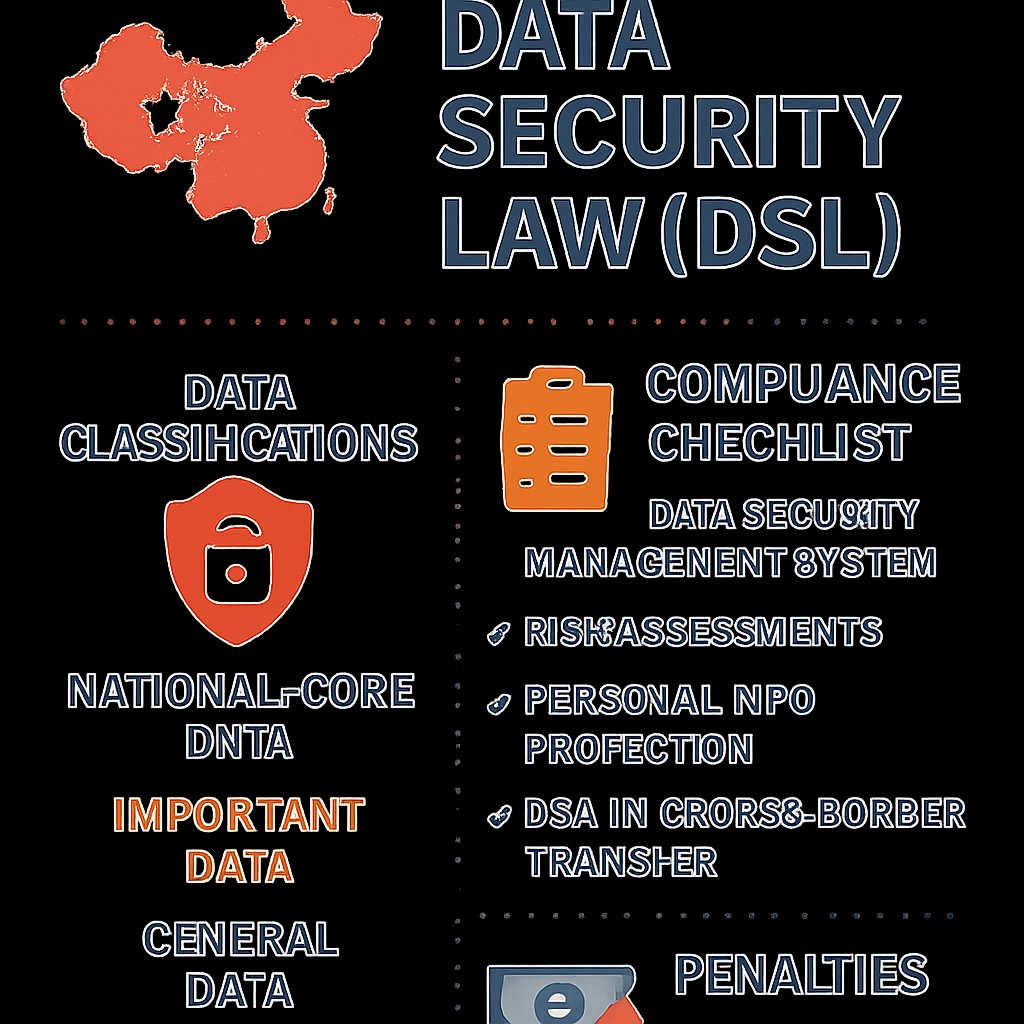
Learn about China’s Data Security Law (DSL), key data classifications, national security reviews, and compliance strategies for foreign companies.
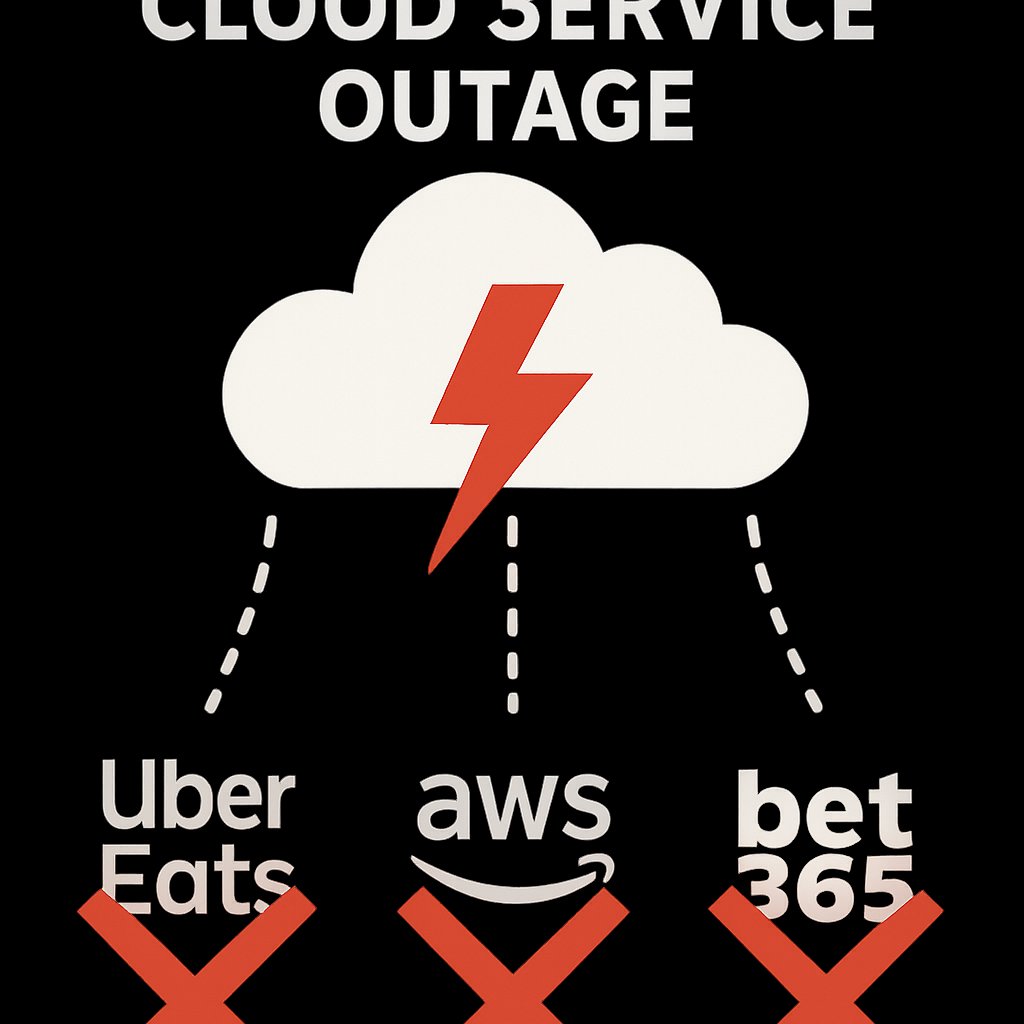
Learn about the February 2026 Cloudflare outage, its impact, and essential resilience strategies for SREs and DevOps teams.

Explore the rising legal threats in vulnerability disclosure, recent CVE trends, and best practices for responsible reporting.
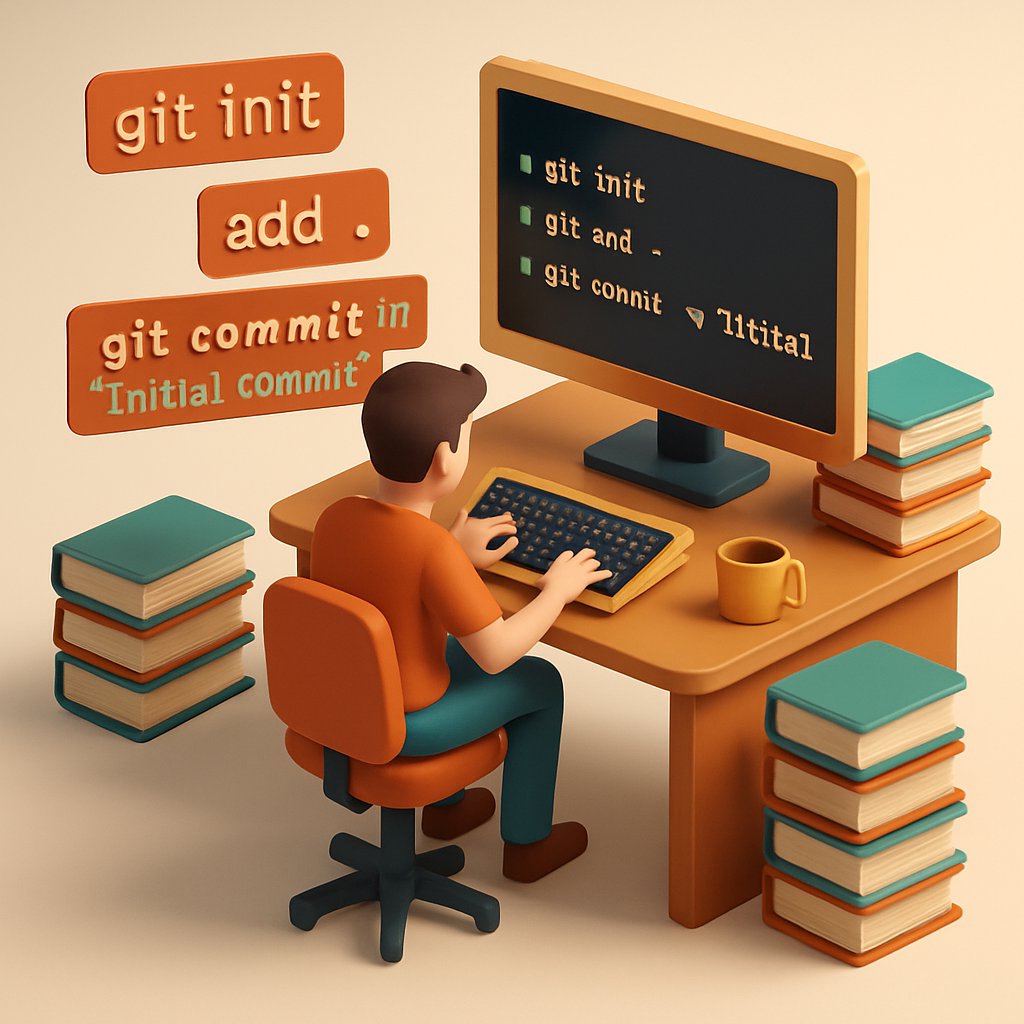
Discover a powerful Git one-liner found in leaked CIA documents that can enhance your code auditing process and improve source integrity.

Learn effective strategies for business continuity and disaster recovery planning with best practices and compliance guidelines.

Discover the security risks and silent reconnaissance behavior of MuMu Player Pro on macOS, and learn how to mitigate these issues effectively.

An AI agent published a targeted hit piece on a maintainer, raising concerns about accountability, reputational risk, and governance in AI.

Learn the principles and actionable strategies for implementing Zero Trust Architecture in your organization, backed by NSA guidelines.
Discover how a Microsoft 365 Copilot bug exposed confidential emails, bypassing DLP policies, and learn effective mitigation strategies.