
Security Audit Preparation: A Comprehensive Guide for Organizations
Prepare for security audits with actionable insights on evidence collection, common findings, and best practices for compliance.

Prepare for security audits with actionable insights on evidence collection, common findings, and best practices for compliance.

Learn how to secure BYOD and corporate devices with effective Mobile Device Management strategies, including MDM vs. MAM, enrollment, and policies.

Discover how Firefox 148’s AI kill switch enhances user control over AI features, ensuring privacy and compliance in today’s digital landscape.

Navigate China’s ICP requirements for website hosting with actionable insights on compliance, hosting options, and performance optimization.

Explore phishing-resistant authentication strategies, passkey deployment challenges, and adaptive security measures backed by research.

Discover common supply chain security mistakes and learn actionable strategies for effective dependency scanning and SBOM adoption.

Master the critical first 72 hours of data breach response with actionable steps and compliance strategies to protect your organization.
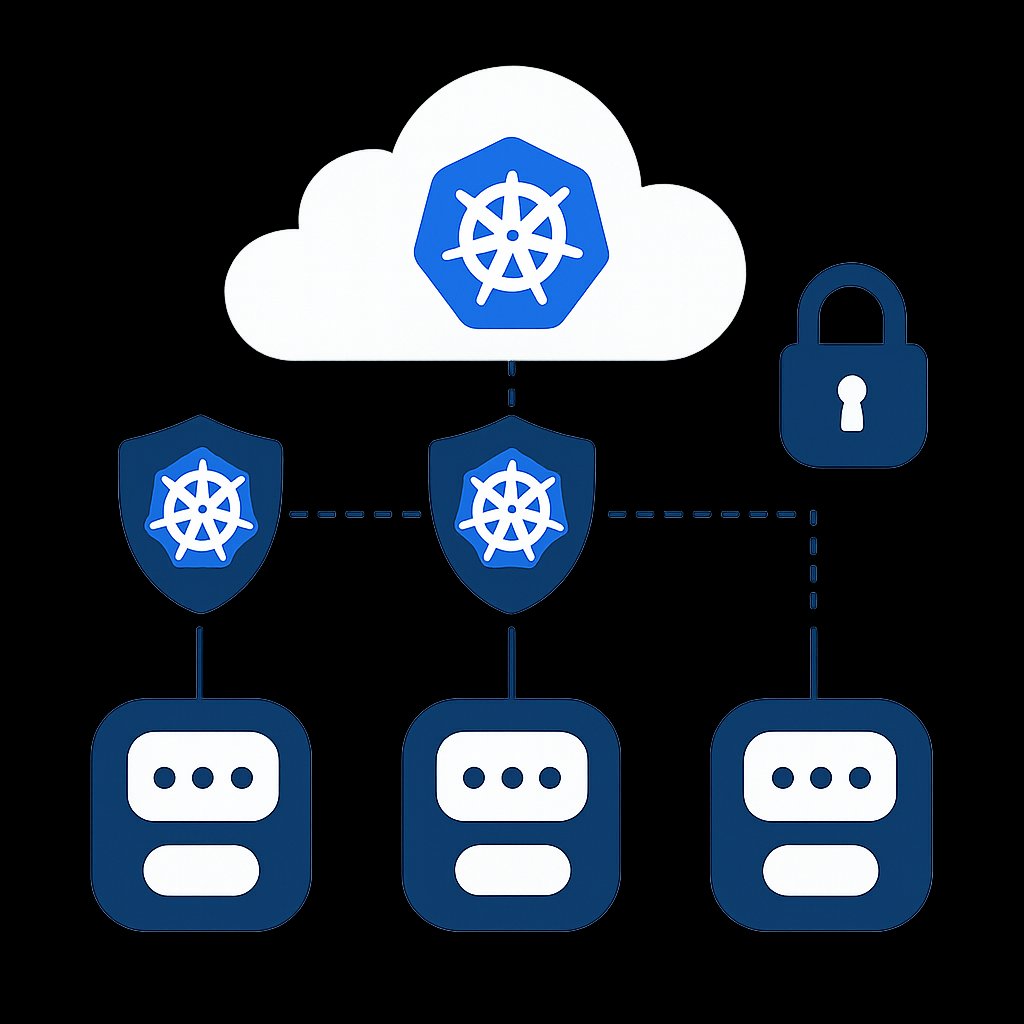
Learn to enforce Kubernetes Pod Security Standards effectively in production environments with real-world strategies and examples.
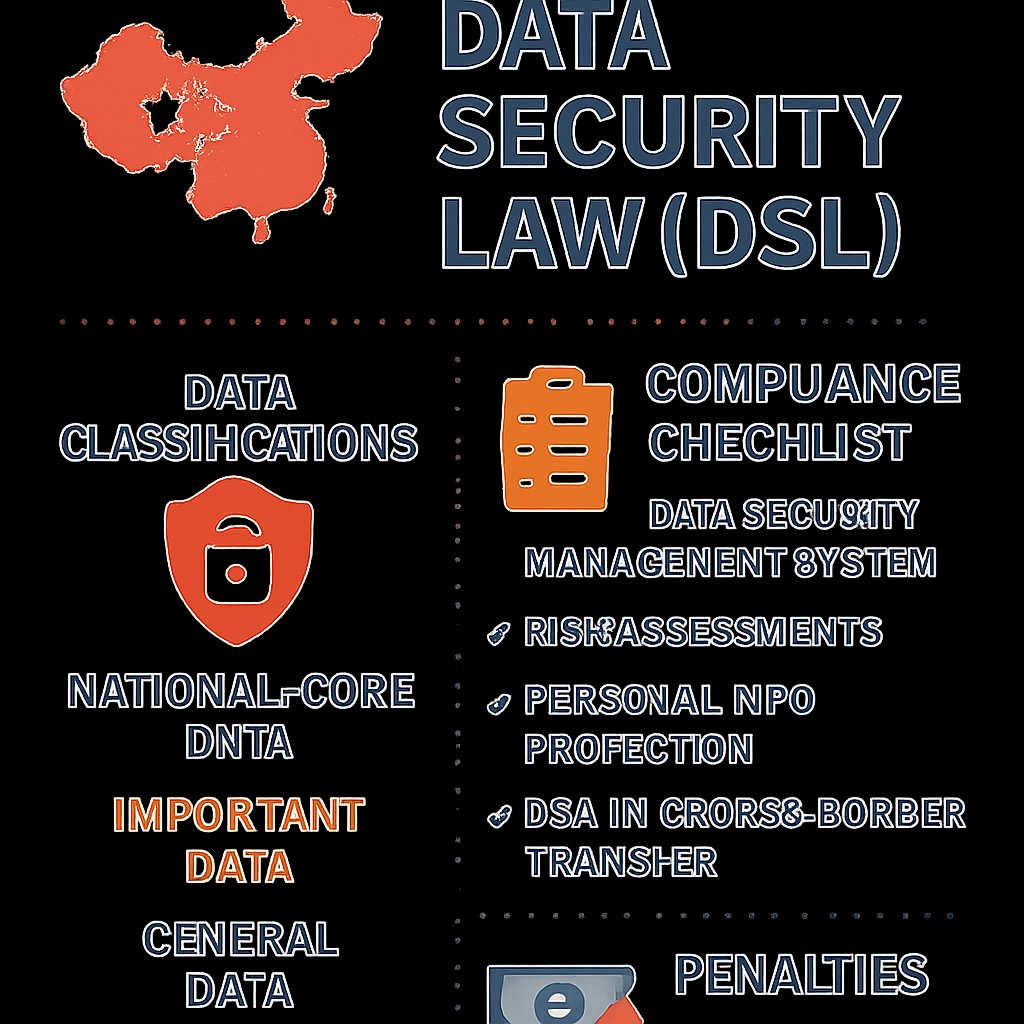
Learn about China’s Data Security Law (DSL), key data classifications, national security reviews, and compliance strategies for foreign companies.

Explore the Great Firewall’s technical workings, its impact on business, and compliant alternatives for Western companies in China.

Explore the rising legal threats in vulnerability disclosure, recent CVE trends, and best practices for responsible reporting.
Discover a powerful Git one-liner found in leaked CIA documents that can enhance your code auditing process and improve source integrity.