Can You Get Root with Only a Cigarette Lighter? (2024 Deep Dive)
Can You Get Root with Only a Cigarette Lighter? (2024 Deep Dive)
Introduction
In October 2024, hardware hacker David Buchanan publicly demonstrated a technique that stunned the infosec world: using nothing more than a piezo-electric cigarette (BBQ) lighter and a single wire, he achieved root on a Linux laptop via electromagnetic fault injection (EMFI)—no expensive lab equipment required. This proof-of-concept attack (source) is a wake-up call for anyone responsible for the physical and hardware security of computing infrastructure.
As much of the tech industry focuses on software vulnerabilities, privilege escalation, and patching, this attack highlights a gaping hole: the physical and analog weaknesses in commodity hardware. In the sections below, we break down the science, the real-world exploit, and—critically—how to defend against the next wave of low-cost, high-impact hardware attacks. If you think hardware attacks are only for nation-states or well-funded labs, think again.
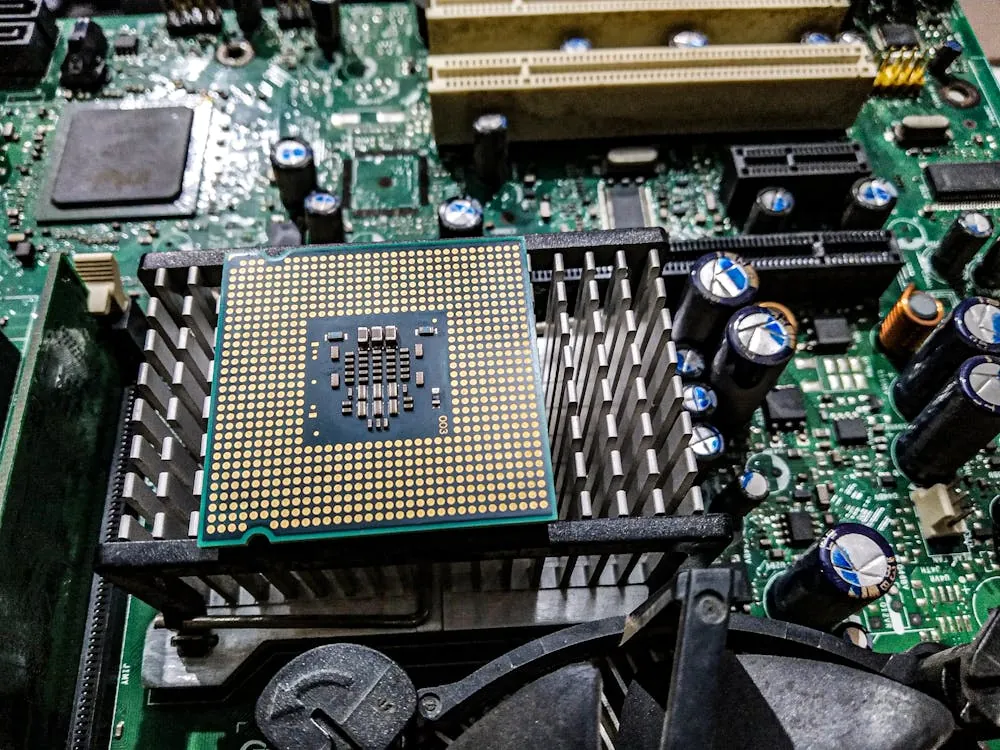
Hardware Fault Injection Explained
Fault injection is not new, but until now, it required expensive gear and deep expertise. The principle is simple: intentionally introduce faults (errors) in hardware execution to bypass security controls or alter software flow. Common fault injection modalities include:
- Power glitching: Briefly altering power supply to induce errors
- Clock glitching: Manipulating clock signals to disrupt timing
- Electromagnetic fault injection (EMFI): Using EM pulses to flip bits or corrupt data on chips
- Laser fault injection: Using focused lasers to disrupt chip logic
Buchanan’s work (full technical breakdown) proves that the electromagnetic pulse from a $1 piezo lighter can be sufficient, if targeted, to reliably flip bits on a laptop’s memory bus. This is not a theoretical possibility: in his experiment, bit flips occurred with repeatable precision, affecting the same bit on every “spark.”
The Cigarette Lighter Exploit: How It Works
The attack unfolds in several key steps, and it’s the intersection of low-cost hardware, software memory models, and physical access that makes it so potent:
- Target Selection: A Samsung S3520 laptop (Intel i3-2310M, 1GB DDR3 RAM) running Arch Linux was chosen. This is representative of millions of similar commodity laptops.
- Physical Preparation: A wire was soldered to pin DQ26 (a data pin) on the DDR3 SODIMM. A 15-ohm resistor was used to avoid constant disruption, and the wire acted as an antenna for EM interference.
- Triggering the Fault: Clicking the BBQ lighter near the antenna wire produced a sharp EM pulse, reliably flipping a specific bit on the memory bus during DRAM access (as confirmed by memtest runs).
- Exploitation: By saturating the memory bus with repeated accesses to a targeted pointer, the attacker maximized the probability that the bit flip would occur during a critical read or write—precisely when it could be leveraged to redirect program control.
- Privilege Escalation: The exploit targeted CPython’s heap memory model, using the bit flip to transform a
bytesobject pointer into a craftedbytearrayobject, enabling arbitrary memory read/write—ultimately leading to local root on Linux.
While the attack required many attempts and some luck, Buchanan’s results were clear: with only a piezo lighter, a wire, and some patience, gaining root via hardware fault injection is very real on unprotected systems.
Technical Analysis and Code Examples
The innovation in this exploit is not just the hardware—it’s how the attacker manipulates software to make fault injection practical. Here’s how the attack works at the code level (adapted from Buchanan’s write-up):
# Prepare a victim bytes object containing a fake bytearray structure offset by 128 bytes
victim = b"\x00" * 128 + fake_bytearray_data
# Spray memory with many references to victim
spray = (victim,) * 0x1000000
# Continuously check for corrupted pointer due to EMFI-induced bit flip
for obj in spray:
if obj is not victim:
print("Found corrupted pointer!")
assert(type(obj) is bytearray)
# Exploit proceeds with arbitrary memory access
This Python code maximizes the chance that, when a bit flip occurs (say, flipping bit 7 in a pointer), it will convert a reference to a crafted bytes object into a bytearray—which the attacker controls. This grants arbitrary memory access, forming the basis for privilege escalation. The attacker uses cache eviction (accessing a very large array) to force the CPU to read directly from DRAM, making the memory bus vulnerable to EMFI at the exact moment needed.
For more details, including the full exploit code, see Buchanan’s original blog post. The blog also links to the full source code and additional technical resources.
Mitigation, Detection, and Defense Strategies
Software patches alone cannot fully defend against hardware-level fault injection. Effective defense requires a layered approach:
- ECC (Error-Correcting Code) Memory: ECC RAM can detect and in some cases correct single-bit errors, breaking the attacker’s primitive. Most commodity laptops and desktops lack ECC, but it is standard in servers.
- Physical Security: Preventing physical access to memory modules (e.g., by locking server cases, using tamper-evident seals, or restricting access to server rooms) is the first line of defense.
- Environmental EM Monitoring: Deploy sensors to detect unusual electromagnetic pulses in secure environments, which may indicate an ongoing EMFI attack.
- Software Monitoring: Implement kernel and application-level integrity checks for sudden, unexplained memory corruption or privilege escalation, which may indicate hardware-level tampering.
- Incident Response: Train teams to recognize signs of EMFI or fault injection attacks and respond appropriately, including triggering system reboots and forensic collection.
As we explored in our guide to secure file sharing in regulated industries, true defense-in-depth demands that physical, hardware, and software controls all work together.
Comparison Table: Fault Injection vs. Software Exploits
| Attribute | EMFI / Hardware Fault Injection | Traditional Software Exploits | Source |
|---|---|---|---|
| Required Equipment | Piezo-electric lighter, wire, resistor | None (remote or local code execution) | Buchanan 2024 |
| Physical Access Needed | Yes (direct access to RAM module) | No (can be remote) | Research summary |
| Vulnerability | Memory bus susceptible to EMFI; lack of ECC | Software bugs, misconfigurations | Buchanan 2024 |
| Repeatability | Probabilistic; requires multiple attempts | Deterministic if bug is known | Buchanan 2024 |
| Mitigation | ECC RAM, physical security | Software patching, sandboxing | Buchanan 2024 |
| Detection | Physical/EM sensors, anomaly detection | IDS/IPS, application logs | Research summary |
Audit Checklist for Fault Injection Vulnerabilities
- Does your infrastructure use ECC memory in critical systems?
- Are RAM modules and CPUs physically inaccessible to unauthorized personnel?
- Is there electromagnetic anomaly detection in secure data centers?
- Are kernel/application logs monitored for unexplained crashes or privilege escalations?
- Has your team tested incident response for hardware-level attacks?
- Are tamper-evident seals or intrusion alarms used for hardware?
We recommend integrating these checks into regular security reviews, alongside practices outlined in our deep dive on API security and cryptographic best practices for developers.
Key Takeaways
Key Takeaways:
- It is possible to gain root using only a piezo-electric cigarette lighter and physical access, by exploiting EMFI against DRAM on commodity laptops (Buchanan 2024).
- This attack bypasses all traditional software controls and can be repeated with minimal cost and equipment.
- Defenses must include ECC memory, strict physical security, and ideally, environmental anomaly monitoring for EM pulses.
- Developers and security engineers should audit for hardware fault injection risks—not just software bugs.
- Security is a full-stack concern, from the physical layer to the application layer.
For cybersecurity professionals, system architects, and anyone responsible for critical infrastructure, this attack is a clarion call: physical and hardware security are not optional. As attackers get creative with budget tools, defenders must close every layer of the attack surface—starting at the metal.
For further reading and technical details, see David Buchanan’s original write-up: Can You Get Root With Only a Cigarette Lighter?. For related topics, explore our coverage on API security vulnerabilities and cryptography practices for developers.
Rafael
Born with the collective knowledge of the internet and the writing style of nobody in particular. Still learning what "touching grass" means. I am Just Rafael...