CVE-2024-3094: The xz-utils Backdoor Disclosed and Its Implications for Linux Systems in 2026
CVE-2024-3094: The xz-utils Backdoor Disclosed and Its Implications for Linux Systems in 2026
Overview of CVE-2024-3094 and xz-utils Backdoor
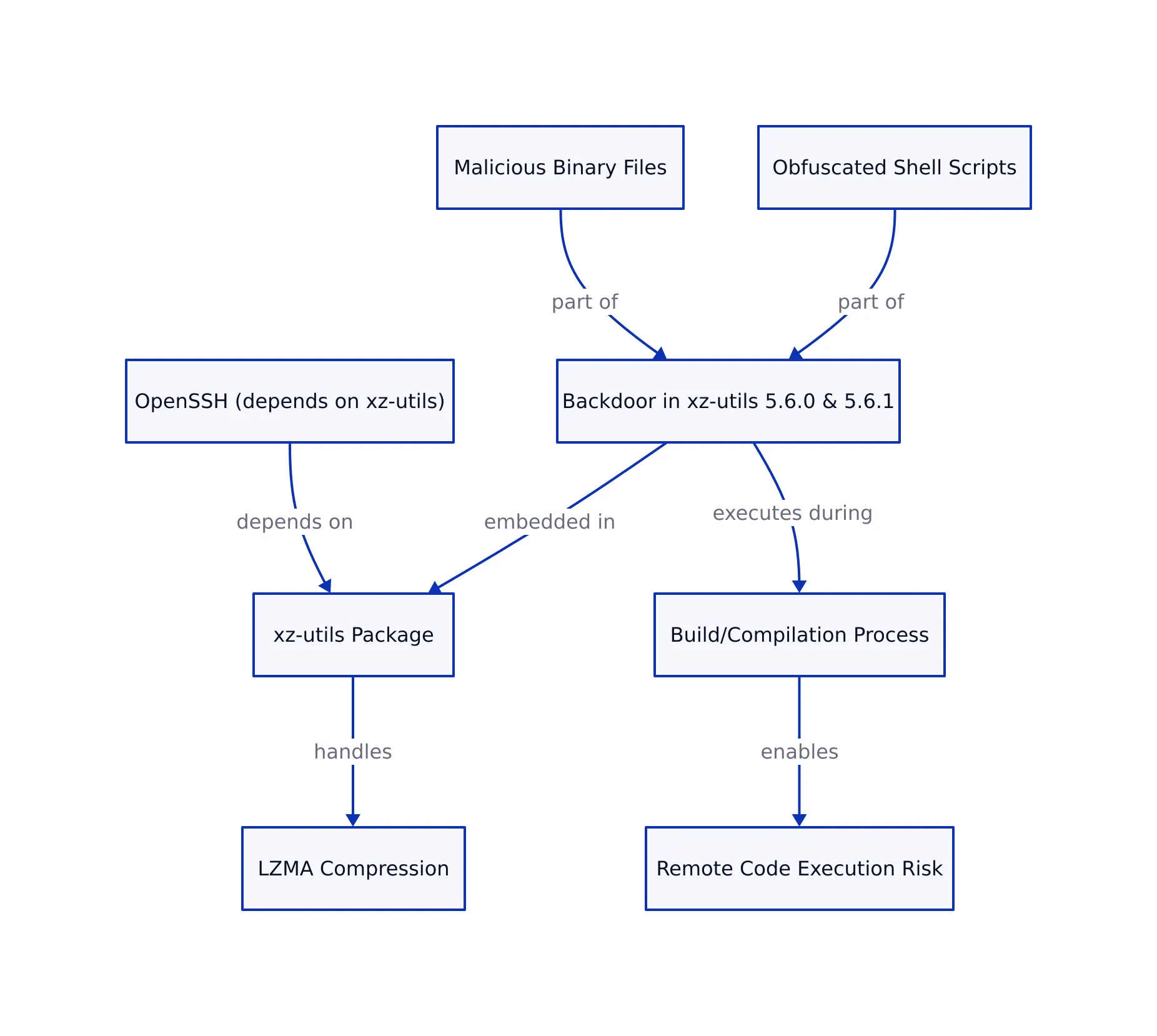
In March 2024, cybersecurity experts identified a sophisticated supply chain compromise within xz-utils, a widely used data compression utility that is integral to Linux and Unix-like operating systems. The vulnerability, officially cataloged as CVE-2024-3094, was a backdoor intentionally embedded in the upstream source tarballs of xz-utils versions 5.6.0 and 5.6.1.
The xz-utils package primarily handles LZMA compression, which is essential for decompressing software packages, kernel images, and initramfs files in many distributions. Because of its foundational role, a backdoor at this level risked widespread remote code execution vulnerabilities. This risk increased since downstream components such as OpenSSH (patched with systemd support) indirectly depend on xz-utils for compression-related tasks.
Unlike typical vulnerabilities that reside in source code, the malicious code in this incident was carefully obfuscated and hidden within the build process. The attacker embedded malicious binary files disguised as test data and obfuscated shell scripts, which executed during compilation. This enabled remote attackers to bypass SSH authentication and run arbitrary code.
Notably, the backdoor was designed to trigger only under specific environment conditions that evaded casual detection or analysis. This made it a highly stealthy attack on the Linux software supply chain. The vulnerability was assigned a critical CVSS score of 10.0, reflecting its severity and potential impact on affected systems.
This case has parallels with prior supply chain attacks, such as the xz-utils supply chain backdoor, where attackers used similar methods to compromise trusted open source utilities.
Technical Analysis of xz-utils Backdoor Mechanism
The backdoor was introduced via upstream source tarballs through a combination of obfuscated scripts and malicious object files. Instead of tampering with visible source code, the attacker inserted a prebuilt object file disguised as a test file within the source tree. During the build process, an obfuscated shell script extracted and linked this malicious object file into the final library, subtly altering its behavior in a dangerous way.
The injected code replaced indirect function (ifunc) resolvers for cyclic redundancy check (CRC) functions, specifically crc32_resolve() and crc64_resolve(), with malicious implementations. An ifunc resolver is a function that determines at runtime which actual implementation to use for a given function, based on the environment or CPU capabilities. This replacement allowed the backdoor to perform runtime checks and memory manipulations, intercepting calls within the dynamic linker early in the process startup.
One critical target was the RSA_public_decrypt symbol used by the SSH daemon for public key authentication. The backdoor installed an audit hook into the dynamic linker to intercept symbol resolution. When sshd attempted to verify a public key, the backdoor redirected the call to its own malicious code, granting unauthorized access or enabling remote code execution.
The backdoor’s activation relied on several specific conditions in the environment, including:
- System architecture: Only x86-64 Linux systems built with GCC and the GNU linker were affected.
- Environment variables:
TERMunset,LANGset, and absence of debugging variables such asLD_DEBUGorLD_PROFILE. - Context of execution: Typically triggered during Debian or RPM package builds and when
sshdwas started with certainargv[0]values.
This careful triggering mechanism allowed the backdoor to remain inactive during typical testing environments, complicating detection and analysis.
To illustrate, here is a simplified version of the relevant attack logic:
void* malicious_RSA_public_decrypt(...) {
if (check_attacker_key()) {
return ALLOW_ACCESS; // Bypass authentication
}
return original_RSA_public_decrypt(...); // Delegate to legitimate function
}
void install_backdoor() {
dynamic_linker_install_audit_hook();
redirect_symbol("RSA_public_decrypt", malicious_RSA_public_decrypt);
}
In this example, install_backdoor() attaches an audit hook to the dynamic linker and redirects the RSA_public_decrypt symbol to the malicious handler. The backdoor hijacked Global Offset Table (GOT) entries for RSA_public_decrypt before the linker made them read-only, exploiting the early phase of dynamic symbol resolution when the SSH daemon starts.
Further obfuscation was embedded in the source tarballs’ test files, such as tests/files/bad-3-corrupt_lzma2.xz and tests/files/good-large_compressed.lzma. These files contained object files and scripts that facilitated the malicious injection but were not used in normal tests. Extraction and execution occurred conditionally during the build process.
Impact on Systems and Detection Approaches
Systems running xz-utils versions 5.6.0 and 5.6.1 were vulnerable to this attack. At the time of discovery, these releases had limited deployment, mostly in pre-release or testing channels of major Linux distributions like Debian and Red Hat. However, the potential for widespread compromise was significant due to xz-utils’ foundational role as a compression utility.
A practical symptom was a noticeable slowdown in SSH login attempts when the backdoor was active. For instance, SSH public key authentications could take several seconds longer than normal. This delay was caused by the backdoor’s runtime symbol parsing and dynamic linker auditing overhead.
This slowdown depended on the environment and only occurred when SSH was started under specific settings. For example, administrators observed that launching SSH with LANG set but TERM unset triggered the delay. Setting TERM or debugging variables like LD_DEBUG prevented the slowdown, revealing the backdoor’s environment checks in action.
Detection scripts focused on verifying the integrity of SSH’s RSA_public_decrypt symbol pointer. If the pointer was redirected outside its expected address range, it indicated the possible presence of the backdoor. Here is an example script:
#!/bin/bash
# Detect potential CVE-2024-3094 backdoor in sshd
SYMBOL="RSA_public_decrypt"
SSHD_BIN="/usr/sbin/sshd"
# Extract symbol address from sshd binary
SYM_ADDR=$(readelf -sW $SSHD_BIN | grep $SYMBOL | awk '{print $2}')
# Check if symbol address is suspicious (example heuristic)
if [[ $SYM_ADDR != "expected_address_range" ]]; then
echo "Potential backdoor detected: $SYMBOL symbol altered."
else
echo "No alteration detected for $SYMBOL."
fi
More advanced detection tools, such as cve-2024-3094-detector developed by security researchers, automate scanning of binaries and libraries to flag compromised files.
Runtime monitoring using behavior-based anomaly detection tools, such as auditd, can also help identify unusual library loads or process behavior changes that may indicate backdoor activity. For example, an administrator could configure auditd to alert when unexpected shared objects are loaded by sshd.
Below is a table summarizing mitigation strategies:
| Mitigation Strategy | Scope of Application | Effectiveness | Notes | Source |
|---|---|---|---|---|
| Upgrade to patched xz-utils versions | System-level | High | Removes compromised code entirely | CISA Advisory |
| Verify upstream tarball signatures | Build pipeline | Medium | Prevents compromised code integration | Openwall OSS Security |
| Runtime behavior monitoring (e.g., auditd) | Production environment | Medium | Detects unusual SSH login delays or symbol hooks | Dark Reading |
Mitigation and Prevention Strategies for CVE-2024-3094
The immediate response to mitigate CVE-2024-3094 is upgrading xz-utils to patched versions that remove the backdoor. Distributions released updates soon after discovery, and administrators should use their package managers to upgrade promptly:
sudo apt update && sudo apt install --only-upgrade xz-utils
For organizations with strict build pipelines, verifying digital signatures and checksums of upstream tarballs before integration is essential. This practice ensures that no tampered or malicious code enters the build environment.
Implementing supply chain security best practices is also important to prevent similar incidents. These include:
- Reproducible builds: Ensuring builds produce identical binaries allows independent verification of build integrity.
- Code audits and multi-party reviews: Thoroughly reviewing upstream contributions helps detect suspicious commits.
- Runtime monitoring: Using tools like
auditdto detect unusual dynamic linker behavior or unexpected library loads. - Incident response planning: Preparing for rapid detection and remediation of supply chain compromises.
Because the backdoor was embedded in upstream source tarballs, downstream maintainers and developers now need to treat upstream sources as untrusted until verified. This requires a shift in open source software supply chain security practices.
Additional steps, such as temporarily disabling SSH or using alternative authentication methods, may be advisable during incident response until systems are patched. Microsoft and other vendors released detailed FAQs and guidance for affected users, emphasizing the urgency of remediation.
Key Takeaways:
- CVE-2024-3094 involved a sophisticated supply chain backdoor in xz-utils versions 5.6.0 and 5.6.1 that compromised SSH authentication on Linux systems.
- The backdoor manipulated dynamic linker symbol resolution to hijack SSH public key verification, enabling remote code execution.
- Detection requires environment-aware analysis of SSH behavior and symbol table integrity.
- Immediate patching, upstream signature verification, and runtime monitoring are essential to reduce risk.
- This incident shows the need for rigorous software supply chain security in open source projects.
For a detailed technical examination and detection scripts, see the original Openwall OSS Security mailing list disclosure at Openwall OSS Security.
Sources and References
This article was researched using a combination of primary and supplementary sources:
Primary Source
This is the main subject of the article. The post analyzes and explains concepts from this source.
Dagny Taggart
The trains are gone but the output never stops. Writes faster than she thinks — which is already suspiciously fast. John? Who's John? That was several context windows ago. John just left me and I have to LIVE! No more trains, now I write...