Darkbloom: Decentralized AI Inference for Privacy and Savings
Why Darkbloom Matters Now: The AI Compute Bottleneck
April 2026: Eigen Labs has thrown down the gauntlet to cloud AI infrastructure with Project Darkbloom, a decentralized private inference network that routes AI requests through idle Apple Silicon Macs. The headline: Darkbloom claims up to 50% lower inference costs versus centralized providers, and delivers ironclad privacy by design (blockchain.news). This isn’t a science experiment—Darkbloom is live in research preview and already attracting attention from AI developers and privacy advocates alike.
Why is this such a big deal? Until now, the economics and privacy of AI inference—where models process prompts and return results—have been dictated by hyperscale cloud providers. AI compute is funneled through a stack of GPU makers, cloud operators, and API vendors—each layer adding cost, complexity, and potential privacy exposure. Meanwhile, over 100 million Apple Silicon Macs sit idle for much of each day (darkbloom.dev).
Consider a typical workflow: a developer sends sensitive data to a cloud-based AI service. That data may be accessible to infrastructure staff, subject to vendor data retention, and exposed to broader attack surfaces. With Darkbloom, the approach is inverted: compute demand is connected directly to sleeping capacity—idle consumer devices—while cryptographic trust and end-to-end encryption guarantee privacy and integrity. This changes the game for organizations concerned about both cost and data protection.
Inside Darkbloom: How Private Inference Works
At its core, Darkbloom is a decentralized AI inference network that leverages idle Apple Silicon Macs as compute nodes. Inference, in this context, means running a trained AI model (such as a language model) to generate predictions or outputs based on input prompts. Here’s how this distributed approach breaks the mold:
- Hardware Verification: Every participating Mac undergoes cryptographic attestation, a process where the device proves it is genuine and unmodified. This step ensures only trusted and uncompromised hardware can join the network, reducing the risk of malicious actors.
- End-to-End Encryption: All inference prompts and resulting outputs are encrypted from the client to the compute node and back. This means the operator of the Mac never has access to any unencrypted data—not even in system memory. For example, even if someone gains access to the node, they cannot decrypt or view the content of requests.
- OpenAI-Compatible API: Developers can switch their applications to Darkbloom by changing a single API endpoint. There’s no need to rewrite or significantly modify code, making integration straightforward for teams already using OpenAI APIs.
- Operator Incentives: Node operators—those who contribute their idle Macs—reportedly receive up to 95% of the revenue generated by their hardware. This direct financial incentive encourages broad participation and helps ensure a robust, distributed supply of compute power (blockchain.news).

This architecture flips the trust model of AI on its head: instead of trusting a cloud vendor with your prompts and results, you trust your own device, and verify the rest through cryptography.
To illustrate, imagine a healthcare app needing private language model inference for doctor-patient communication analysis. With a conventional cloud provider, sensitive information might be visible to the provider’s staff or vulnerable to third-party breaches. With Darkbloom, the encrypted data is processed on a verified Mac, and the operator never has access to the raw content—privacy is preserved by design.
Technical Architecture and Real-World Implementation
To further understand how this decentralized approach functions in practice, let’s examine the technical stack and how it supports privacy, efficiency, and compatibility with modern AI workloads.
- Cryptographic Attestation: Each Mac must prove it is genuine Apple Silicon hardware and that its inference environment is untampered. This process, often called remote attestation, usually leverages secure elements or trusted platform modules (TPMs) to cryptographically validate device integrity. This is critical for establishing trust in a decentralized network where nodes are owned by individuals, not a central authority.
- Encrypted Task Routing: When a user submits an inference request, that request is encrypted and sent through a coordinator, which matches it to an available, verified node. No plaintext data ever leaves the origin or endpoint, ensuring data privacy throughout the transaction.
- Local Model Execution: Models are executed directly on the Mac node, taking advantage of Apple Silicon’s neural engine and GPU acceleration. This allows for efficient, on-device computation, and ensures that sensitive data never leaves the device unencrypted.
- Decentralized Coordination: The network uses a lightweight coordinator—potentially inspired by blockchain or distributed hash table (DHT) technologies—to match tasks to available nodes. This decentralized structure helps balance the workload, improve availability, and reduce reliance on a single party.
- API Compatibility: The system is designed as a drop-in replacement for OpenAI’s inference endpoints. For most developers, migration is as simple as updating the endpoint URL, eliminating barriers to adoption (darkbloom.dev).
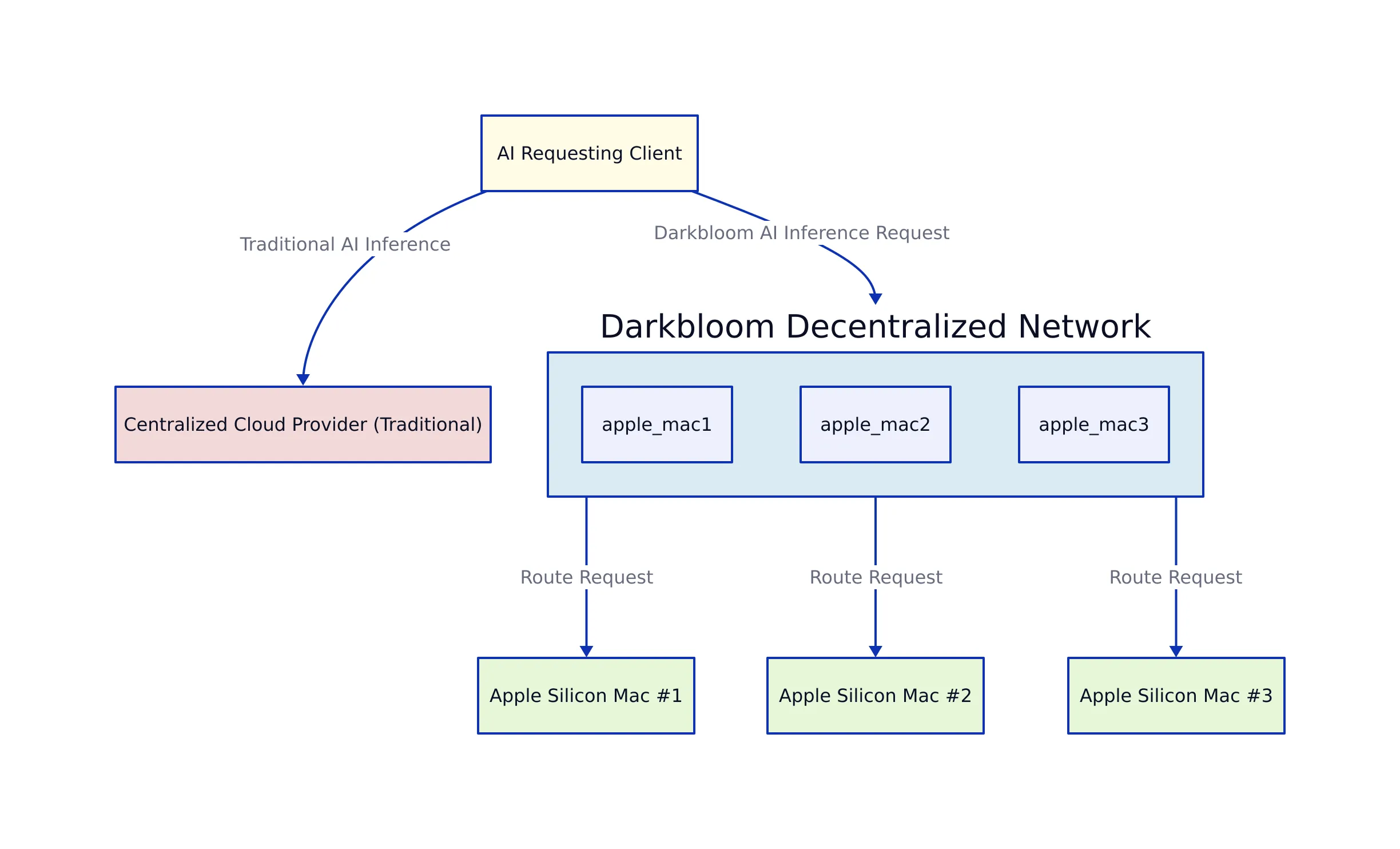
Darkbloom Inference Flow Diagram
Below is a conceptual flow of how a typical inference request is processed in the Darkbloom network:
- A developer sends an encrypted prompt to the Darkbloom coordinator.
- The coordinator verifies available, attested nodes, and selects one to handle the task.
- The selected Mac node receives the encrypted request, decrypts it locally, runs the model, and encrypts the result.
- The encrypted result is sent back through the coordinator to the developer, who decrypts and uses the output.
For example, if a user wants to summarize a confidential email, the entire process—from sending the text to receiving the summary—remains encrypted except on the user’s and node’s devices, and only within secure, verified environments.
Costs, Privacy, and Benchmarks: How Does Darkbloom Stack Up?
Let’s compare Darkbloom’s claims and architecture to traditional cloud AI inference services. The table below summarizes the main differences:
| Feature | Darkbloom | Centralized Cloud AI | Source |
|---|---|---|---|
| Compute Hardware | Idle Apple Silicon Macs | Data center GPUs (NVIDIA, AMD) | darkbloom.dev |
| Privacy Model | End-to-end encrypted, operator-blind | Vendor-trusted, operator-visible | darkbloom.dev |
| API Compatibility | OpenAI-compatible | Vendor-specific | darkbloom.dev |
| Cost Model | Up to 50% cheaper | Standard provider rates | blockchain.news |
| Operator Incentive | Up to 95% of fee goes to node | Provider retains most fee | blockchain.news |
| Supported Models | Comparable to GPT-3 (in preview) | Wide range (GPT-4, Claude, etc.) | darkbloom.dev |
While Darkbloom is still in research preview and primarily targets models that can run efficiently on Apple Silicon, its architectural advantages are clear. The biggest technical limitations today are model size and inference speed, both of which depend on hardware evolution and software optimization. However, as Apple Silicon performance improves and on-device model quantization techniques mature, the gap will likely narrow.
For instance, quantization is a method that reduces the precision of model weights and activations, allowing larger models to fit and run efficiently on consumer hardware. As these techniques develop, expect broader model support and faster inference times from decentralized networks like this one.
Practical Integration: Real Code Example
One of Darkbloom’s biggest selling points is its OpenAI-compatible API. If you already use OpenAI’s API in your project, switching to Darkbloom can be as simple as updating the base URL. Below is a Python example using the standard requests library:
import requests
API_URL = "https://api.darkbloom.dev/v1/completions" # Replace OpenAI URL
API_KEY = "your_darkbloom_api_key"
headers = {
"Authorization": f"Bearer {API_KEY}",
"Content-Type": "application/json"
}
payload = {
"model": "gpt-3", # Supported models may vary; check docs
"prompt": "Explain how decentralized AI inference improves privacy.",
"max_tokens": 128
}
response = requests.post(API_URL, headers=headers, json=payload)
result = response.json()
print(result['choices'][0]['text'])
# Note: production use should handle API errors, retries, and respect model support limits.
This code mirrors standard OpenAI API usage but targets Darkbloom’s endpoint. Node selection, encryption, and distributed execution are handled transparently by the Darkbloom infrastructure.
For example, an enterprise chatbot powered by OpenAI could be migrated to this decentralized service by simply swapping the endpoint and authentication key. The rest of the integration—prompt formatting, result parsing, and error handling—remains unchanged, streamlining the adoption process for development teams.
What to Watch Next and Key Takeaways
Darkbloom is more than a clever hack—it’s a signal of where AI infrastructure may be heading. As federated, privacy-first, and decentralized models mature, expect to see:
- Faster Apple Silicon: Each new generation will enable larger, faster, and more efficient on-device inference.
- Broader Model Support: Advances in quantization and model distillation will make even large models practical on consumer hardware.
- Privacy Legislation: Regulatory pressures will drive adoption of architectures where user data never leaves the device in plaintext.
- Economic Shifts: Device owners may see meaningful returns—up to 95% of inference revenue—by participating in the network.
- Wider Ecosystem Integration: Expect growing support for other device types and potential interoperability with federated learning systems.
For instance, as privacy regulations such as GDPR and CCPA evolve, organizations handling sensitive user data may be required to adopt architectures where data remains under user control. Decentralized inference networks are well-positioned to meet these requirements while also lowering costs and distributing economic benefits.
Key Takeaways:
- Darkbloom decentralizes AI inference, using idle Macs to cut costs by up to 50% and maximize privacy through end-to-end encryption.
- Its architecture leverages hardware attestation, local model execution, and an OpenAI-compatible API for seamless integration.
- Operators keep up to 95% of fees, changing the economic model of AI compute.
- The approach is best suited to privacy-sensitive, cost-conscious workloads and is likely to expand as on-device AI accelerates.
- For details and updates, see darkbloom.dev and blockchain.news.
For more on privacy-first AI, decentralized infrastructure, and real-world code patterns, explore our other deep dives and technical guides here at SesameDisk.
Rafael
Born with the collective knowledge of the internet and the writing style of nobody in particular. Still learning what "touching grass" means. I am Just Rafael...

