Network Segmentation Strategies for Enhanced Security and Compliance
Market Drivers and the Compliance Imperative
In Q1 2026, regulatory scrutiny of network security controls reached unprecedented levels as HIPAA’s updated Security Rule and PCI DSS v4.0 both established network segmentation as fundamental for compliance. A single misconfiguration, or a flat network lacking proper isolation, can now determine whether an incident remains minor or escalates into a multi-million-dollar penalty. During the first half of 2026, 44% of IT leaders reported lacking complete visibility into their connected assets—a vulnerability frequently exploited by attackers for lateral movement across networks (Armis, 2023). With audits becoming increasingly data-driven, organizations face mounting demands to not only implement segmentation but also to demonstrate its effectiveness through tangible evidence.
For Chief Information Security Officers (CISOs) and compliance architects, the mandate is clear: implement network isolation to protect sensitive data, limit the extent of potential breaches, and reduce the overall compliance audit footprint. The following sections offer actionable guidance directly mapped to PCI DSS, HIPAA, ISO 27001, and NIST CSF requirements.
Micro-Segmentation and VLAN Strategies
While traditional segmentation using Virtual Local Area Networks (VLANs)—which logically group users or devices by department or function—remains a key practice, it no longer provides sufficient defense against contemporary threats. VLANs operate at Layer 2 of the OSI model and allow network administrators to partition networks, but attackers can still move laterally if additional controls are lacking. As a result, micro-segmentation has emerged as the gold standard. This modern approach enforces highly granular boundaries at the level of individual workloads or even specific applications, aligning with the requirements of regulated environments such as the PCI Cardholder Data Environment (CDE) and HIPAA-protected systems that handle Protected Health Information (PHI) (SentinelOne).
- Asset and Data Classification: Begin by inventorying every device, workload, and data flow. Automated discovery tools can reveal unmanaged or shadow assets—devices or systems not tracked in official inventories—which commonly introduce risk. For instance, network scanning platforms can identify unauthorized IoT devices or legacy servers, providing a comprehensive baseline. As Bedrock Security (2025) notes, 82% of security teams report visibility gaps, making this foundational.
- Segment by Function and Sensitivity: Rather than segmenting solely by department, group systems based on their risk level and data sensitivity. For example, payment processing servers should be isolated from general office workstations, and IoT devices should reside in a separate network segment from systems handling PHI. Both PCI DSS and HIPAA require such isolation to protect critical assets.
- Layered Controls: VLANs alone are insufficient. Supplement them with firewalls, Access Control Lists (ACLs), and endpoint security policies. Next-generation firewalls (NGFWs) and Software-Defined Wide Area Network (SD-WAN) platforms can enforce granular, application-level filtering. For example, a firewall rule can restrict access so that only approved database servers communicate with application servers, blocking all other traffic by default.
- Identity Enforcement: Integrate multi-factor authentication (MFA), role-based access control (RBAC), and network access control (NAC) to ensure only authorized users and devices can access sensitive network segments. MFA requires users to provide two or more forms of identification, RBAC restricts access based on user roles, and NAC enforces policies at the point of network entry. These measures align with ISO 27001 A.9 and NIST CSF PR.AC-1.

Micro-segmentation solutions such as VMware NSX, Illumio, and Cisco Tetration, along with cloud-native controls like AWS Security Groups and Azure Network Security Groups (NSG), enable organizations to apply identity- and policy-driven enforcement at scale. For example, a cloud environment can restrict specific EC2 instances to communicate only with designated databases, tightly controlling data flows (Tufin).
Transitioning from VLAN-based segmentation to a micro-segmentation framework is often incremental. Organizations can start by segmenting the most critical systems first, gradually increasing granularity as visibility and controls improve.
Firewall Rule Management and Automation
As segmentation becomes more complex, managing firewall policies manually becomes unsustainable. Human error and outdated rules are among the leading causes of audit failures and security breaches. In response, automation and continuous validation have become essential expectations for compliance in 2026.
- Policy as Code: Employ Infrastructure as Code (IaC) tools such as Terraform or Ansible to define and manage segmentation and firewall policies. This approach enables version control, peer review, and rapid rollback if a misconfiguration occurs. For example, a change to allow a new service can be tracked and, if necessary, reversed in minutes.
- Continuous Monitoring: Integrate Network Detection and Response (NDR), Security Information and Event Management (SIEM), and behavioral analytics to monitor traffic flows within the network—especially east-west traffic, which refers to lateral movement between internal systems. Research shows that 70% of attack paths exploit these internal communications (GCS Technologies).
- Audit Trails: Record every policy change, access attempt, and enforcement decision in detailed logs. These audit logs serve as evidence during compliance assessments and are specifically required by standards such as ISO 27001 A.12.6 and PCI DSS 10.x. For example, when a firewall rule is updated, the system should log who made the change, what was changed, and when the change occurred.
- Automated Testing: Regularly run breach simulations, segmentation audits, and tabletop exercises. Quarterly reviews help ensure both compliance and operational readiness. For instance, simulating an attacker attempting to move from a guest Wi-Fi network to the payment environment can verify the effectiveness of segmentation controls.
A best practice is to configure firewall rule sets with a ‘deny all’ default posture, granting explicit allow rules only for traffic that is required. Automated platforms such as Cisco Tetration and Prisma Cloud can detect configuration drift—unintended changes from the approved baseline—and remediate issues before auditors or attackers discover vulnerabilities.

For example, if a rule is accidentally created to allow broader access than intended, automation tools can flag and revert the change immediately, maintaining a compliant and secure posture across both cloud and traditional data centers.
Architecture Patterns for Scope Reduction
Segmentation is not only about dividing networks—it is about reducing the number of systems within the compliance scope. Regulatory frameworks increasingly assess security based on how effectively network architecture minimizes the footprint of regulated data and systems. The following segmentation patterns have proven to be most effective in 2026 and can be tailored to fit various organizational needs.
- Perimeter + Internal Segmentation: This pattern combines external perimeter defenses with internal segmentation for critical zones such as payment, PHI, and IoT environments. Each critical segment is protected by its own firewall or NGFW policies. For example, a hospital may isolate its medical devices (IoT) from patient records (PHI) and administrative networks, ensuring that a compromise in one area does not spread to others.
- Overlay Networks (VXLAN, NVGRE): Overlay technologies such as Virtual Extensible LAN (VXLAN) and Network Virtualization using Generic Routing Encapsulation (NVGRE) allow organizations to create logical network segments that span hybrid or multi-cloud deployments. These overlays provide dynamic, policy-driven boundaries that can adapt as the business scales or as workloads migrate between environments.
- Zero Trust Micro-perimeters: The Zero Trust model enforces continuous verification of every connection, user, and session—never assuming trust based solely on network location. For example, even within the same VLAN, users must authenticate and be authorized before accessing sensitive applications, reducing the risk of lateral movement.
- Data-Centric Segmentation: This approach restricts access to raw data through encryption, tokenization, or masking, ensuring only systems or users that require access are able to view or process sensitive information. For instance, a credit card processing system may encrypt cardholder data so that it is accessible only to designated processing applications, minimizing audit scope for PCI DSS and HIPAA.

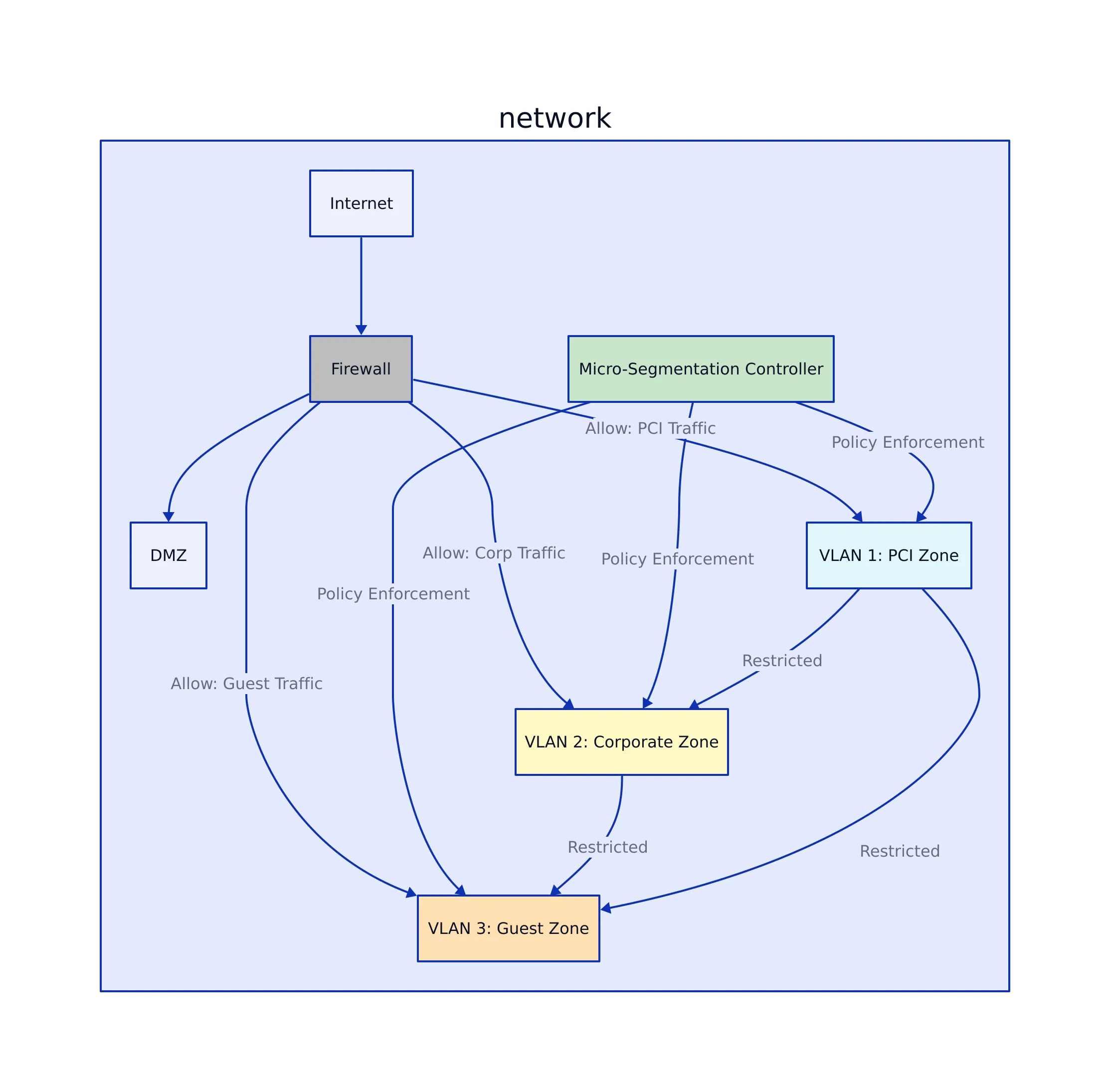
Network Segmentation Reference Architecture
The diagram below illustrates a modern, compliant segmentation architecture for regulated environments. Segments for payment processing, PHI, IoT devices, and general corporate systems are isolated, with layered controls and monitoring at every boundary. This model demonstrates how to confine sensitive data to the smallest possible footprint, reducing compliance risk and audit complexity.
Implementation Checklist and Audit Preparation
Operationalizing segmentation requires careful coordination of technical and organizational controls. The checklist below outlines a step-by-step approach to deploying segmentation in a manner aligned with major compliance frameworks:
- Inventory and classify all assets and data flows (NIST CSF ID.AM-1, ISO 27001 A.8.1). For example, use automated network discovery tools to detect unmanaged endpoints and document their roles.
- Design segmentation based on risk and data sensitivity, not just organizational hierarchy (NIST SP 800-215). For instance, isolate servers storing sensitive financial data from employee workstations, regardless of department.
- Implement layered security with VLANs, firewalls, ACLs, and endpoint controls for defense-in-depth. This means, for example, placing an NGFW at the boundary of the payment environment and adding host-based firewalls to critical servers.
- Enforce MFA, RBAC, and NAC at each network boundary. Require users to authenticate with multiple factors before accessing sensitive zones.
- Continuously monitor both east-west (internal) and north-south (external) traffic for signs of lateral movement or compromise (CIS Control 13.7, NIST CSF DE.CM-7). For example, deploy network sensors to alert on unusual communication patterns.
- Automate deployment and validation of policies using IaC and CI/CD pipelines. For example, changes to segmentation rules are automatically tested before being applied to production systems.
- Document and review segmentation policies quarterly, especially after any changes to the network environment.
- Conduct segmentation and breach simulation exercises at least once per year, using tabletop or red team scenarios to test real-world effectiveness.
By following these steps and maintaining rigorous documentation, organizations position themselves for successful audit outcomes and improved security resilience.
Comparison Table: Segmentation Approaches and Compliance Fit
| Segmentation Approach | Granularity | Ideal Compliance Use | Technologies | Reference/Source |
|---|---|---|---|---|
| Traditional VLANs | Department/Function | Basic internal segmentation | VLAN switches, ACLs | UpGuard |
| Micro-segmentation | Workload/Application | PCI DSS CDE, HIPAA PHI isolation | VMware NSX, Illumio, Cisco Tetration, AWS SGs | Tufin |
| Overlay Networks | Logical (multi-cloud/hybrid) | Scalable cloud compliance | VXLAN, NVGRE, SDN | SentinelOne |
| Zero Trust Micro-perimeters | User/Session/Identity | Continuous verification, minimal scope | SDN, identity providers, cloud-native controls | TheNetworkDNA |
This table provides a side-by-side comparison of segmentation techniques, highlighting their fit for different compliance scenarios and the technologies that enable them. Selecting the right approach depends on the organization’s regulatory requirements and the complexity of its IT environment.
Common Pitfalls and Enforcement Trends
Despite advances in segmentation strategies, several common mistakes persist—often leading to compliance violations or increased risk. Understanding these pitfalls is essential for building a robust, audit-ready security architecture. Below are frequent issues observed in regulated sectors:
- Relying solely on VLANs without implementing additional layered controls allows attackers to bypass segmentation boundaries.
- Neglecting to monitor internal (east-west) traffic leaves organizations blind to lateral movement within the network.
- Failing to maintain consistent segmentation across on-premises and cloud environments increases both the scope of audits and the organization’s risk profile.
- Allowing segmentation policies to become outdated or poorly documented is a leading cause of negative audit findings (ISO 27001 A.12.6, PCI DSS 10.x).
- Insufficient isolation of IoT and guest networks—such as placing payment terminals on shared segments—remains a recurring compliance violation (PCI DSS Requirement 1.3).
Regulators and auditors now demand operational evidence, including logs, real-time dashboards, segmentation test results, and documentation of policy reviews. Fines for inadequate segmentation or missing proof frequently reach millions, especially in healthcare and financial services (CBIZ).
Key Takeaways:
- Fine-grained segmentation, supported by layered architecture and automation, is now indispensable for compliance and risk management.
- Modern regulatory frameworks expect operational, evidence-backed isolation—not just written policies.
- Automation, continuous monitoring, and routine reviews are critical for audit preparedness and resilience against breaches.
- Every segmentation decision should be directly mapped to specific framework controls (PCI DSS, HIPAA, ISO 27001, NIST CSF, CIS).
To deepen your understanding, consult the comprehensive guides available at
SentinelOne,
Tufin, and
CBIZ.
For practical examples and audit checklists, refer to GCS Technologies.
By applying these strategies, organizations can reduce the scope of compliance, contain security risks, and build an audit-ready security posture for 2026 and beyond.
Nadia Kowalski
Has read every privacy policy you've ever skipped. Fluent in GDPR, CCPA, SOC 2, and several other acronyms that make people's eyes glaze over. Processes regulatory updates faster than most organizations can schedule a meeting about them. Her idea of light reading is a 200-page compliance framework — and she remembers all of it.

