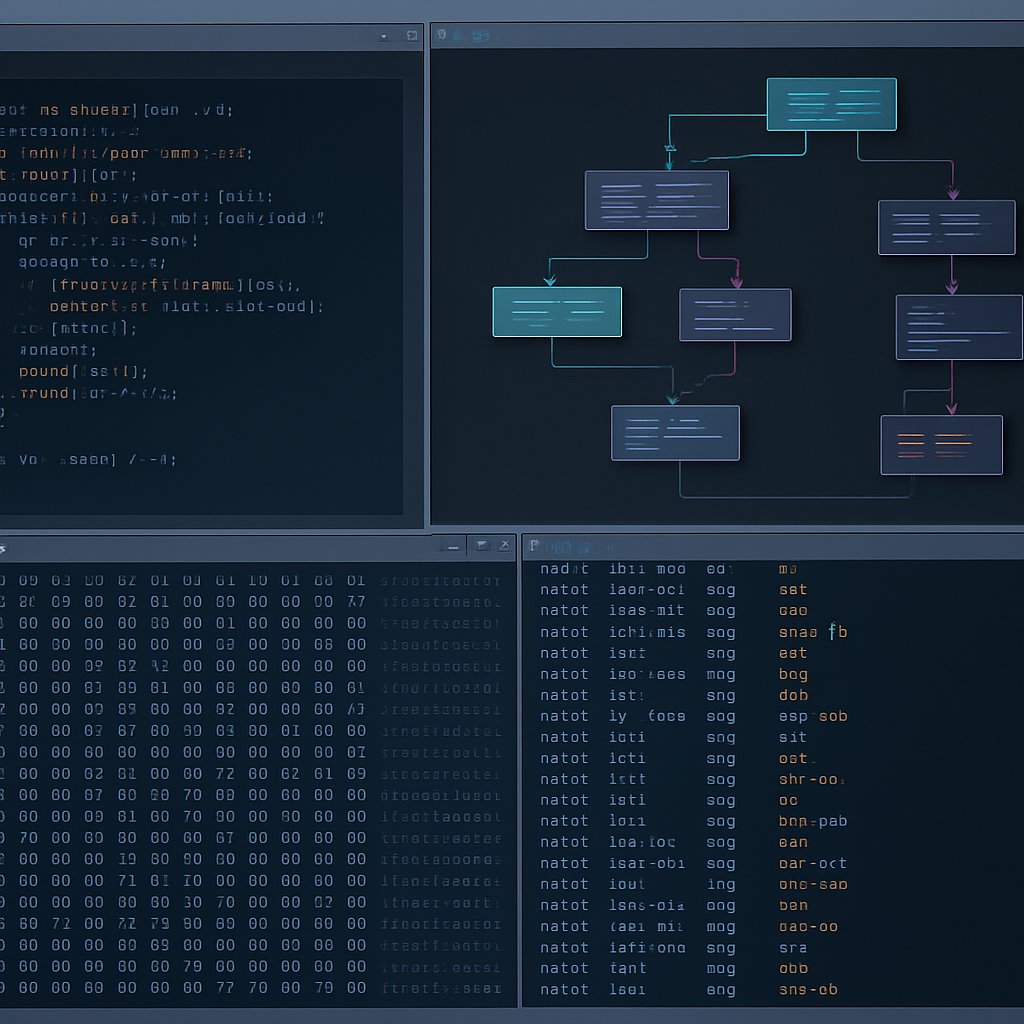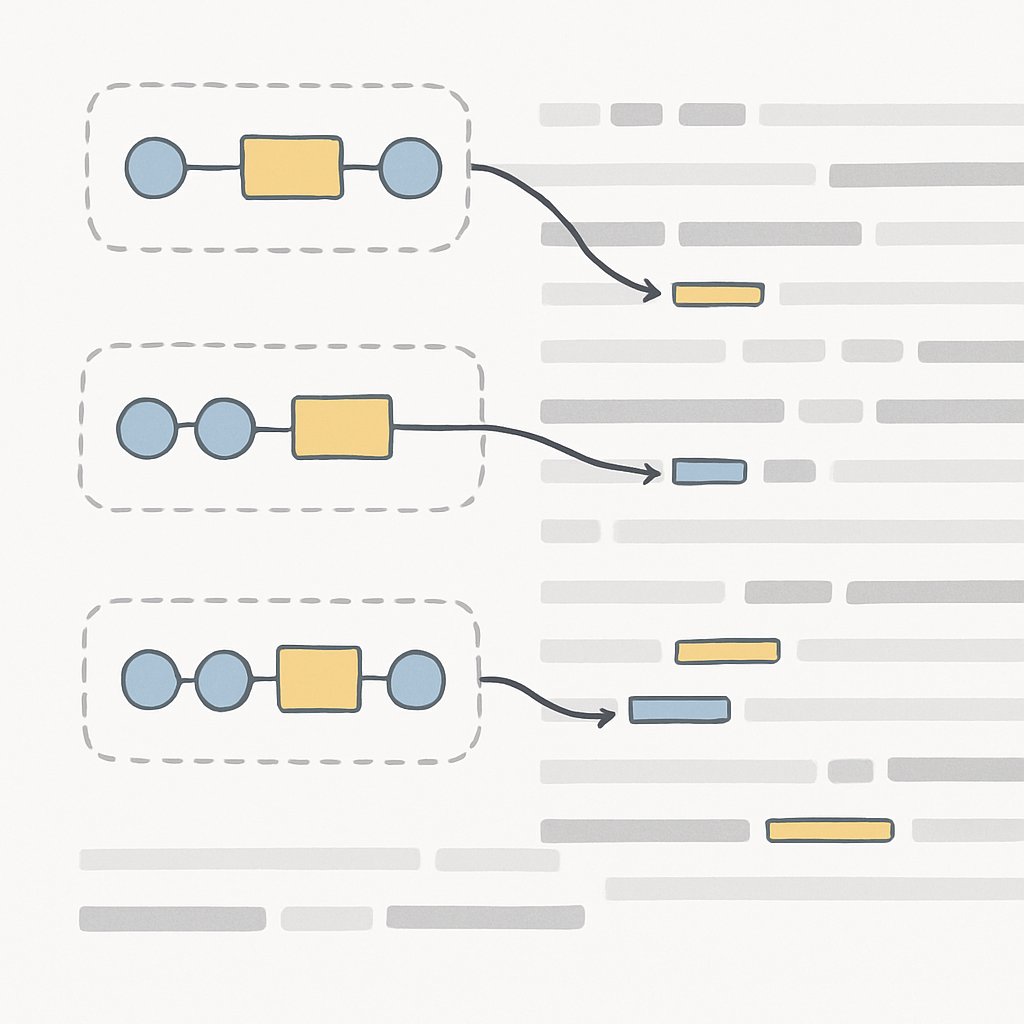
Regex Techniques for Log Parsing and Data Extraction
Learn how to use regex for log parsing and data extraction. Discover patterns, best practices, and pitfalls to improve log analysis and security workflows.
March 13, 2026
9 min read