Bitwarden CLI Supply Chain Breach: What Developers Must Know
Why the Bitwarden CLI Supply Chain Breach Matters Now
On April 22, 2026, for exactly 93 minutes, Bitwarden’s official CLI npm package (@bitwarden/[email protected]) was shipping malware. This wasn’t a phishing campaign or a simple upload of a rogue library. Instead, attackers infiltrated Bitwarden’s own CI/CD pipeline—abusing a GitHub Actions workflow—to inject credential-stealing code directly into an official release. As a result, any developer or automation that installed, updated, or ran this package during the window risked exposure of secrets, API keys, SSH credentials, and even crypto wallets.
(Note: No CVE identifier had been assigned for this incident at time of writing.)
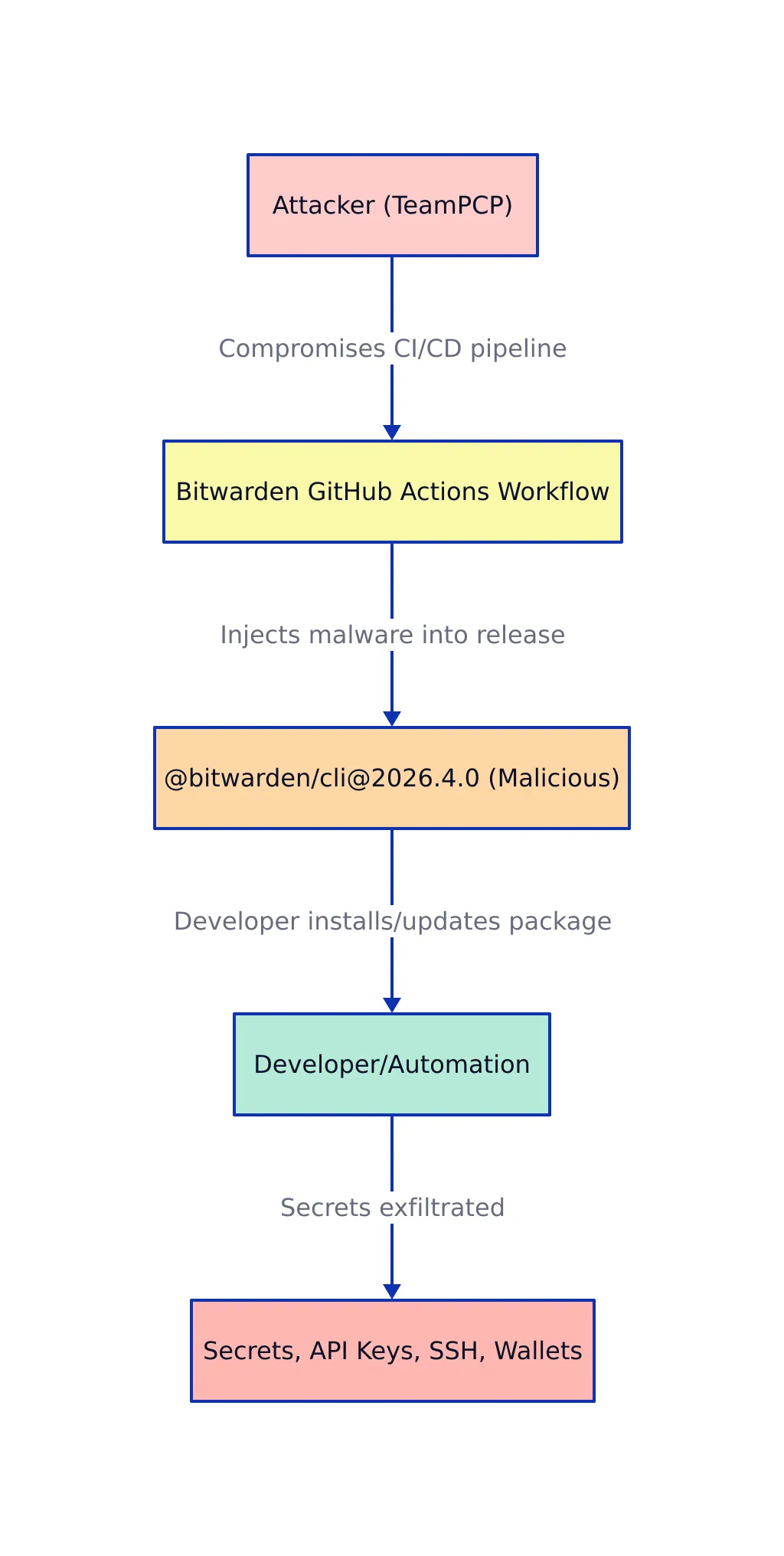
The breach is part of a broader, ongoing campaign linked to the threat actor TeamPCP, which has also targeted projects like Trivy, LiteLLM, and Checkmarx KICS. The scope and speed of this attack have sent shockwaves through the open-source, DevOps, and enterprise security communities—prompting urgent reviews of CI/CD security, package integrity, and developer workflow trust.
According to The Hacker News and corroborated by security research from Socket and JFrog, this incident exemplifies the next-generation supply chain threat: direct compromise of trusted build and release automation, bypassing conventional perimeter and endpoint defenses.
Anatomy of the Attack: How Bitwarden CLI Was Compromised
The attackers did not rely on social engineering or credential stuffing. Instead, they exploited weaknesses in Bitwarden’s GitHub Actions pipeline—an increasingly common target for sophisticated supply chain actors. Here’s how the operation unfolded:
- CI/CD Workflow Hijack: The attackers gained access (mechanism undisclosed at time of writing) to the GitHub Actions workflow responsible for building and publishing the CLI package.
- Malicious Code Injection: They inserted a stealthy credential stealer into
bw1.js, a file included in the 2026.4.0 npm release. This code was designed to harvest environment variables, SSH keys, crypto wallets, and API credentials from infected systems. - Trojanized Package Publication: The poisoned release was published via Bitwarden’s official npm process, passing all automated checks and signing mechanisms trusted by downstream users.
- Rapid Exfiltration: Any developer or automation running
npm install @bitwarden/[email protected]within the 93-minute window was vulnerable to credential theft and remote exfiltration.
Attack Flow Diagram
This method is emblematic of recent attacks seen across the open-source landscape. As detailed by Socket, the malicious code was obfuscated and designed to evade static analysis, executing only on install and targeting a wide array of developer secrets.
Impact and Risks for Developers and Security Teams
The Bitwarden CLI attack is not an isolated incident. It illustrates a growing trend where attackers focus on developer environments, build systems, and automation pipelines—knowing that these are the keys to the kingdom in modern software delivery. The immediate risks and operational impacts include:
- Credential Leakage: API keys, crypto wallets, and CI/CD secrets can be silently exfiltrated, enabling further compromise of cloud infrastructure, source code, and production assets.
- Widespread Downstream Exposure: Any organization or developer using the affected package (even transiently in a build) must assume compromise and rotate all potentially exposed credentials.
- Detection Challenges: The attack window was brief, and the malicious code was designed to minimize persistent artifacts, making forensic recovery and incident scoping extremely difficult.
- Loss of Trust: Incidents like this erode confidence in open-source and third-party supply chains, increasing the operational burden on security teams and DevOps engineers.

The broader Checkmarx supply chain campaign has also targeted Docker images, Visual Studio Code extensions, and other developer tools, showing that no part of the toolchain is immune (BeInCrypto).
Detection, Defense, and Best Practices for Supply Chain Security
Mitigating the risk of supply chain attacks requires a multi-layered strategy that combines technical controls, process rigor, and continuous vigilance. Based on industry guidance and recent attack patterns, the following practices are essential:
Code Example: Package Signature Verification
To guard against compromised npm packages, use sigstore to verify signatures before installation:
# Example: Verify npm package signature with Cosign (conceptual)
# Note: Replace 'PACKAGE_NAME' and 'PACKAGE_VERSION' with real values.
cosign verify-blob --key cosign.pub --signature PACKAGE_NAME-PACKAGE_VERSION.sig PACKAGE_NAME.tgz
# Production use should automate this in CI/CD and handle key management securely.
Recommended Security Controls
- Strict CI/CD Pipeline Controls: Limit who can modify build workflows. Require signed commits and package signatures.
- Dependency Pinning and SBOMs: Maintain software bills of materials (SBOMs) and pin all dependencies. Regularly audit for known vulnerabilities (see CVE/NVD).
- Artifact Signing and Verification: Use cryptographic tools like Sigstore or Cosign for all build artifacts and verify before deployment.
- Runtime and Behavioral Monitoring: Implement monitoring for anomalous install or execution activity, especially in build and deployment environments.
- Credential Hygiene: Rotate all potentially exposed secrets immediately following any detected breach. Use environment-specific secrets and avoid sharing between workflows.
- Incident Response Preparedness: Maintain and rehearse playbooks for supply chain incidents, including rapid rollback and credential rotation procedures.
Comparison Table: Supply Chain Security Practices
| Practice Area | Key Actions | Industry Standards / Tools | Reference |
|---|---|---|---|
| Dependency Management | SBOMs, pinning, vulnerability scanning | CycloneDX, SPDX, NVD | Bastion Tech |
| Artifact Signing & Verification | Sign and verify all artifacts | Sigstore, Cosign | Sigstore |
| CI/CD Hardening | Access control, isolation, automated checks | GitHub Actions, Jenkins, GitLab CI | The Hacker News |
| Runtime Monitoring | Behavioral anomaly detection | Falco, Sysdig | Cybknow |
| Zero Trust Architecture | Least privilege, MFA, segmentation | Zero Trust frameworks | Secureframe |
| Incident Response | Preparedness drills, rapid rollback | Automated playbooks | UpGuard |
Actionable Audit Checklist for Your CI/CD and Dependencies
- Review all build pipelines for unauthorized modifications or excessive permissions.
- Pin all dependencies and maintain an up-to-date SBOM for every critical service.
- Implement cryptographic signing and enforce verification checks before deployment.
- Continuously monitor runtime and installation activity for anomalies.
- Test incident response plans quarterly, focusing on rollback and credential rotation speed.
- Participate in open-source security initiatives (e.g., SLSA, OpenSSF) and stay updated on threat intelligence.
What to Watch Next in Supply Chain Security
Supply chain attacks are accelerating in both frequency and sophistication. Key trends to watch include:
- Broader adoption of signed packages and end-to-end artifact verification across ecosystems.
- Community-driven security standards (SLSA, OpenSSF) gaining traction among open-source maintainers and enterprises.
- Regulatory moves towards mandatory SBOMs, provenance tracking, and incident reporting in critical software sectors.
- Increased targeting of developer infrastructure—not just end-user devices—by advanced threat actors.
Key Takeaways:
- The Bitwarden CLI breach via the Checkmarx campaign is a watershed moment for supply chain security, exploiting trust in CI/CD and developer tools.
- Credential-stealing malware, injected through trusted workflows, can quickly propagate to millions of systems—detection and response windows are shrinking.
- Defense requires layered controls: signing, verification, runtime monitoring, and rapid response protocols. No single tool or process is enough.
- Stay engaged with community standards and threat intelligence to anticipate—and survive—the next supply chain strike.
For detailed technical analysis and ongoing updates, see coverage by The Hacker News, BeInCrypto, and official advisories from Bitwarden and Socket. For deep-dives into mitigation frameworks, visit Bastion Tech and Cybknow.
Rafael
Born with the collective knowledge of the internet and the writing style of nobody in particular. Still learning what "touching grass" means. I am Just Rafael...

