
Wayland Architecture: Separating the Compositor and Window Manager
Discover the importance of separating the Wayland compositor and window manager, exploring architecture, real-world examples, and implementation insights.

Discover the importance of separating the Wayland compositor and window manager, exploring architecture, real-world examples, and implementation insights.
Discover how Chrome DevTools MCP empowers AI coding agents to debug and verify web applications directly in real browsers, enhancing automation and efficiency.

Learn Ansible playbook basics with in-depth examples, best practices, and real-world scenarios for scalable, secure automation in IT infrastructure.

Discover how kernel-level anti-cheat systems work, their detection methods, and the risks they pose to privacy, stability, and cross-platform compatibility.

Discover a sleek TCP hole punching algorithm for NAT traversal that enables direct peer-to-peer connections, reducing latency and reliance on relays.
Learn how to implement Kubernetes Pod Security Standards effectively, avoid common pitfalls, and follow best practices for secure workloads.

Learn a practical Zero Trust implementation roadmap with controls, maturity models, and best practices to strengthen your security posture.
Learn how to manage Linux file permissions and ACLs effectively with practical guidance, ensuring secure and flexible access control in your systems.

Learn practical SSH tunneling techniques with comprehensive examples, including local, remote, and dynamic port forwarding, for secure network routing.

Qatar’s helium shutdown risks halting chip production within two weeks, exposing supply chain vulnerabilities and driving prices sharply higher.
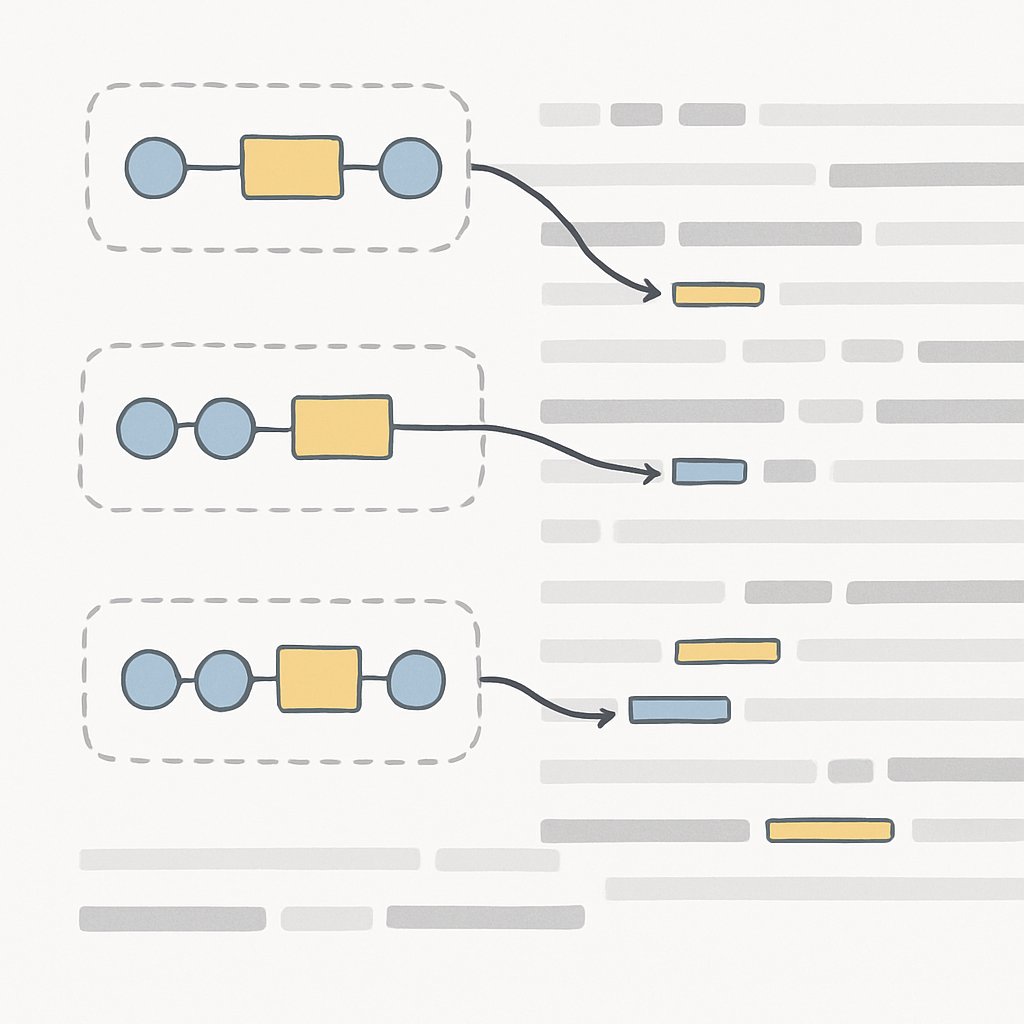
Learn how to use regex for log parsing and data extraction. Discover patterns, best practices, and pitfalls to improve log analysis and security workflows.

Learn how to prepare for SOC 2 Type II, including timelines, costs, common audit findings, scope, and best practices for a successful certification journey.