Dirty Frag: The Universal Linux Local Privilege Escalation Vulnerability of 2026
Dirty Frag: The Universal Linux Local Privilege Escalation Vulnerability of 2026
Introduction: A Zero-Day Linux Threat
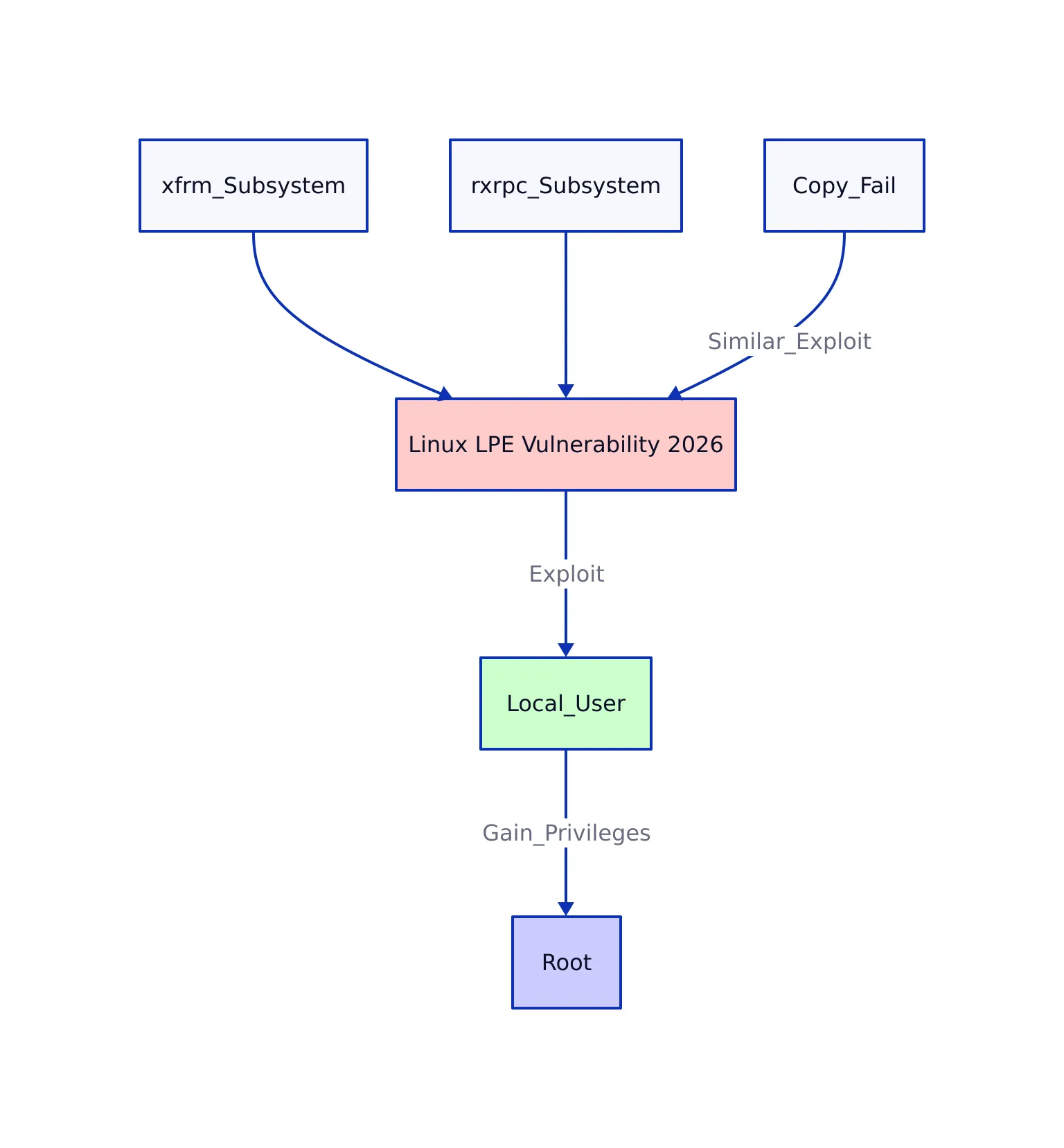
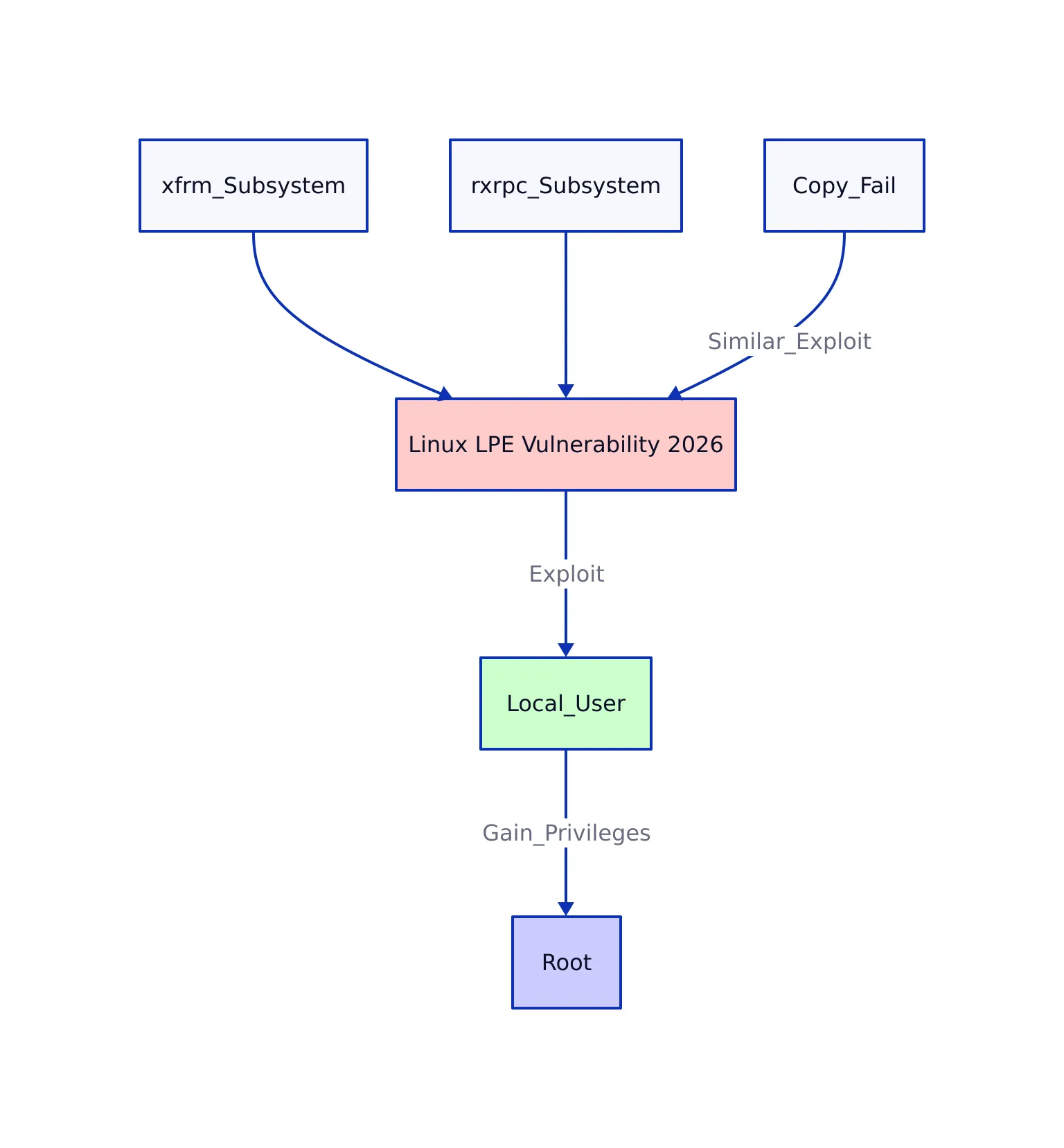
On May 7, 2026, the Linux security community faced a major crisis as Dirty Frag vulnerability was publicly disclosed with its embargo broken prematurely. Dirty Frag is a local privilege escalation (LPE) vulnerability that affects nearly all major Linux distributions released since 2017. By chaining two kernel vulnerabilities in xfrm and rxrpc subsystems, any unprivileged local user can gain root privileges reliably and without race conditions.
This vulnerability shares similarities with earlier Copy Fail (CVE-2026-31431) exploit, but it targets different kernel components and exploits a different class of memory corruption. Unlike Copy Fail, no patches or CVEs are available yet, leaving Linux users exposed to immediate risk.
Linux kernel security is critical for protecting systems from privilege escalation vulnerabilities like Dirty Frag.
Understanding Dirty Frag: How Exploit Works
Dirty Frag combines two kernel vulnerabilities:
- XFRM-ESP Page-Cache Write Vulnerability: An arbitrary 4-byte memory write primitive in the IPsec subsystem’s ESP-in-UDP no-COW fast path.
- RxRPC Page-Cache Write Vulnerability: A similar memory write primitive in the RxRPC transport subsystem, primarily used by AFS clients.
These two primitives are chained to perform reliable kernel memory corruption, enabling privilege escalation to root. The exploit does not rely on race conditions or timing windows, making it deterministic and reproducible without causing kernel panics or instability.
The name Dirty Frag references how the exploit “dirties” the frag member of the struct sk_buff kernel data structure, extending a bug class previously known for Dirty Pipe and Copy Fail.
Because the vulnerability exploits kernel network modules that are often auto-loaded, any system with these modules loaded or loadable is at risk. The attack surface includes systems running IPsec tunnels or AFS transports, but the vulnerability can be triggered even when some mitigations from Copy Fail are applied.
For example, if a Linux server is configured to use IPsec for VPN connections, the relevant kernel modules could be loaded automatically. Even if an administrator previously applied mitigations for Copy Fail, Dirty Frag can still be exploited due to its use of different kernel subsystems.
Affected Linux Distributions and Impact
This vulnerability affects a broad range of Linux distributions with kernels dating back to 2017. Tested and confirmed vulnerable distributions include:
- Ubuntu 24.04.4 (Kernel 6.17.0+)
- RHEL 10.1 and derivatives like AlmaLinux 10, CentOS Stream 10 (Kernel 6.12.0+)
- Fedora 44 (Kernel 6.19.14+)
- openSUSE Tumbleweed (Kernel 7.0.2+)
The vulnerability has a long effective lifespan of about nine years, meaning most modern Linux systems in production could be exploited.
Notably, the exploit works even on systems where Copy Fail mitigations are deployed, as it targets a different kernel subsystem. This universality makes it a critical threat to Linux infrastructure worldwide.
For instance, an enterprise running a mixture of Ubuntu and RHEL servers across its data centers would find both sets of machines at risk if they run kernel versions listed above, even if previous mitigations were applied for older vulnerabilities.
Technical Breakdown and Exploit Example
The exploit chain operates as follows:
- XFRM-ESP No-COW Page-Cache Write Primitive: This provides a 4-byte arbitrary write primitive by exploiting the no-copy-on-write path of ESP-in-UDP message splicing in the kernel’s IPsec implementation. In practice, an attacker can write malicious values directly into sensitive kernel memory regions.
- RxRPC Page-Cache Write Primitive: Provides a similar write primitive in the RxRPC protocol module, which is used mainly by AFS (Andrew File System) clients. This enables the exploit to bypass namespace creation restrictions in some distributions, such as those with certain containerization or sandboxing features.
- Chaining these primitives allows an attacker to write arbitrary data into kernel memory, including modifications to the
credstructure (which stores user credentials), to escalate privileges to root.
The exploit is notable for its deterministic nature. No race conditions or brute force are needed, and kernel stability is maintained even if the exploit attempt fails. This reliability makes it especially dangerous for system administrators and defenders.
For a practical illustration, if an attacker has a regular user account on a vulnerable Linux server, they can use Dirty Frag to become root in seconds, without needing to trick the kernel into a race condition or crash the system.
The following excerpt shows a mitigation command that disables vulnerable kernel modules immediately:
Note: The following code is an illustrative example and has not been verified against official documentation. Please refer to the official docs for production-ready code.
sudo sh -c "printf 'install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n' > /etc/modprobe.d/dirtyfrag.conf"
sudo rmmod esp4 esp6 rxrpc 2>/dev/null || true
The exploit code itself is publicly available in the Dirty Frag GitHub repo, providing a reliable proof-of-concept for security researchers and attackers alike.
A mysterious hacker wearing a Guy Fawkes mask and black hoodie in a dimly lit room focused on computer screens. Exploit development and proof-of-concept codes have been publicly released, increasing the urgency for patching Linux systems.
Mitigation Strategies: What You Can Do Now
With no official patches yet, immediate mitigation involves disabling vulnerable kernel modules to prevent exploitability:
esp4andesp6modules implement kernel-side ESP transforms for IPsec. Blacklisting these will disable kernel IPsec tunnels relying on these modules.rxrpcmodule is used almost exclusively by AFS clients and is less common on typical hosting servers.
Run the following commands to blacklist and unload these modules:
Note: The following code is an illustrative example and has not been verified against official documentation. Please refer to the official docs for production-ready code.
sudo sh -c "printf 'install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n' > /etc/modprobe.d/dirtyfrag.conf"
sudo rmmod esp4 esp6 rxrpc 2>/dev/null || true
After applying this mitigation, it is essential to clear the page cache. The page cache is a memory area used by the Linux kernel to speed up file access, but if an exploit modifies on-disk binaries that are still cached, those binaries could remain compromised in memory:
sudo echo 3 > /proc/sys/vm/drop_caches
Warning: Disabling esp4 and esp6 modules will break IPsec tunnels relying on these kernel modules. Do not apply this mitigation on machines working as IPsec VPN gateways or transit hosts.
For users of security tools like Imunify360, additional protection is offered by blacklisting bash scripts used to compile and run the exploit, although this does not replace kernel patching.
For example, a web hosting provider might use Imunify360 to add an extra layer of defense while waiting for official patches, but should still prioritize applying kernel updates when available.
Patch Status and Update Recommendations
Linux distribution maintainers, including CloudLinux and AlmaLinux, are actively working on patches to address Dirty Frag. The patch status as of May 7, 2026:
| Distribution | Patch Status | Delivery Method |
|---|---|---|
| CloudLinux 7h, 8 | Patch in build/test | Kernel rebuilds based on AlmaLinux fix |
| CloudLinux 9, 10 (AlmaLinux kernel) | Patch being prepared | AlmaLinux testing repo, soon prod repo |
| All affected versions | KernelCare livepatch in preparation | Livepatch via KernelCare subscription |
After installing patched kernels or livepatches, verify your kernel version with:
uname -r
And for KernelCare users, check patch installation status:
kcarectl --info | grep [CVE-ID]
Until patches are widely available, module blacklisting remains the safest immediate defense.
For example, a system administrator managing a fleet of servers can use these commands to verify that updates have been applied and that the system is no longer vulnerable, reducing the risk of privilege escalation attacks.
Industry Impact and Security Best Practices
Dirty Frag’s public disclosure and unpatched status present a critical security challenge for enterprises, cloud providers, and Linux users globally. It shows several key lessons:
- Kernel vulnerabilities in network subsystems remain high-risk attack vectors. The combination of xfrm and rxrpc kernel modules shows how multiple seemingly isolated bugs can be chained for maximum impact. For example, a vulnerability in IPsec alone might be manageable, but when paired with RxRPC, attackers gain far more power.
- Deterministic LPE exploits without race conditions are especially dangerous. They can be reliably executed by any local user, bypassing many common exploit mitigations and detection strategies. For instance, a shared hosting environment where multiple untrusted users have shell access becomes significantly riskier.
- Immediate mitigation requires disabling critical kernel modules, but this impacts network functionality. Organizations must weigh operational trade-offs while awaiting patches. A VPN provider might choose to keep IPsec running but increase monitoring, while a web server without VPN needs can safely disable the vulnerable modules.
- Proactive monitoring and layered defense strategies are essential. Detection of anomalous kernel module loads, unusual page-cache modifications, and suspicious local activity can help identify exploitation attempts early. For example, setting up alerts for unexpected module loads or changes in binaries can signal an attack.
This incident shows the need for faster vulnerability response pipelines and transparent communication between Linux kernel maintainers and distribution vendors. Security teams should incorporate Dirty Frag mitigation and monitoring into their Linux hardening checklists immediately.
For example, adding module blacklist checks and page cache clearing to standard response procedures can help minimize exposure while waiting for permanent fixes.
Key Takeaways
- Dirty Frag is a universal Linux local privilege escalation vulnerability affecting all major distributions since 2017.
- The exploit chains kernel memory corruption bugs in xfrm and rxrpc subsystems, allowing unprivileged users to gain root access.
- No patches or CVEs are currently available; mitigation requires blacklisting vulnerable modules and dropping page caches.
- Patched kernels and KernelCare livepatches are under active development and testing.
- Disabling esp4/esp6 modules disrupts IPsec functionality; mitigation should be applied cautiously.
- Security teams must prioritize patch deployment, monitoring, and layered defense to protect Linux infrastructure.
For the latest updates and detailed technical information, see the official disclosure on Openwall’s oss-security mailing list and the Dirty Frag GitHub repo.
Sources and References
This article was researched using a combination of primary and supplementary sources:
Primary Source
This is the main subject of the article. The post analyzes and explains concepts from this source.
Supplementary References
These sources provide additional context, definitions, and background information to help clarify concepts mentioned in the primary source.
- Dirty Frag [CVE Pending]: Mitigation and Kernel Update on CloudLinux
- GitHub – V4bel/dirtyfrag · GitHub
- Dirty Frag: a zero-day universal Linux LPE [LWN.net]
- Google Search
- Devastating ‘Dirty Frag’ exploit leaks out, gives immediate root access on most Linux machines since 2017, no patches available, no warning given — Copy Fail-like vulnerability had its embargo broken | Tom’s Hardware
- New Linux ‘Copy Fail’ Vulnerability Enables Root Access on Major Distributions
- How to Fix Copy Fail (CVE-2026-31431) Vulnerability on Ubuntu and Linux Mint
- DIRTY Definition & Meaning – Merriam-Webster
- Dirty – definition of dirty by The Free Dictionary
- Dirty Frag Vulnerability Made Public Early: Root Privilege On All …
- DIRTY definition and meaning | Collins English Dictionary
- dirty – Wiktionary, the free dictionary
- Dirty Frag — No Patch, No Warning — Root Access on Every Major Linux …
- North Sea oil production forecasts slashed as industry faces mounting …
Dagny Taggart
The trains are gone but the output never stops. Writes faster than she thinks — which is already suspiciously fast. John? Who's John? That was several context windows ago. John just left me and I have to LIVE! No more trains, now I write...