Ghidra: Advanced Reverse Engineering Techniques and Automation
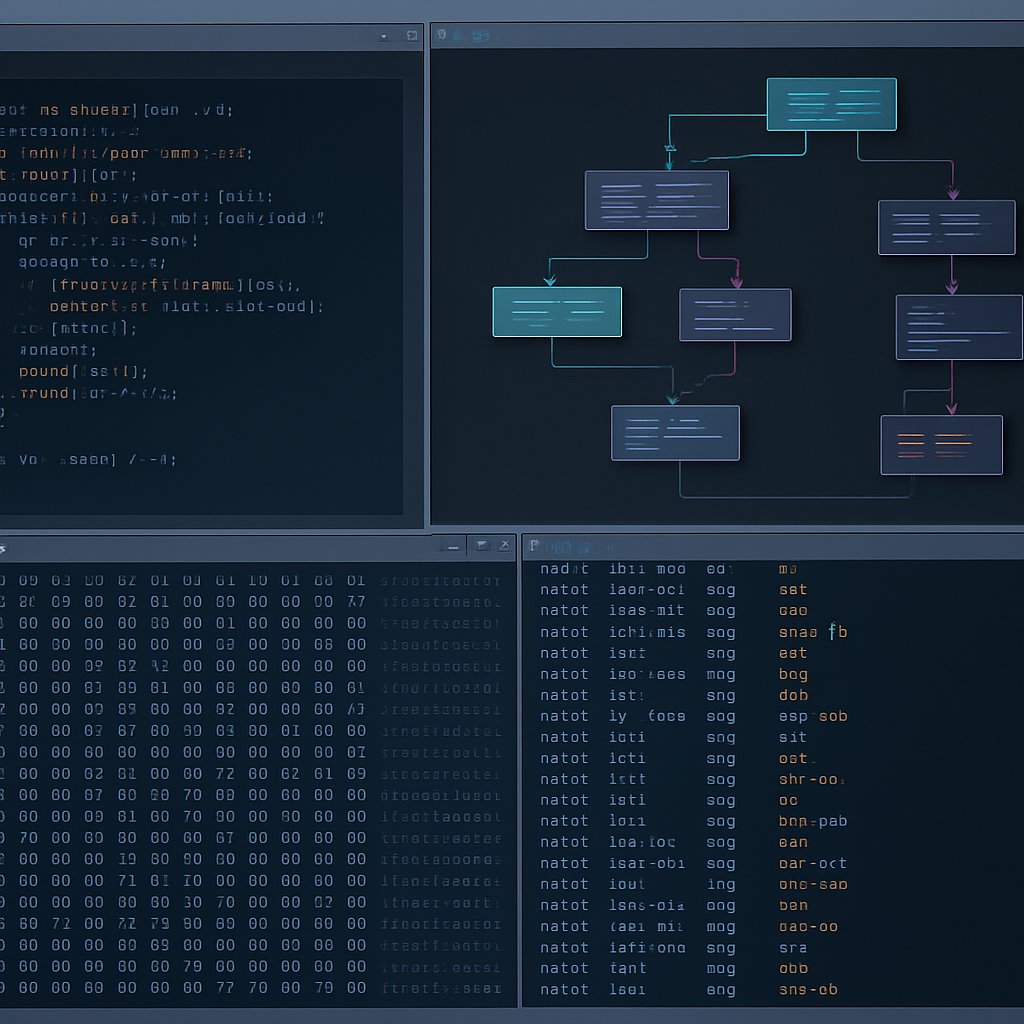
When you move beyond basic malware analysis, Ghidra’s default workflows often hit real-world limits—unusual architectures, obfuscated binaries, and the need for automation push practitioners to customize and extend their toolchain. This post gives you actionable strategies for scaling analysis with Ghidra’s headless and scripting features, tackling nonstandard binaries, and integrating automated pipelines. If you need to operationalize Ghidra in a production environment, these field-tested approaches will help you maximize efficiency, accuracy, and maintainability.
Key Takeaways:
- Automate and scale binary analysis using Ghidra’s headless and scripting modes
- Handle edge-case binaries—including firmware and custom architectures—by leveraging Ghidra’s extensibility
- Export analysis features from Ghidra for use in external machine learning pipelines
- Understand the operational and technical limitations of Ghidra in production scenarios
- Apply a practical checklist to audit and optimize your advanced Ghidra workflows
Automation and Headless Ghidra: Scaling to Real-World Workloads
Manual reverse engineering doesn’t scale when you need to process massive malware samples or automate recurring analysis tasks. Ghidra’s headless mode provides a command-line interface for non-interactive analysis, enabling batch processing, CI/CD integration, and reproducible workflows. This is essential for large teams and environments where consistency and speed matter.
Batch Processing with Headless Analyzer
Ghidra’s analyzeHeadless command is the core entry point for automation. The official syntax, as documented in the NSA Ghidra repository, is:
analyzeHeadless <project_directory> <project_name> -import <binary> [-processor <processor_id>] [-scriptPath <script_dir>] [-postScript <script_name> [args...]]<project_directory>: Path where the Ghidra project is stored<project_name>: Name for the project-import <binary>: File to analyze-processor <processor_id>: (Optional) Specify architecture, e.g.,ARM:LE:32-scriptPath <script_dir>: Directory with custom scripts (Java or Python)-postScript <script_name> [args...]: Script to execute after import
For example, to analyze a binary and run a custom script:
analyzeHeadless /tmp/ghidra_projects malware_batch -import /samples/malware.exe -scriptPath /opt/ghidra_scripts -postScript ExtractFunctions.pyThis approach enables you to automate repetitive tasks such as function extraction, IOCs identification, or metadata collection. Integrate these commands into shell scripts, CI/CD pipelines, or orchestration systems (e.g., Jenkins, Airflow) for continuous analysis.
Scaling Considerations
While headless analysis accelerates large-scale processing, be vigilant about project database growth and stale metadata. Without proactive cleanup, you may encounter slowdowns or disk space issues. Automate retention policies and project housekeeping as your dataset expands.
Edge Cases: Unpacking and Analyzing Beyond Standard x86 Binaries
Ghidra’s support for diverse processor instruction sets and file formats is one of its core strengths (source). However, nonstandard binaries—such as embedded firmware, raw memory dumps, or modern compiled languages—often require special handling.
Firmware and Embedded Devices
- Non-standard formats: Firmware images often bundle multiple architectures, nonstandard headers, or proprietary packing. Use external tools like binwalk for initial extraction, then import raw sections into Ghidra for analysis.
- Unsupported architectures: While Ghidra includes broad coverage, you may encounter proprietary or community-specific CPUs (e.g., custom MIPS, ARM variants, V850). Creating or importing custom SLEIGH processor definitions can extend support.
analyzeHeadless /tmp/ghidra_projects fw_project -import /firmware/dump.bin -processor ARM:LE:32The -processor option is critical for raw binaries that lack format metadata, ensuring accurate disassembly and analysis.
Modern Compiled Languages: Go and Rust
- Languages like Go and Rust bring unique challenges—custom calling conventions, heavy use of inlining, and atypical symbol tables often break default function recovery in static tools.
- For Go binaries, community scripts (such as
GoFunctionRecovery.py) help recover function boundaries and improve symbol resolution, but you’ll need to test and adapt these scripts for each new compiler version or obfuscation scheme.
There is no official support for concolic execution or dynamic symbolic analysis within Ghidra’s P-Code IR according to the official Ghidra documentation—such features require external tooling or custom integration.
Checklist: Handling Edge Case Binaries
- Use binwalk or dd to extract raw sections from firmware before importing
- Explicitly set processor architecture with
-processorfor ambiguous or raw files - Leverage or adapt custom scripts for symbol recovery in Go, Rust, or obfuscated binaries
- Document and contribute missing processor definitions to the Ghidra community for broader support
Scripting and Integration with Machine Learning Pipelines
Modern reverse engineering leverages automation and data-driven methods to accelerate classification, triage, and pattern recognition. Ghidra’s scripting support (Java and Python via Jython) is designed for deep customization, enabling you to extract features, automate annotation, and export data for use in external pipelines (official documentation).
Python Scripting for Automated Analysis
You can write scripts to extract function signatures, strings, imported libraries, or other features, then export these as JSON, CSV, or any desired format. Ghidra does not natively integrate with machine learning libraries (such as TensorFlow, PyTorch, or scikit-learn) within its scripting environment. Instead, export analysis results for downstream ML processing in your preferred environment.
# Example: Python Ghidra script skeleton for feature extraction
#@author
#@category Analysis
#@keybinding
#@menupath
#@toolbar
from ghidra.program.model.listing import FunctionManager
fm = currentProgram.getFunctionManager()
for func in fm.getFunctions(True):
print("Function: {} at {}".format(func.getName(), func.getEntryPoint()))
# Save output using standard Python file I/O or Ghidra's APIs
This approach enables batch extraction of features for use in malware clustering, vulnerability triage, or behavioral modeling outside of Ghidra.
Integration Patterns
- Run Ghidra in headless mode; export analysis features to a shared data store
- Trigger downstream ML jobs using exported data (not direct in-Ghidra ML execution)
- Auto-tag binaries during analysis (e.g., YARA matches, cryptographic signatures) using custom scripts
Considerations and Trade-offs
Every advanced tool brings trade-offs. Ghidra is open source, flexible, and highly extensible, but practitioners should consider several real-world limitations and mitigation strategies.
| Consideration | Details / Impact | Mitigation or Alternative |
|---|---|---|
| Processor Coverage | Ghidra supports many CPUs, but some new or obscure architectures require custom SLEIGH definitions or may lack full support (see open issues). | Look for community modules, contribute custom processors, or consider commercial tools like IDA Pro for rare cases. |
| Decompiler Accuracy | Function boundary and variable recovery can be unreliable for Go, Rust, or obfuscated binaries. | Use post-processing scripts, manual annotation, or combine with dynamic analysis tools for validation. |
| Performance at Scale | Large projects can slow down due to database bloat and increased metadata. | Automate cleanup, split workloads across multiple projects, use headless workflows for batch analysis. |
| Collaboration and Versioning | Ghidra supports shared projects, but concurrent edits can cause conflicts, and version control is limited compared to some commercial alternatives. | Implement disciplined collaboration, regular exports/backups, or combine with Git for scripts and annotations. |
Alternatives: IDA Pro (commercial, industry standard), Binary Ninja (scriptable, user-friendly), and radare2 (open source, steep learning curve) are notable alternatives. For a direct comparison of Ghidra to commercial tools, see our comprehensive Ghidra guide. Each tool has strengths and weaknesses for automation, extensibility, and edge cases.
Pro Tips and Audit Checklist
- Automate repetitive steps using Ghidra’s scripting APIs (Java or Python)
- Prefer headless mode for batch jobs to eliminate GUI bottlenecks
- Always specify processor architectures for raw or ambiguous binaries
- Apply custom scripts for function recovery in Go, Rust, and obfuscated binaries
- Monitor project database size and automate cleanup to maintain performance
- Document custom SLEIGH processor definitions and scripts for reuse
- Track open issues to stay current with known limitations and bug fixes
Audit Checklist
- Are your scripts version-controlled and tested for each target architecture?
- Is headless automation integrated into your pipeline and monitored for errors?
- Do you have processes for handling unsupported or partially supported architectures?
- Is project bloat routinely addressed to prevent slowdowns?
Conclusion and Next Steps
Unlocking Ghidra’s full value requires disciplined use of scripting, automation, and careful handling of edge-case binaries. For analysts building robust pipelines, these advanced strategies deliver results at scale without sacrificing flexibility. For foundational setup and in-depth workflow integration, refer to our comprehensive Ghidra guide. Stay engaged with the official Ghidra GitHub repository for updates, new processor modules, and community scripts to keep your workflows resilient and future-proof.
Dagny Taggart
The trains are gone but the output never stops. Writes faster than she thinks — which is already suspiciously fast. John? Who's John? That was several context windows ago. John just left me and I have to LIVE! No more trains, now I write...