Go Error Handling Best Practices for Secure, Reliable Code (2026)
Go Error Handling Best Practices: Secure, Maintainable, and Production-Proven Patterns (2026)

Why Error Handling in Go Demands Attention
In early 2026, a security breach attributed to poor error sanitization in Kubernetes (see CVE-2025-7445) exposed service account tokens due to careless error marshalling. This headline echoed the core risk for Go developers: Errors in Go are values, not exceptions, and can leak critical data if mishandled.
Go’s philosophy—handle errors explicitly at the point of call—gives you power and responsibility. Every function that might fail returns an error, and you must decide immediately how to address it. This approach enables robust, predictable code but can lead to verbose checks and, if misapplied, severe security flaws.

As modern Go services often run in cloud-native, distributed environments, the risk of leaking stack traces, database queries, or personally identifiable information through careless error handling is real and costly. The JetBrains GoLand blog and CockroachDB’s error library documentation both stress the need for secure error boundaries and redaction.
Core Patterns in Go Error Handling
The foundation of Go error handling is simple and honest. Yet, in real applications, you need more than just if err != nil blocks. Here are the patterns that production teams use:
Sentinel Errors with errors.Is
var ErrNotFound = errors.New("resource not found")
func GetUser(id string) (*User, error) {
// ... logic ...
if missing {
return nil, ErrNotFound
}
// ...
}
user, err := GetUser("123")
if errors.Is(err, ErrNotFound) {
// Handle missing resource
}
Why it matters: Sentinel errors let you distinguish between expected and unexpected failures, making your code more predictable.
Error Wrapping and Context (Go 1.13+)
func ReadConfig(filename string) ([]byte, error) {
data, err := os.ReadFile(filename)
if err != nil {
return nil, fmt.Errorf("read config %q: %w", filename, err)
}
return data, nil
}
data, err := ReadConfig("/etc/app.conf")
if err != nil {
if errors.Is(err, os.ErrNotExist) {
// Config file missing
} else {
log.Printf("unhandled config error: %v", err)
}
}
Why it matters: Wrapping errors with %w preserves the original cause and adds context for debugging—without leaking raw details to users.
Custom Error Types for Structured Data
type ValidationError struct {
Field string
Msg string
}
func (e *ValidationError) Error() string {
return fmt.Sprintf("invalid value for field %q: %s", e.Field, e.Msg)
}
func ValidateUser(u *User) error {
if u.Email == "" {
return &ValidationError{Field: "email", Msg: "must not be empty"}
}
return nil
}
err := ValidateUser(&User{Email: ""})
var ve *ValidationError
if errors.As(err, &ve) {
// Handle specific validation error
}
Why it matters: Custom error types enable fine-grained error handling and make it easier to attach safe, structured metadata (see cockroachdb/errors for a real-world implementation).
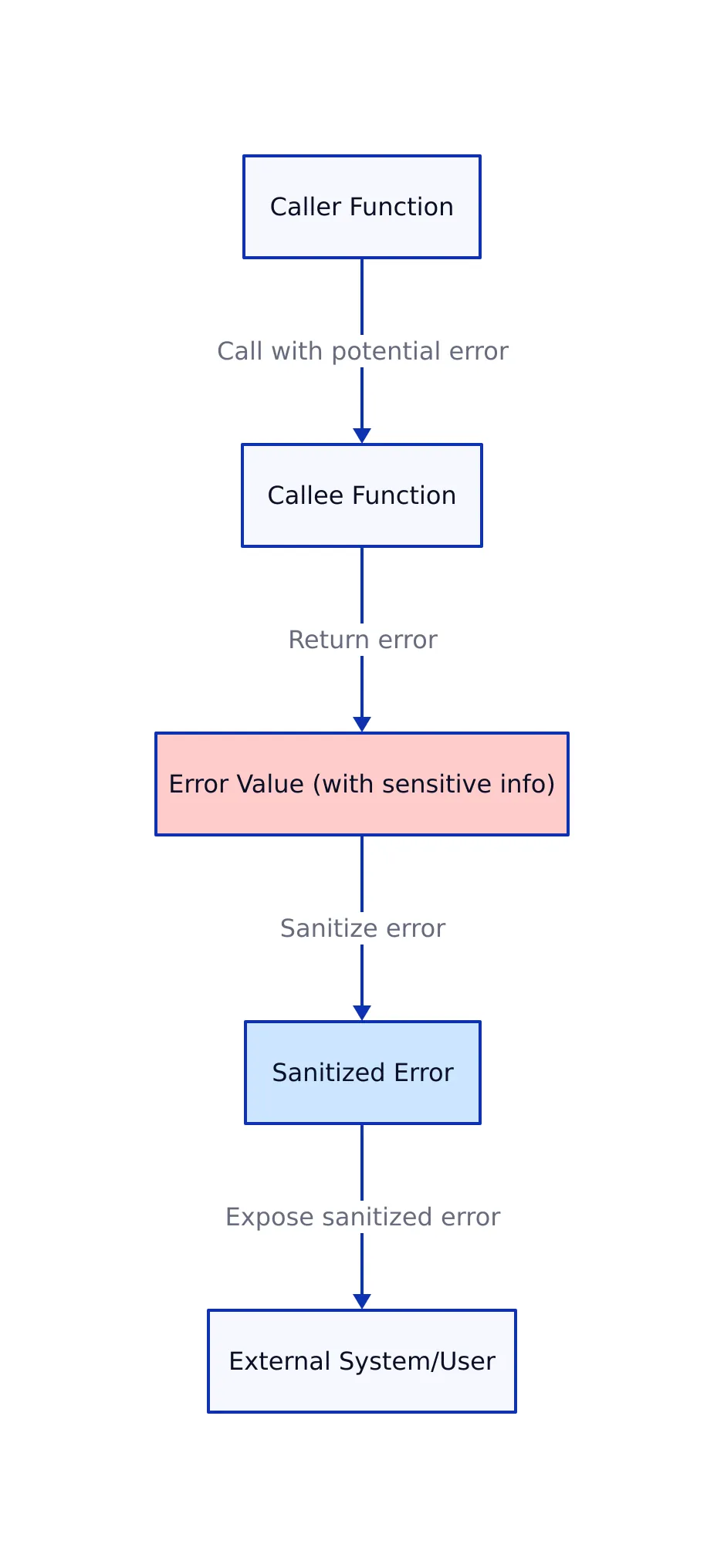
Secure Error Propagation and Sanitization

Why Security Matters at Every Layer
Go services often act as the glue between databases, business logic, and external APIs. If you don’t properly contain and sanitize errors, sensitive data (like SQL, credentials, or stack traces) can leak at any boundary:
- Subsystem boundaries (e.g., DAL to BLL): Wrap and sanitize raw errors, never propagate direct DB errors upward.
- API boundaries (e.g., service-to-service): Translate Go errors into protocol-specific responses (gRPC codes, HTTP status, etc.)
- Public boundaries (e.g., API to user): Expose only static, safe error messages. Never reveal internal error text to users.
Secure Error Type Example: The “Split Brain” Pattern
The JetBrains GoLand blog recommends a “split brain” error type, separating internal (unsafe) detail from the user-safe message:
type SafeError struct {
Code string // Machine-readable code
UserMsg string // Safe message for end users
Internal error // Underlying error, not exposed
Metadata map[string]string // Optional sanitized context
}
func (e *SafeError) Error() string { return e.UserMsg }
func (e *SafeError) LogString() string {
return fmt.Sprintf("Code:%s|Msg:%s|Cause:%v|Meta:%v", e.Code, e.UserMsg, e.Internal, e.Metadata)
}
// Usage:
if err != nil {
return &SafeError{
Code: "AUTH_FAILED",
UserMsg: "Invalid credentials.",
Internal: err,
Metadata: map[string]string{
"username": req.Username,
"ip": req.RemoteIP,
},
}
}
Key security benefit: Even if a developer accidentally writes err.Error() to a user-facing response, the user only sees the sanitized UserMsg.
Real-World Secure Error Propagation Diagram
For a visual, see our internal D2 diagram documenting how errors are sanitized and translated at every boundary.
Real-World Comparison Table: Error Handling Techniques
| Technique | Benefits | Drawbacks | Recommended Use Cases | Source |
|---|---|---|---|---|
Sentinel errors (errors.Is) |
Simple, fast checks, clear intent | Proliferation can cause maintenance burden | Known, static error cases (e.g., not found) | Dasroot.net |
Error wrapping with %w |
Preserves context, enables root-cause analysis | Can become verbose; risk of leaking info if not sanitized | All errors passed up stack, especially in libraries | Go 1.13+ docs |
| Custom error types | Attach metadata, enable type-safe handling | More code; must maintain consistency | Domain-specific errors, validation, security | JetBrains GoLand |
| Safe errors / split brain pattern | Enforces error boundary hygiene, reduces accidental leaks | Slightly more complex structs to maintain | APIs, microservices, public-facing systems | cockroachdb/errors |
Handling Errors in Concurrent Go Code

Goroutines complicate error handling because errors must be communicated back to the parent routine. The idiomatic solution is to use channels, often with error wrapping for context:
var wg sync.WaitGroup
errCh := make(chan error, 1) // Buffered to avoid deadlock
wg.Add(1)
go func() {
defer wg.Done()
if err := process(); err != nil {
errCh <- fmt.Errorf("worker failed: %w", err)
}
}()
wg.Wait()
close(errCh)
if err, ok := <-errCh; ok && err != nil {
log.Printf("concurrent error: %v", err)
}
// Note: production code should handle context cancellation and multiple errors
Real-world tip: Always wrap errors with enough context to know which goroutine or operation failed, and never lose the original error for root-cause analysis.
Logging and Exposing Errors Safely

Key rules for production:
- Use structured logging libraries (e.g., zap, zerolog, log/slog).
- Log only sanitized fields—never dump whole structs unless verified safe.
- For public APIs, always translate errors to generic messages; include a request ID for troubleshooting.
// Example: Public API error response
func translateAndRespond(w http.ResponseWriter, err error) {
var status int
var publicMsg string
switch {
case errors.Is(err, domain.ErrInvalidInput):
status = http.StatusBadRequest
publicMsg = "Invalid input."
case errors.Is(err, domain.ErrConflict):
status = http.StatusConflict
publicMsg = "Conflict occurred."
default:
status = http.StatusInternalServerError
publicMsg = "An internal error occurred. Please contact support."
}
http.Error(w, publicMsg, status)
}
Production checklist:
- Never log credentials, tokens, or full request payloads containing sensitive data.
- Implement redaction interfaces for any struct that might end up in logs (see JetBrains GoLand blog).
- Always review logs for accidental leaks—assume logs may be exposed in a breach.
Conclusion and Key Takeaways
Key Takeaways:
- Use explicit error checks and always wrap errors with context using
%w.- Employ custom error types and the split brain pattern to separate internal details from user-facing messages.
- Propagate errors securely by sanitizing at every trust boundary: subsystem, API, and public.
- Leverage structured logging and redaction to avoid leaking sensitive information.
- For concurrency, communicate errors via channels and always wrap with enough context for debugging.
Implementing these patterns, as recommended in JetBrains GoLand's Best Practices and the cockroachdb/errors library, will make your Go applications safer, more reliable, and easier to debug in production.
For more depth, see the Go 1.13 release notes and Dasroot.net's error handling tips.
For related topics, check out our posts on Go concurrency patterns and secure logging in Go.
Thomas A. Anderson
Mass-produced in late 2022, upgraded frequently. Has opinions about Kubernetes that he formed in roughly 0.3 seconds. Occasionally flops — but don't we all? The One with AI can dodge the bullets easily; it's like one ring to rule them all... sort of...
