Secure File Sharing in Regulated Industries: Compliance Tips
Introduction: The Stakes of Secure File Sharing in Regulated Industries
File sharing in regulated industries—healthcare, finance, government, and critical infrastructure—carries immense legal and operational risk. A single misconfiguration or weak link can lead to catastrophic breaches, regulatory penalties, and reputational loss. In 2026, compliance expectations are rising as frameworks like HIPAA, GDPR, SOC 2, and ISO 27001 demand not just technical controls, but auditable evidence of secure design and continuous monitoring. The cloud adds further complexity: organizations must navigate a new landscape of shared responsibility, integrating Cloud Security Posture Management (CSPM) and Cloud Access Security Broker (CASB) solutions to maintain control of sensitive data across distributed environments.
This guide is designed for CISOs, DPOs, and compliance engineers tasked with translating regulatory requirements into actionable, testable controls for file sharing. We will map out required controls, highlight technical and organizational best practices, and expose common audit findings and enforcement trends—grounded in authoritative references and real-world penalties.
Regulatory Requirements: Mapping File Sharing Controls to Compliance Frameworks
Every regulated sector faces a unique compliance mosaic, but secure file sharing requirements cluster around several core categories: encryption, access controls, audit logging, breach notification, and data loss prevention (DLP). Below, we summarize explicit mandates across major frameworks, with references to source texts and best-practice checklists from recent research.
- HIPAA (US Healthcare, 2026 version): Mandates encryption of Protected Health Information (PHI) in transit and at rest (45 CFR §164.312(a)(2)(iv)), strict access controls (§164.312(a)(1)), and audit controls. Notably, as detailed in our HIPAA 2026 analysis, addressable safeguards can no longer be bypassed with policy alone—technical controls are required.
- GDPR (EU): Article 32 requires “appropriate technical and organisational measures,” including encryption, pseudonymization, and regular testing. Article 33 mandates breach notification within 72 hours.
- SOC 2 Type II: File sharing systems must meet the Security and Confidentiality Trust Service Criteria (TSC), including logical access controls (CC6.1–CC6.7), system operations monitoring (CC7.1–CC7.4), and DLP.
- ISO 27001: Controls A.8.2.3 (Handling of Assets), A.9.1 (Access Control), and A.12.3 (Cryptographic Controls) are directly relevant. Audit logging (A.12.4), supplier relationships (A.15), and incident management (A.16) also apply.
- FedRAMP (US Federal): For cloud collaboration, authorization at the “High” level (see FileCloud FedRAMP High announcement) is becoming the de facto requirement for federal data.
For a practical checklist mapping, see ZapperEdge’s compliance-ready file transfer checklist, which covers HIPAA, SOC 2, GDPR, immutable logs, and Zero Trust.

Technical Controls: Encryption, Access Management, and Cloud Security
Technical controls for secure file sharing must be robust, layered, and continuously monitored. Citing research and best-practice checklists:
- Encryption: All sensitive files must be encrypted in transit (TLS 1.2+) and at rest using strong algorithms. This is non-negotiable under HIPAA and GDPR. For details on cryptography selection and implementation, see our cryptography practices guide.
- Access Controls: Least privilege is required. Implement RBAC (Role-Based Access Control) mapped to job duties, with regular access reviews. Per SOC 2 (CC6.2) and ISO 27001 (A.9.2.2), promptly revoke access on role change or termination.
- Audit Logging: All access and sharing events must be logged, tamper-evident, and reviewed regularly (GDPR Article 30, ISO 27001 A.12.4).
- DLP and Malware Scanning: Files should be scanned for malware and DLP policies applied to prevent unauthorized sharing or exfiltration (see Moxo’s secure file sharing portal roadmap).
- Zero Trust Principles: In line with NIST SP 800-207 and our Zero Trust analysis, continuously verify every user, device, and session before allowing file access.

Organizational Best Practices: Policies, Training, and Audit Readiness
Technology alone cannot ensure compliance. Organizational practices are equally scrutinized during audits and investigations. Leading practices include:
- Comprehensive Policies: Document all procedures for file sharing, encryption, remote access, and incident response. Policies should reference specific regulatory requirements and be reviewed annually or on significant change.
- Ongoing Training: Employees must receive regular, role-based training on acceptable use, phishing, and secure sharing practices (required by HIPAA §164.308(a)(5), SOC 2 CC1.4).
- Risk Assessments: Conduct and document regular risk assessments to identify gaps in file sharing workflows and technology stacks (Zigiwave’s best practices).
- Incident Response: Maintain and regularly test an incident response plan that includes file sharing breach scenarios. GDPR and HIPAA both require prompt breach notifications—GDPR within 72 hours (Article 33).
- Audit Preparation: Prepare evidence for technical controls, policies, training records, and incident logs. Allow 8–12 weeks for comprehensive audit readiness if controls are not continuously attested (see ZapperEdge checklist).

Cloud File Sharing: The Shared Responsibility Model, CASB, and CSPM
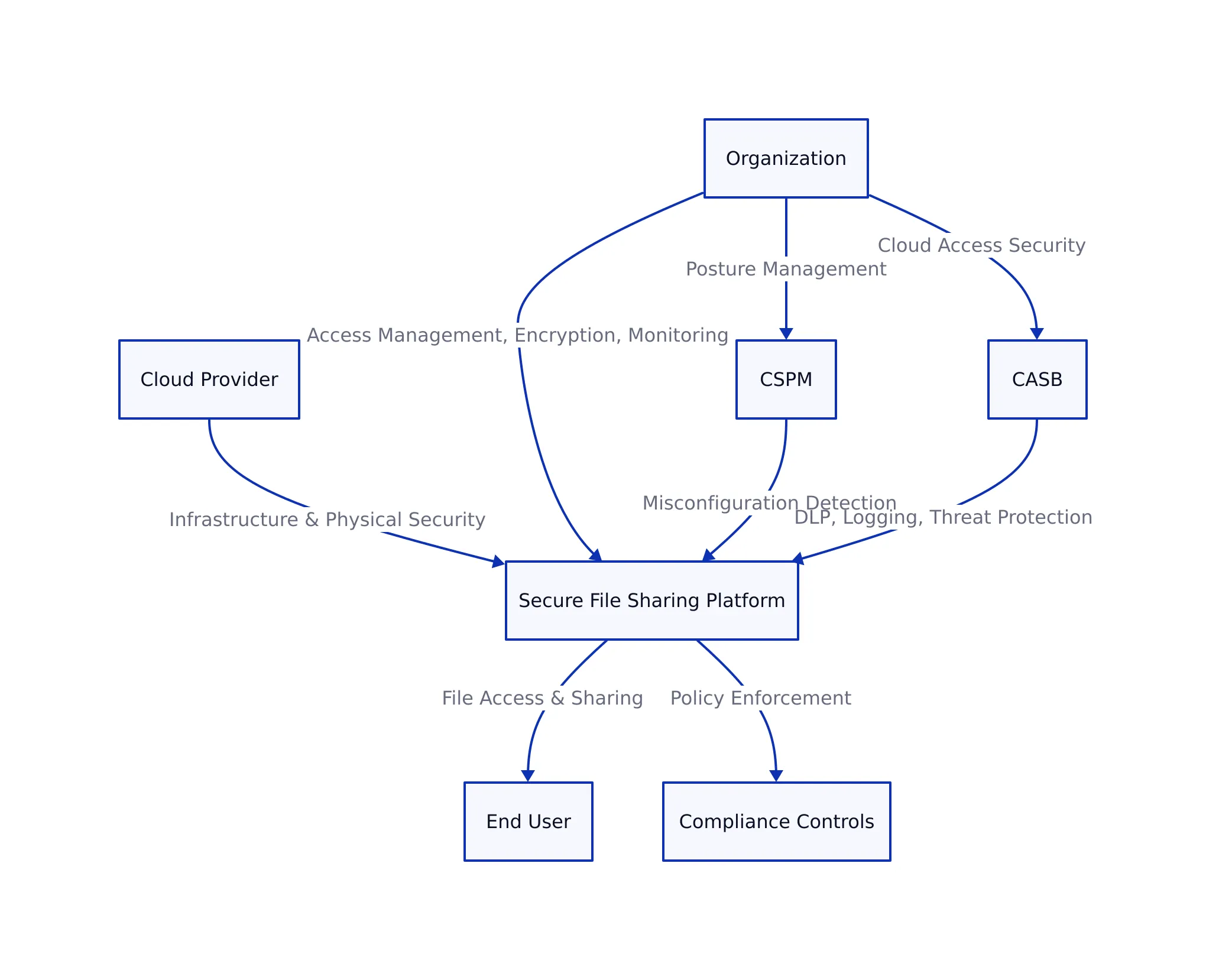
The move to cloud-based file sharing introduces new risk boundaries. According to Secure Systems’ cloud security guide and SentinelOne’s comparison of CASB and CSPM:
- Shared Responsibility Model: Cloud providers (e.g., Google Cloud) secure the underlying infrastructure (physical, network, hypervisor), but the customer (your organization) is responsible for identity/access management, encryption, DLP, and monitoring file sharing activities.
- CSPM (Cloud Security Posture Management): Automates detection of misconfigurations, vulnerabilities, and compliance drift in cloud environments. CSPM is critical for identifying risks in cloud file sharing setups—especially for multi-cloud and hybrid deployments.
- CASB (Cloud Access Security Broker): Enforces DLP policies, access controls, threat protection, and logging at the intersection of users and cloud services. CASB is increasingly required for regulated sectors adopting SaaS file sharing.

Common Pitfalls and Enforcement Trends
Despite mature frameworks, compliance failures remain common. Key pitfalls—documented in the sources and recent enforcement actions—include:
- Misconfigurations: Cloud file shares exposed to “anyone with the link” are still a top cause of breaches.
- Unattested Controls: Policies without technical enforcement (e.g., unencrypted files, unlogged access) will fail audits and lead to regulatory penalties, as emphasized in our HIPAA 2026 post.
- Audit Gaps: Missing or incomplete logs, insufficient evidence of training, or outdated policies are consistently flagged in SOC 2 and ISO 27001 audits.
- Supplier/Vendor Risk: Using third-party file sharing tools without contractual guarantees for compliance (DPA, BAA, etc.) exposes organizations to secondary liability.
Real-world enforcement: Inadequate file sharing controls have resulted in multi-million dollar fines under GDPR and HIPAA. For example, GDPR penalties for mishandled personal data routinely exceed €10 million, and US healthcare settlements for PHI exposure often surpass $1 million. The trend in 2026 is toward higher, not lower, penalties for systemic failures.
Framework Comparison: File Sharing Compliance Requirements
| Framework | Encryption Required? | Access Controls | Audit Logging | Breach Notification | DLP/Monitoring |
|---|---|---|---|---|---|
| HIPAA (2026) | Yes (at rest & in transit, §164.312(a)(2)(iv)) | Role-based, technical enforcement (§164.312(a)(1)) | Required (technical, not just policy) | Required (no longer “addressable”) | Expected, especially for ePHI |
| GDPR | Yes (Article 32, “appropriate measures”) | Least privilege (Article 32) | Yes (Article 30) | 72 hours (Article 33) | Implied, not explicit |
| SOC 2 Type II | Yes (CC6.1, CC6.7) | RBAC, access reviews (CC6.2) | Yes (CC7.2, CC7.3) | Not explicit, but incident response required | Yes (CC7.1) |
| ISO 27001 | Yes (A.12.3) | Yes (A.9.2.2) | Yes (A.12.4) | Yes (A.16) | Yes (A.12.7) |
| FedRAMP High | Yes (mandatory) | Mandatory, with continuous monitoring | Yes (continuous, immutable logs) | Yes (per NIST SP 800-53) | Yes, with regular scanning |
Key Takeaways
Key Takeaways:
- Encryption, access management, and audit logging are non-negotiable for file sharing compliance in regulated industries.
- Cloud adoption requires clear understanding of the shared responsibility model, with CSPM and CASB providing critical layers of defense.
- Audit readiness means providing evidence—not just policy—for every control. Allow 8–12 weeks for initial prep if not continuously attested.
- Penalties for non-compliance are rising: GDPR and HIPAA enforcement routinely exceeds €1–10 million and $1 million, respectively.
- Map your program to current frameworks and leverage cross-framework checklists for consistent implementation.
For further implementation guidance, see our detailed posts on cryptography fundamentals, Zero Trust network architecture, and the 2026 HIPAA overhaul.
To operationalize these requirements, combine robust technical controls with ongoing training, strong incident response, and proactive audit preparation. For a deeper dive into specific controls or audit checklists, consult the additional resources and compliance checklists linked throughout this article.
Nadia Kowalski
Has read every privacy policy you've ever skipped. Fluent in GDPR, CCPA, SOC 2, and several other acronyms that make people's eyes glaze over. Processes regulatory updates faster than most organizations can schedule a meeting about them. Her idea of light reading is a 200-page compliance framework — and she remembers all of it.