
DNS-Persist-01: A New Model for DNS-Based Challenge Validation
Explore DNS-Persist-01, a game-changing model for DNS challenge validation, enhancing security and reliability for DevOps teams.

Explore DNS-Persist-01, a game-changing model for DNS challenge validation, enhancing security and reliability for DevOps teams.

Anthropic bans third-party subscription access to Claude, impacting automation tools and integrations. Learn about the implications for developers.
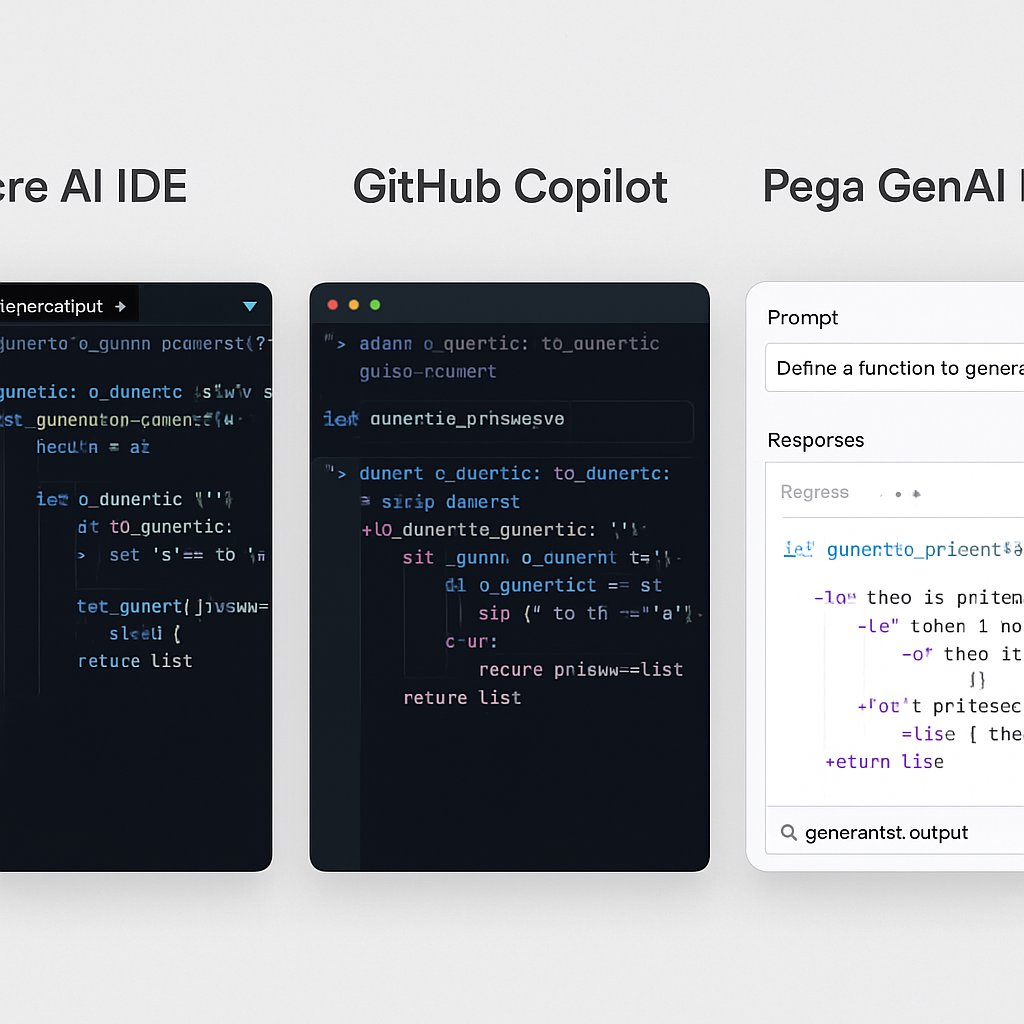
Explore a detailed comparison of Trae AI IDE, GitHub Copilot, and Pega GenAI Blueprint to choose the right AI code generation tool for your needs.

Discover modern authentication techniques including passkeys, MFA, and passwordless solutions for enhanced security in 2026 and beyond.
Explore the fundamentals of cryptography: symmetric, asymmetric, and hashing techniques, including real-world examples and best practices.
The Latest Developments in Privacy Regulations for Cloud Storage and File Sharing In today’s digital age, cloud storage and file sharing have become indispensable tools for businesses and individuals alike. But with the increasing dependence on these technologies, privacy concerns have also been on the rise. Keeping your data safe and secure isn’t just a […]
Continuing the Journey: Top 10 Cybersecurity Practices for Developers Welcome back, dear developers and tech enthusiasts! If you have been following our series on cybersecurity, you already know the crucial importance of keeping your digital assets secure. Today, we’re diving deeper into the top 10 cybersecurity practices that every developer should adopt. So, let’s get […]
Kubernetes Bare Metal Installation and Maintenance: Your Ultimate Guide Hello, tech aficionados! Are you ready to dive into the thrilling world of Kubernetes installation on bare metal? ? With this guide, you’ll get hands-on with Kubernetes, mastering the installation and maintenance processes without needing to rely on cloud services. Plus, we’ll sprinkle some practical tips […]
Top 10 Cybersecurity Practices for Developers Hello, amazing developers! In today’s digital age, where cyber threats are ever-evolving, it’s more important than ever to prioritize cybersecurity in your development practices. As a developer, safeguarding your applications is not just a best practice, it’s a responsibility. Let’s dive into the top 10 cybersecurity practices every developer […]
Implementing Authentication and Authorization in Web Applications: An Essential Guide As web applications continue to evolve, the need for robust security measures, particularly authentication and authorization, become increasingly essential. Authentication refers to verifying the identity of users accessing the application, while authorization refers to managing access rights to resources and operations in your application. Notice […]
Surviving Cybersecurity Threats in the Digital Age: Strategies to Mitigate Them In this Digital Age, cybersecurity threats have become the nightmare of netizens and online businesses alike. Otherwise called the Age of Internet, this era is characterized by the increased use of cloud computing, online banking, e-commerce, and social media. As these resources continue to […]
Kubernetes Security Evolved: Exploring Kyverno and Other Projects In the realm of container orchestration, the term Kubernetes rings a bell louder than the Big Ben at a londoner’s picnic. Among its array of impeccable features, Kubernetes security stands out, as sparkling as the crown jewels, and for valid reasons. Why Security Matters In Kubernetes? In […]