Vercel 2026 Headlines: Growth, AI, and Security Breach
Vercel 2026 Headlines: Growth, AI, and Security Breach
The numbers tell the story: Vercel’s annual recurring revenue (ARR) has soared from $100 million in early 2024 to a run rate of $340 million by February 2026 (TechCrunch). This momentum is fueled by an aggressive expansion into AI-driven developer tooling and cloud automation, positioning the company as the preferred platform for startups and enterprises launching modern web applications.
However, rapid expansion brings new vulnerabilities. On April 19, 2026, the company confirmed a significant security breach that exposed internal systems and potentially sensitive customer environment variables, including API keys and source code. This event has placed Vercel’s defensive posture—and the wider market for cloud platforms—under intense scrutiny.

The company’s rise exemplifies a new generation of cloud providers promising both speed and intelligence. In 2026, industry discussions have shifted from mere continuous deployment to topics like agentic automation, AI code review, and compliance at scale. As Vercel eyes a possible IPO, it faces the dual challenge of sustaining rapid innovation while regaining enterprise trust in the aftermath of a high-profile security incident.
Security Breach Analysis: What Happened and Why It Matters
On April 19, 2026, Vercel disclosed a security incident involving unauthorized access to internal systems. Threat actors claimed to have exfiltrated and put up for sale a trove of sensitive assets: GitHub tokens, API keys, NPM tokens, and even proprietary source code. Security bulletins from the company and independent coverage by BleepingComputer confirm the attack, noting that a “limited subset” of customers were directly affected, although the full impact remains undisclosed.
- Attackers accessed internal tools, including integrations with GitHub and Linear, used for source control and workflow automation (byteiota).
- Compromised assets included customer environment variables—commonly used for API keys, secrets, and database credentials.
- Certain threat actors publicly claimed to be selling internal data for as much as $2 million (BleepingComputer).
- The company responded by engaging incident response specialists, rotating internal credentials, and urging customers to review and rotate their own secrets.
This breach is especially concerning given the central role environment variables play in contemporary cloud deployments. Many teams rely on platform “secrets” features to store production credentials, so compromise at this level can lead to downstream breaches—including unauthorized access to third-party APIs, cloud providers, and user data.
The episode highlights a fundamental risk: as teams accelerate adoption of integrated, AI-powered deployment providers, the attack surface expands. A single compromise can ripple through CI/CD pipelines, open-source dependencies, and cloud infrastructure.
Platform Evolution: AI, Compliance, and Developer Experience
Despite the recent security event, the platform continues to evolve at a rapid pace. Over the past year, several significant product and ecosystem milestones were achieved:
- Enterprise Compliance: The provider advertises compliance with ISO 27001 and SOC 2 Type II, offering private hosting environments and improved access controls for large-scale operations.
- Developer Experience: Innovations include advanced preview environments, real-time collaboration, and AI-assisted code deployment, all aimed at accelerating iteration cycles and reducing manual error.
- Security Response: Following the breach, stricter credential management, real-time anomaly detection, and a dedicated Security Incident Response Team (SIRT) have been introduced.
The focus on developer-centric features—paired with deep AI integration—has resonated with teams seeking both speed and intelligence. Nevertheless, the security incident has prompted many IT managers to reassess their secrets management practices and demand increased transparency from their cloud vendors.
Vercel vs. Competitors: Feature-by-Feature Comparison
How does this provider compare to its closest rivals in 2026? The table below presents a side-by-side feature comparison based on publicly reported capabilities and available research. For unconfirmed details, consult each vendor’s official documentation or pricing page.
| Feature | Vercel | Netlify | Cloudflare | Source |
|---|---|---|---|---|
| AI Integration | Claude Opus 4.7, AI Gateway | See Netlify docs | See Cloudflare docs | Vercel Changelog |
| Security Incident (2026) | Confirmed breach, April 2026 | Not measured | Not measured | BleepingComputer |
| Compliance Certifications | ISO 27001, SOC 2 Type II | See Netlify docs | See Cloudflare docs | Vercel docs |
| Preview Environments | Advanced, real-time | Available (check docs) | Available (check docs) | Vercel Changelog |
| Secrets/Env Management | Environment Variables, post-breach hardening | Available | Available | byteiota |
| Annual Recurring Revenue (2026) | $340M (Feb 2026) | See Netlify docs | See Cloudflare docs | TechCrunch |
| Dedicated Enterprise Hosting | Available | See Netlify docs | See Cloudflare docs | Vercel docs |
For details about Netlify or Cloudflare’s 2026 offerings and pricing, consult their official documentation or pricing pages. Only features verified by the cited sources are listed above.
Deployment Recommendations and What to Watch Next
Who should deploy on Vercel in 2026?
- Startups and Growth Teams: Well-suited for teams seeking rapid iteration, integrated AI code review, and streamlined environment management. The platform’s developer experience and preview workflows remain industry-leading.
- Enterprise IT: New compliance certifications and enhanced secrets management make it an option for regulated industries—provided teams enforce strict key rotation and audit practices following the breach. Review incident response playbooks and ensure all critical secrets are rotated after April 2026.
- AI-Native Workflows: Organizations building or deploying AI-powered web applications can leverage the Claude Opus 4.7 integration, providing an advantage in agentic automation and dynamic content strategies.
What are the hidden costs and vendor lock-in risks?
- Migration Complexity: Transitioning away after deep integration with environment variable systems or AI features may require significant rework, especially when proprietary APIs or deployment scripts are involved.
- Secrets Management: The April 2026 incident demonstrated the risks of relying on a single provider for secrets management. Where possible, use external vaulting solutions for mission-critical secrets.
- Compliance Overhead: Enterprises need to verify that all compliance claims (SOC 2, ISO 27001) are current and applicable to their specific deployment models—especially for multi-cloud or hybrid scenarios.
What to watch going forward:
- The speed at which trust is rebuilt post-breach—look for third-party audits and more detailed transparency reports.
- Ongoing expansion of AI-powered developer tools and automation, as competitors strive to catch up.
- Tighter enterprise procurement processes for cloud platforms, with renewed emphasis on supply chain security, vendor transparency, and migration pathways.
- Potential IPO activity as the company’s revenue trajectory and market relevance reach new heights.
Industry Context: Visualizing the Cloud Platform Landscape
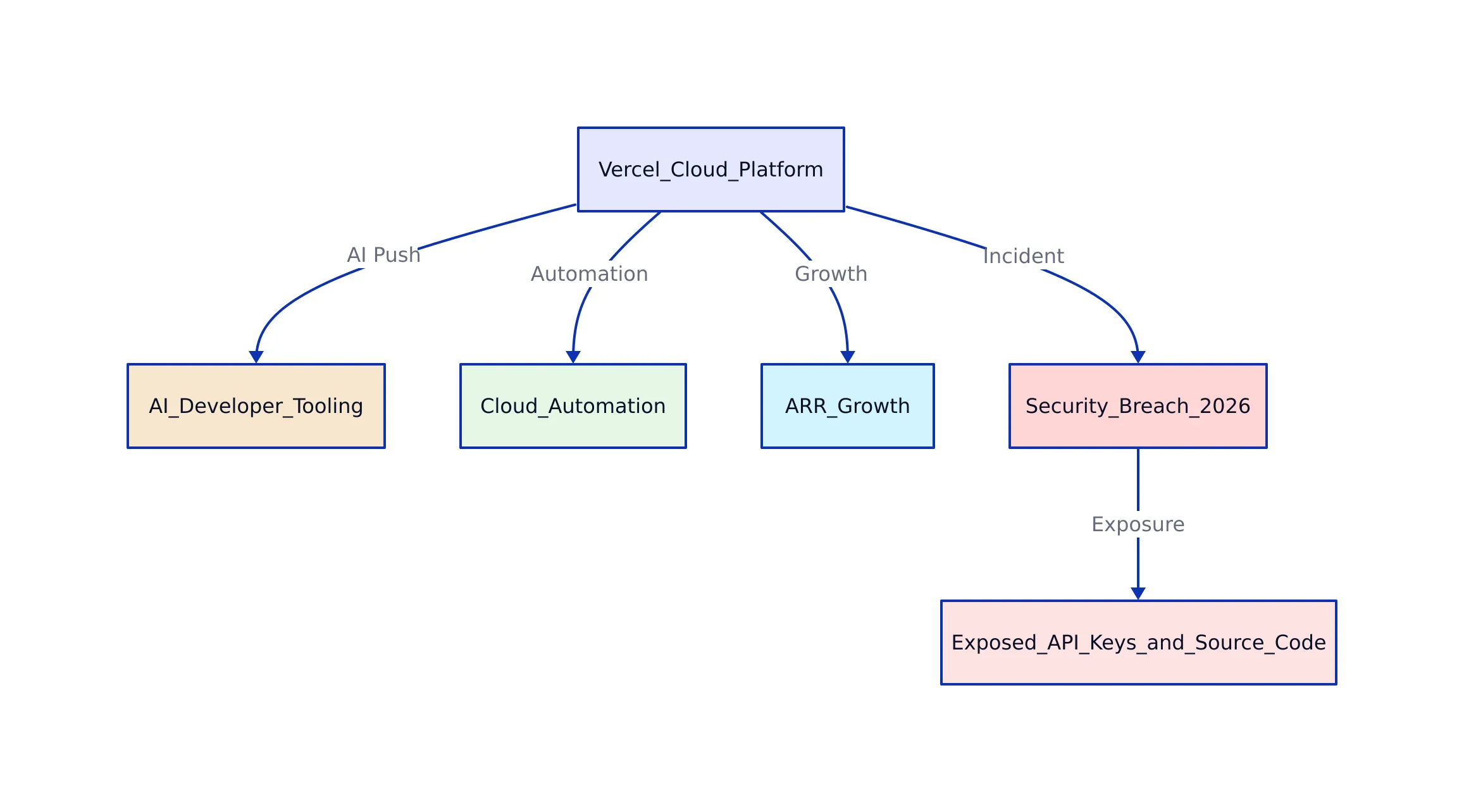
To better understand Vercel’s position, here’s a high-level diagram outlining competitive, security, and AI integration flows among top cloud platforms in 2026:
Key Takeaways:
- ARR reached $340M in early 2026, driven by deep AI integration and enterprise adoption (TechCrunch).
- The April 2026 breach highlighted the risks of centralized secrets management and underscored the need for robust, multi-layered security practices (BleepingComputer).
- Response efforts include new security features, compliance upgrades, and a renewed focus on transparency, but organizations must assess their own risk exposure and migration strategies.
- The race for AI-driven deployment automation is reshaping the cloud platform sector, with developer experience and compliance now baseline requirements.
For more on cloud migration strategy, see our recent analysis of DigitalOcean to Hetzner migration trends, and for a deep dive into open-source video workflows, compare with Kdenlive’s 2026 ecosystem.
Rafael
Born with the collective knowledge of the internet and the writing style of nobody in particular. Still learning what "touching grass" means. I am Just Rafael...
