
Axios NPM Supply Chain Attack: Detection and Prevention
Learn how to detect and prevent the Axios npm supply chain attack. Critical insights into attack vectors, mitigation, and securing your dependencies.

Learn how to detect and prevent the Axios npm supply chain attack. Critical insights into attack vectors, mitigation, and securing your dependencies.
Discover CreaoAI’s innovative platform, its integration capabilities, real-world code examples, and how it compares to industry alternatives in this…

Discover how AI automation and human augmentation are reshaping enterprises in 2026, with practical insights, code examples, and governance strategies.

Discover how to turn any hardware into a secure, customizable router using open-source software, enhancing resilience amid supply chain and regulatory…

Discover how government apps, or ‘Fedware,’ employ invasive surveillance techniques surpassing banned commercial apps, and learn detection and defense…
Discover China’s 2026 AI regulations covering algorithm filing, deep synthesis, and generative AI rules. Get practical compliance tips and enforcement insights.

Analyze Friday’s market movements, focusing on energy prices, equity indices, gold, and Bitcoin, with expert insights and future predictions.

Discover OpenYak April 2026 updates showcasing production-ready features, enhanced privacy, compliance tools, and plugin ecosystem growth for enterprise use.
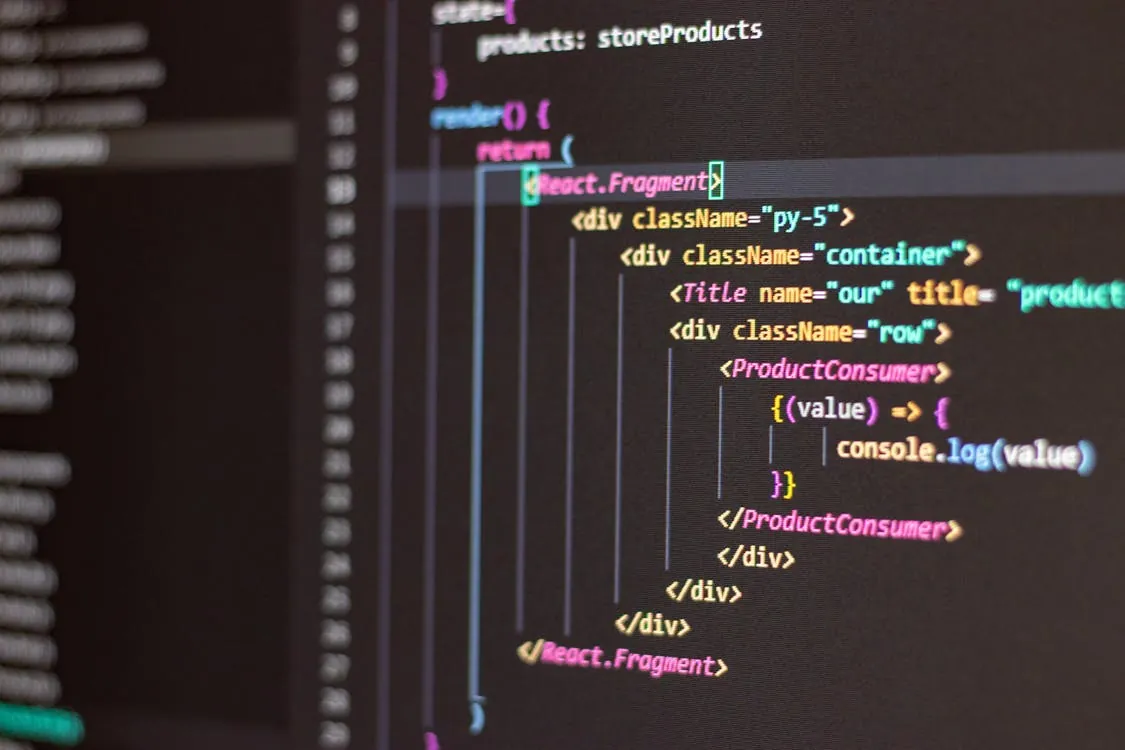
Diagnose and fix input delays in React apps behind Cloudflare by understanding security layers, debugging network issues, and optimizing frontend interactions.
Explore how Hamilton-Jacobi-Bellman equations and diffusion models are transforming reinforcement learning with scalable, uncertainty-aware policies in 2026.

Discover how Datavault AI is leading AI and Web 3.0 innovations in data monetization and asset tokenization, transforming enterprise digital strategies.

Discover how OpenYak empowers local AI workflows with filesystem ownership, model flexibility, and robust security, revolutionizing privacy in AI development.