
Redis Caching Patterns: Best Practices for Application Optimization
Explore Redis caching patterns with real-world examples and best practices to optimize performance, consistency, and scalability in your applications.

Explore Redis caching patterns with real-world examples and best practices to optimize performance, consistency, and scalability in your applications.

Oil stabilizes at $98.71 while gold rises above $5,060 amid Middle East tensions, highlighting safe-haven demand and supply concerns impacting markets.

Learn how to set up and optimize PostgreSQL connection pooling with PgBouncer. Tips on configuration, avoiding pitfalls, and effective monitoring strategies.

Discover how kernel-level anti-cheat systems work, their detection methods, and the risks they pose to privacy, stability, and cross-platform compatibility.

Discover a sleek TCP hole punching algorithm for NAT traversal that enables direct peer-to-peer connections, reducing latency and reliance on relays.

Analyze oil, rates, and risk signals that shaped European markets amid geopolitical tensions and energy shocks over the weekend.
Learn how to implement Kubernetes Pod Security Standards effectively, avoid common pitfalls, and follow best practices for secure workloads.

Explore Friday’s market movements amid energy shocks and geopolitical tensions, highlighting key indices, sector performance, and macroeconomic signals.

US stock market closed flat on March 14, 2026. Recap, movers, sectors, macro factors, and key next steps to watch in upcoming trading sessions.
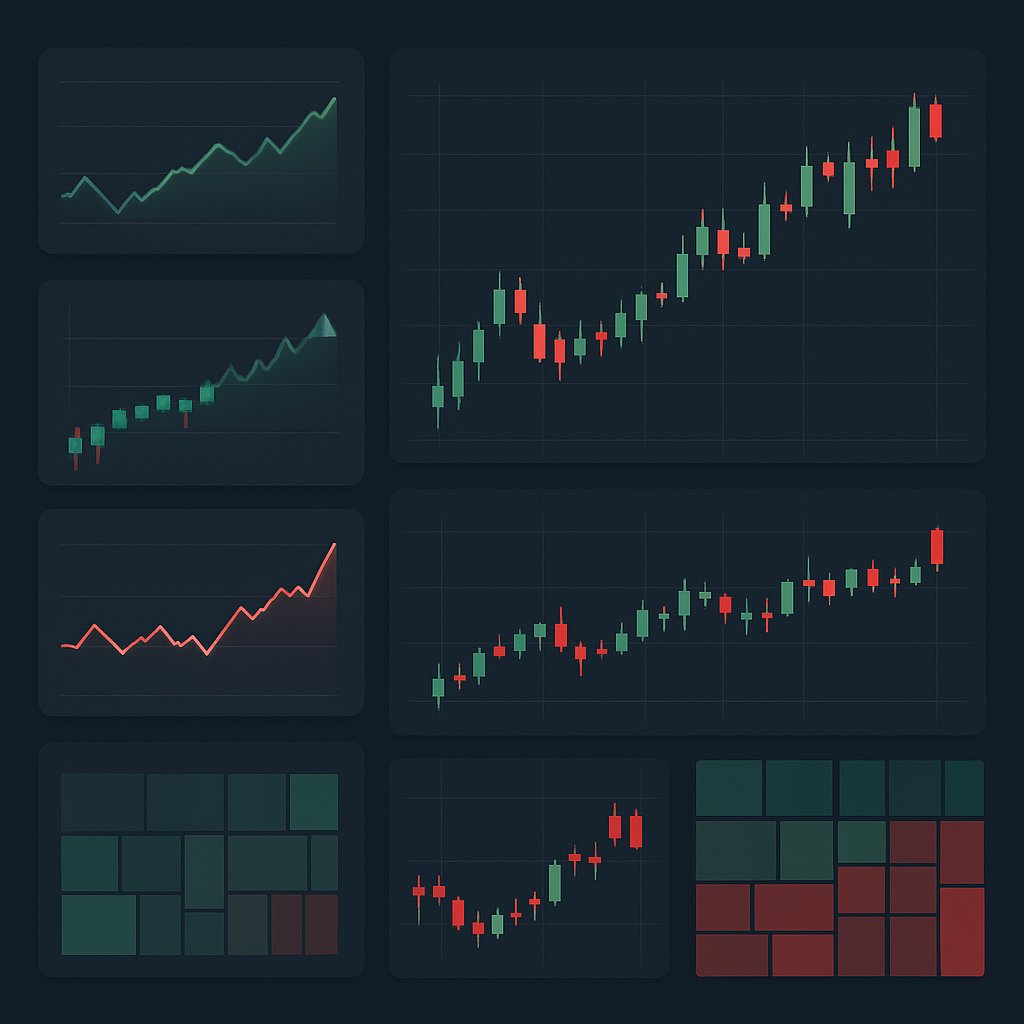
Market recap of the March 14, 2026 US stock close, highlighting index levels, top movers, sector performance, and key upcoming events for investors.
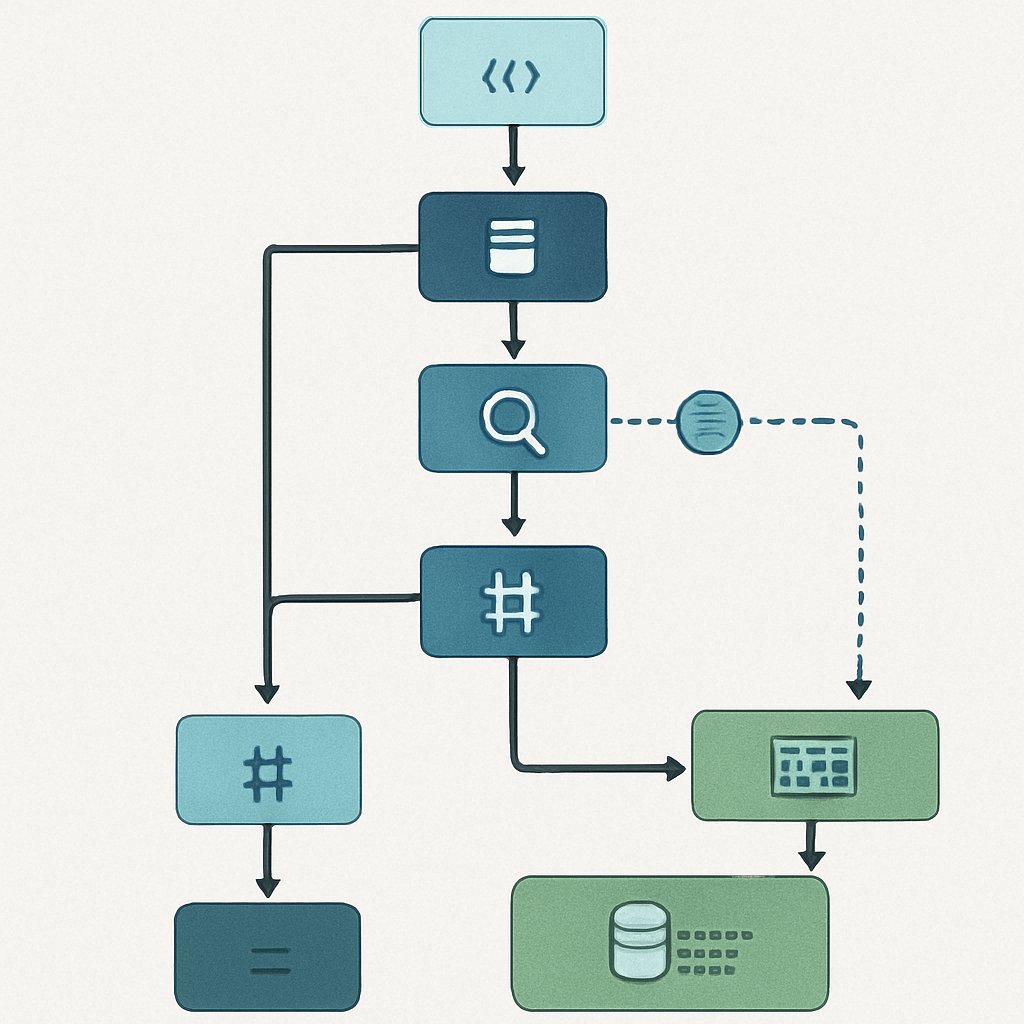
Learn how to use EXPLAIN ANALYZE in PostgreSQL for effective query optimization. Discover real-world tips to improve performance and interpret plans.

Recap of the US stock market close on March 14, 2026, highlighting index movements, sector performance, top movers, macro factors, and investor outlook.