
Zero Trust Architecture: Principles and Implementation
Learn the principles and actionable strategies for implementing Zero Trust Architecture in your organization, backed by NSA guidelines.

Learn the principles and actionable strategies for implementing Zero Trust Architecture in your organization, backed by NSA guidelines.
Discover how a Microsoft 365 Copilot bug exposed confidential emails, bypassing DLP policies, and learn effective mitigation strategies.

Explore DNS-Persist-01, a game-changing model for DNS challenge validation, enhancing security and reliability for DevOps teams.

Discover the implications of the newly discovered Chrome zero-day CVE-2026-2441, its exploitation risks, and how to secure your browser now.
Discover how DNS-PERSIST-01 changes the game for automated certificate validation and management, reducing operational complexity and risk.

CVE-2026-2441 is a critical Chrome zero-day under active attack. Immediate updates are essential to protect users from exploitation.

Discover common pitfalls in incident response and actionable troubleshooting techniques to enhance your cybersecurity strategy.

Explore how GrapheneOS is breaking free from Google and Apple, expanding into Snapdragon devices for enhanced mobile privacy.
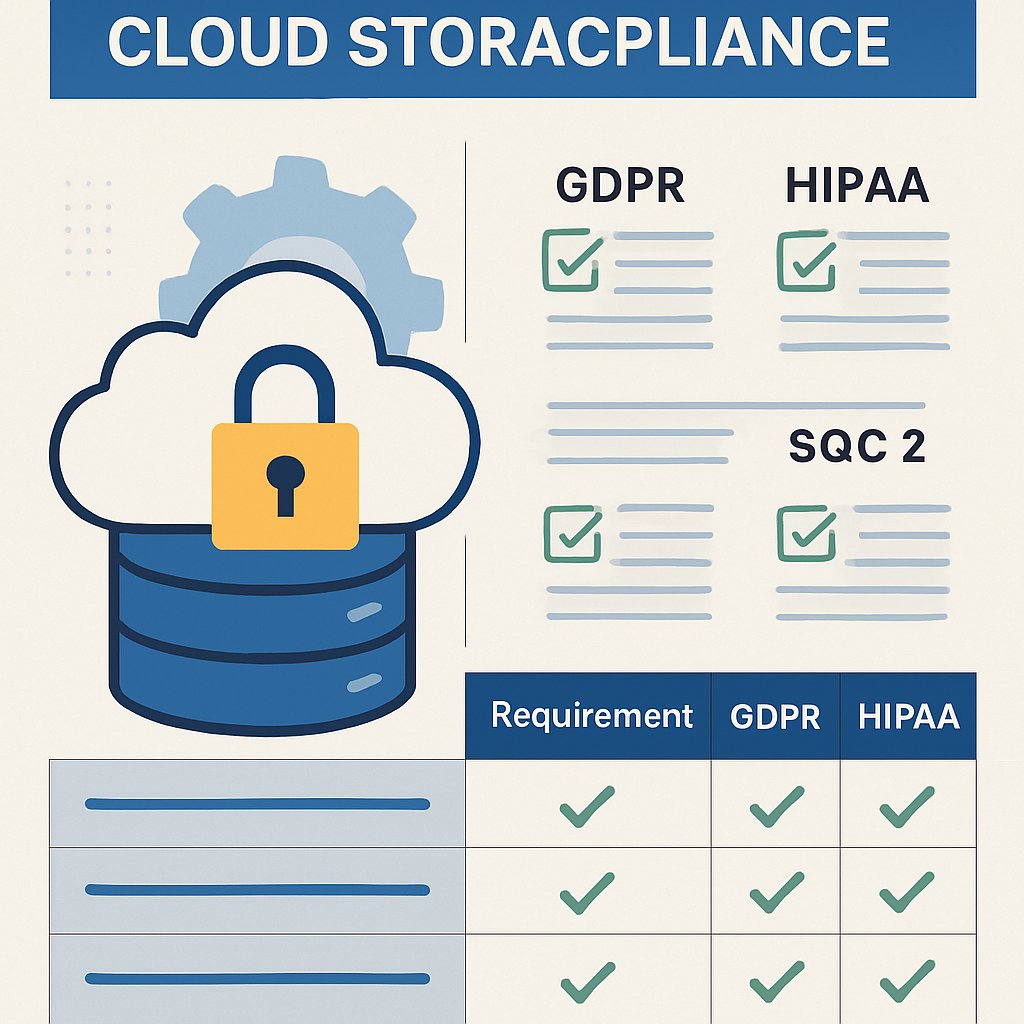
Get a quick reference for cloud storage compliance with GDPR, HIPAA, and SOC 2. Use this guide for audits, migrations, and vendor evaluations.
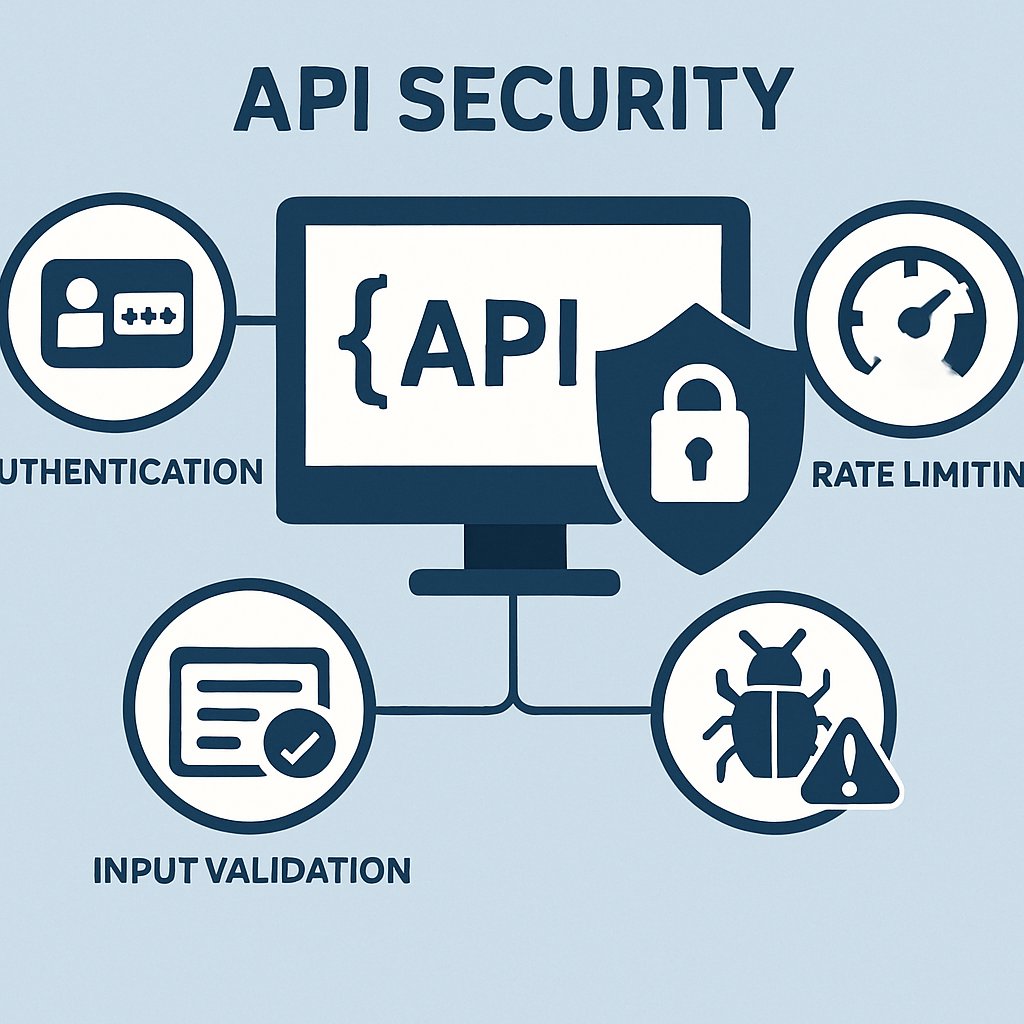
Explore common API security mistakes, their symptoms, and effective troubleshooting solutions to enhance your API defenses and prevent breaches.

Secure your APIs with robust authentication, rate limiting, and input validation strategies to mitigate risks and safeguard sensitive data.

Discover modern authentication techniques including passkeys, MFA, and passwordless solutions for enhanced security in 2026 and beyond.