
Data Sovereignty in Cloud Architecture: Compliance & Audit Strategies
Learn how to design cloud architectures that ensure data sovereignty compliance and prepare for audits with best practices and regional controls.

Learn how to design cloud architectures that ensure data sovereignty compliance and prepare for audits with best practices and regional controls.

Learn how trusted Unix binaries like bash and python are exploited as attack vectors, and discover effective detection and mitigation strategies.

Discover how AI is transforming crypto scams in 2026, from deepfake videos to automated phishing, and learn strategies to defend against these sophisticated…

Discover how the decline in Western manufacturing and coding skills in 2026 poses operational risks and how to address this strategic challenge.

Discover the details of the recent Bitwarden CLI supply chain breach, its impact, detection strategies, and best practices to safeguard your software…

Discover the root causes behind Claude’s 2026 code quality decline, practical fixes, security risks, and operational lessons for AI-powered development tools.

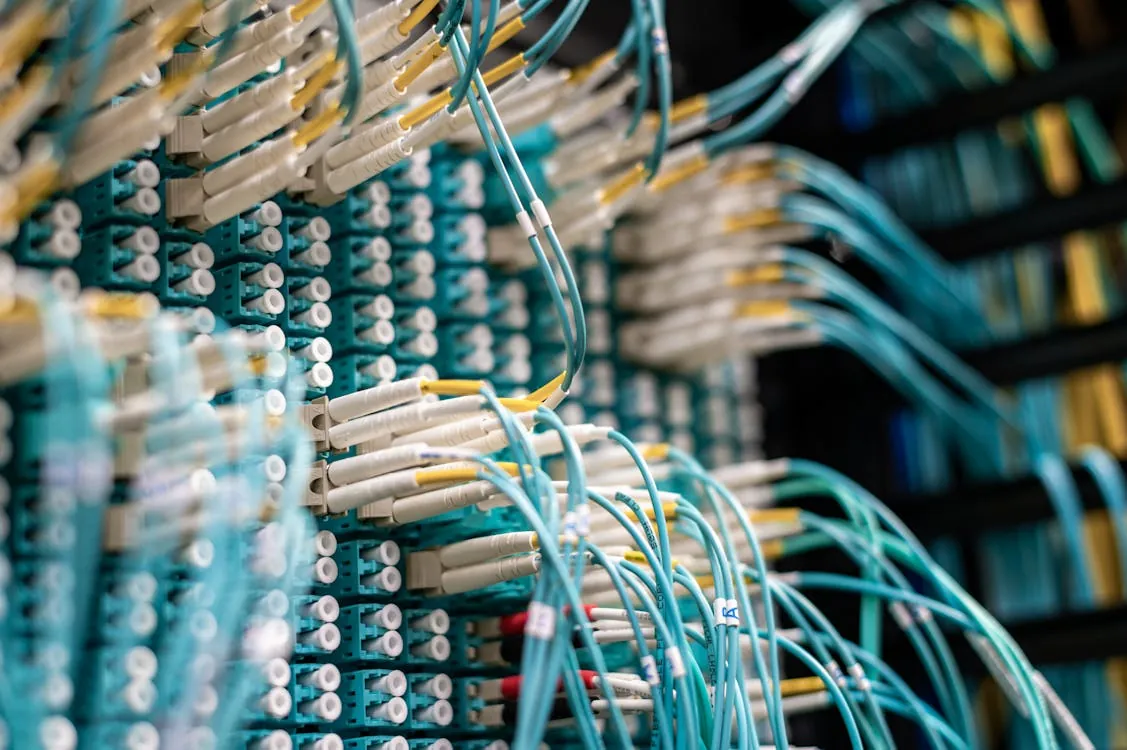
Learn how to implement network segmentation strategies to enhance security, meet compliance standards, and reduce organizational scope using layered…

Discover how Apple fixed a critical security flaw allowing forensic tools to recover deleted messages from iOS notification caches, enhancing user privacy…

Discover strategic insights for building a modern cloud in 2026, emphasizing automation, security, multicloud strategies, and cost management for enterprise…

Learn scalable methods for deploying Firefox extensions at scale, including policies.json and automation techniques, while understanding security pitfalls.

Discover essential software engineering laws for 2026, including modern challenges like AI, security, and compliance, with practical code examples and…
Learn how to build a multi-layer DDoS protection architecture with CDN, WAF, and origin shielding to defend against volumetric and application-layer attacks.