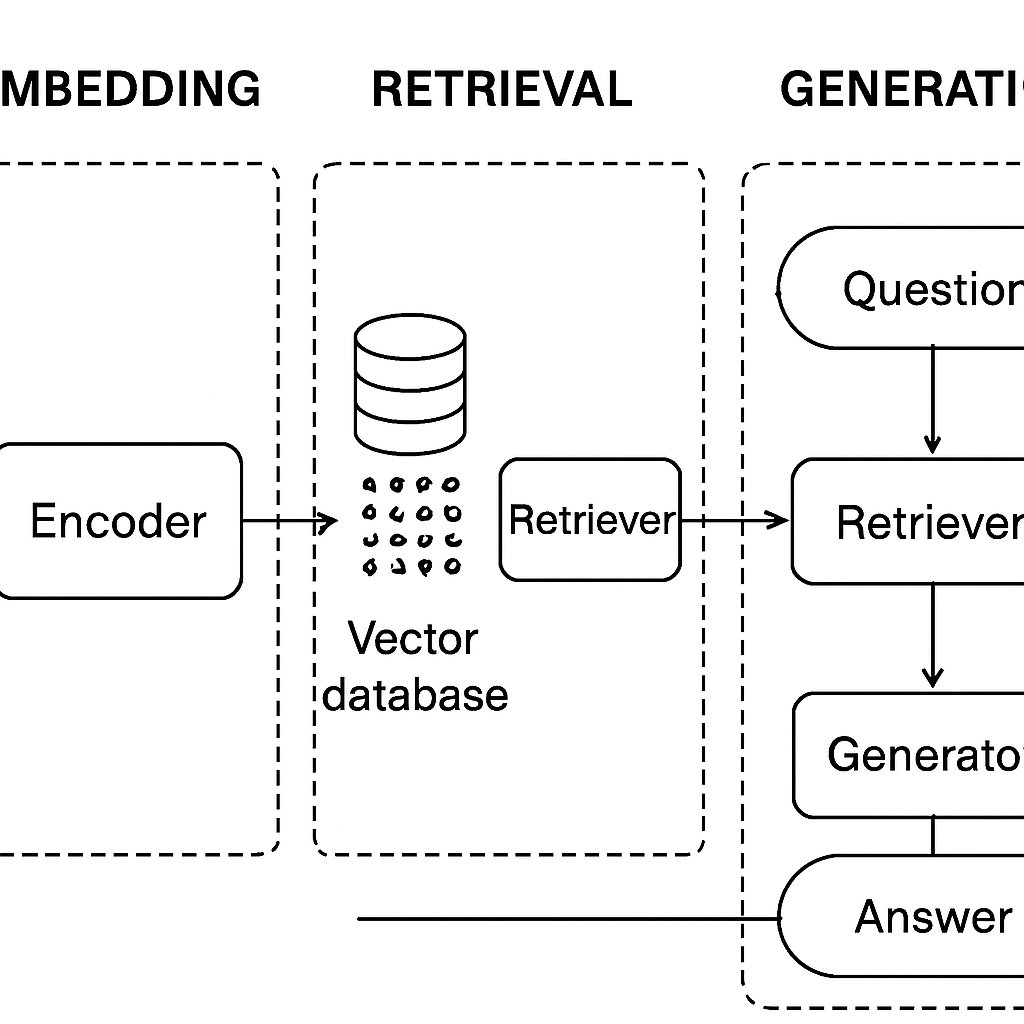
Implementing RAG for Enterprise Knowledge Management
Learn to implement a Retrieval-Augmented Generation (RAG) pipeline for enterprise knowledge using code examples and cost analysis.
Learn to implement a Retrieval-Augmented Generation (RAG) pipeline for enterprise knowledge using code examples and cost analysis.

Explore the rising legal threats in vulnerability disclosure, recent CVE trends, and best practices for responsible reporting.
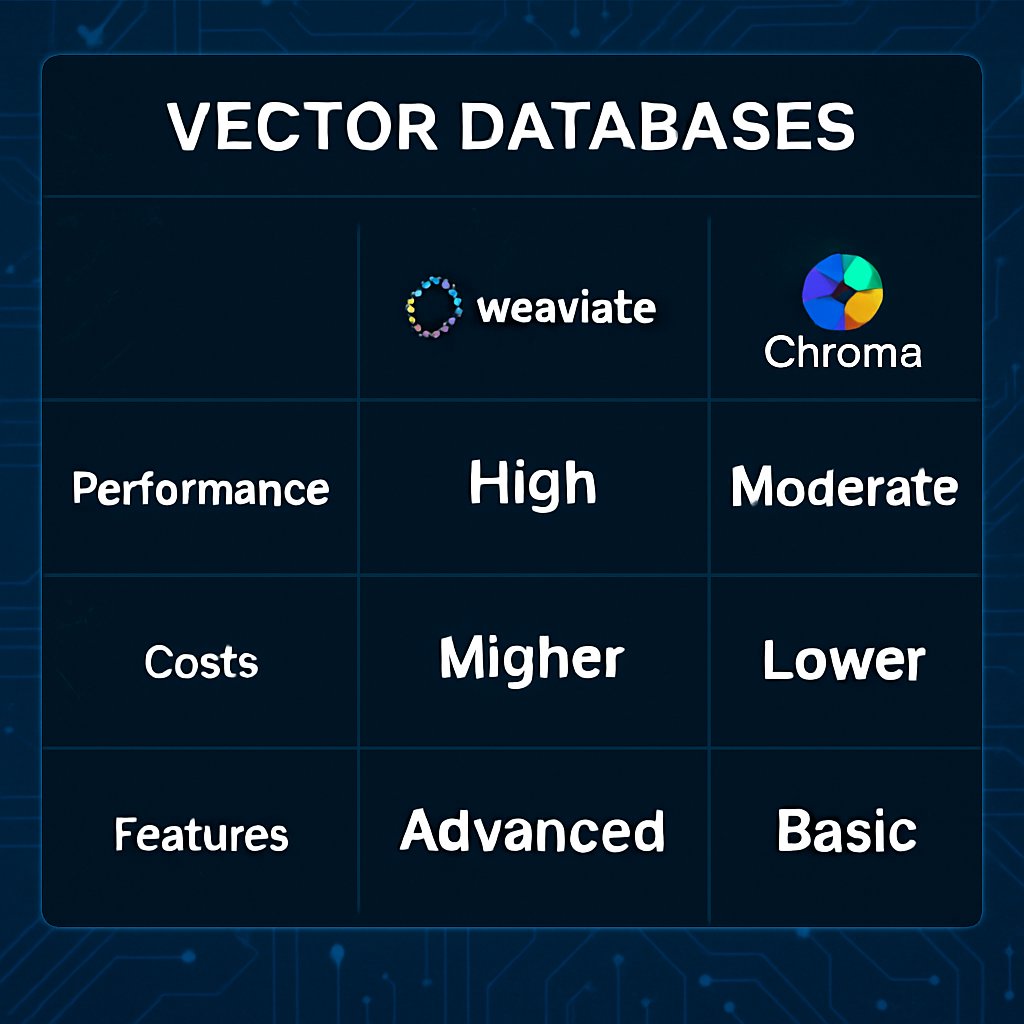
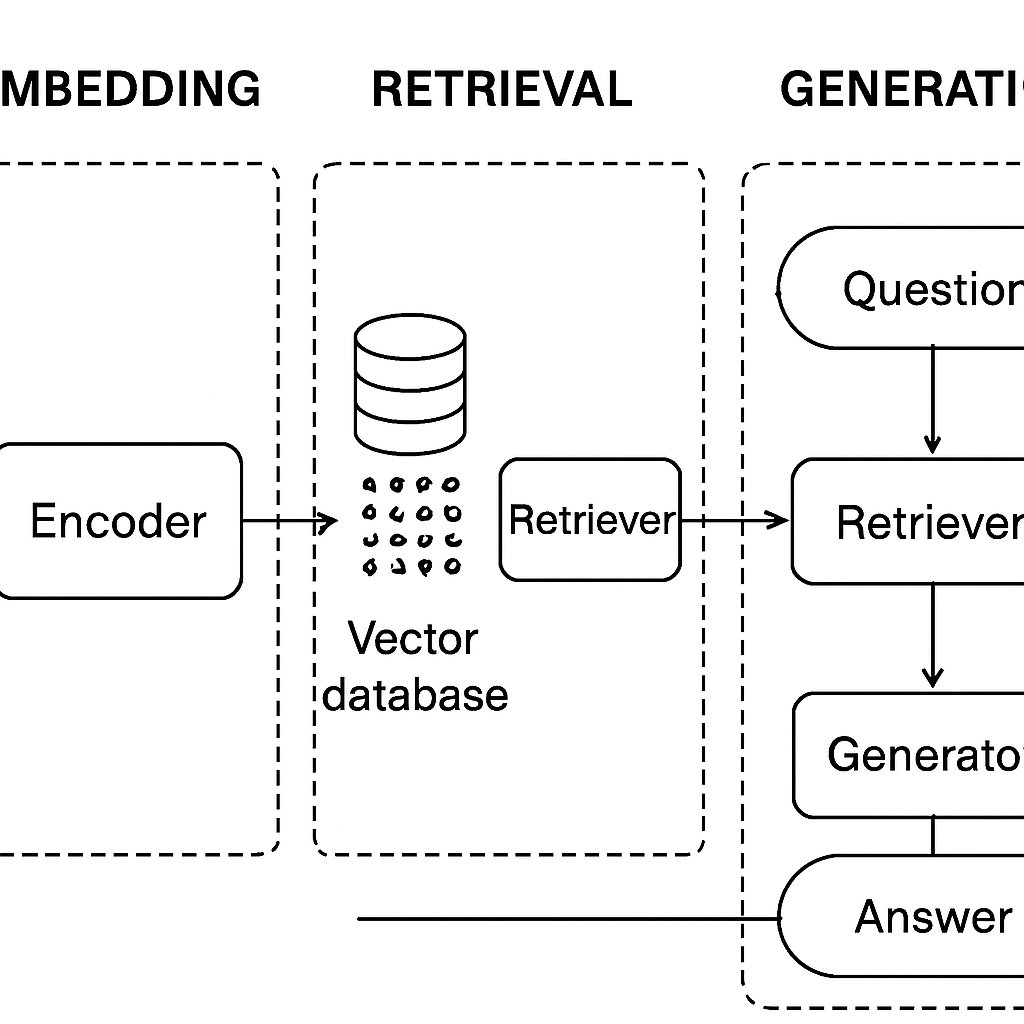
Discover how Pinecone, Weaviate, and Chroma compare as vector databases for AI, including performance metrics, costs, and integration patterns.
Discover a powerful Git one-liner found in leaked CIA documents that can enhance your code auditing process and improve source integrity.

Learn how to access the MEMS accelerometer on Apple Silicon MacBooks using IOKit HID and Python, with crucial compatibility and security tips.
Discover how Consistency Diffusion Language Models achieve up to 14.5x faster inference without degrading quality, transforming LLM deployment.
Explore Google’s Gemini 3.1 Pro, its advanced AI reasoning capabilities, and critical considerations for deployment in real-world applications.
Optimize your SQL queries with effective strategies: learn about EXPLAIN plans, indexing, and common pitfalls to improve database performance.

Explore advanced concurrency techniques in Go: worker pools, select patterns, sync package optimizations, and edge case solutions.
Learn how to use Python decorators and context managers to write cleaner, more maintainable code. Practical examples included.

Discover the implications of the newly discovered Chrome zero-day CVE-2026-2441, its exploitation risks, and how to secure your browser now.
Explore the key differences between Hindley-Milner and bidirectional typing to make informed decisions for your programming language or DSL.