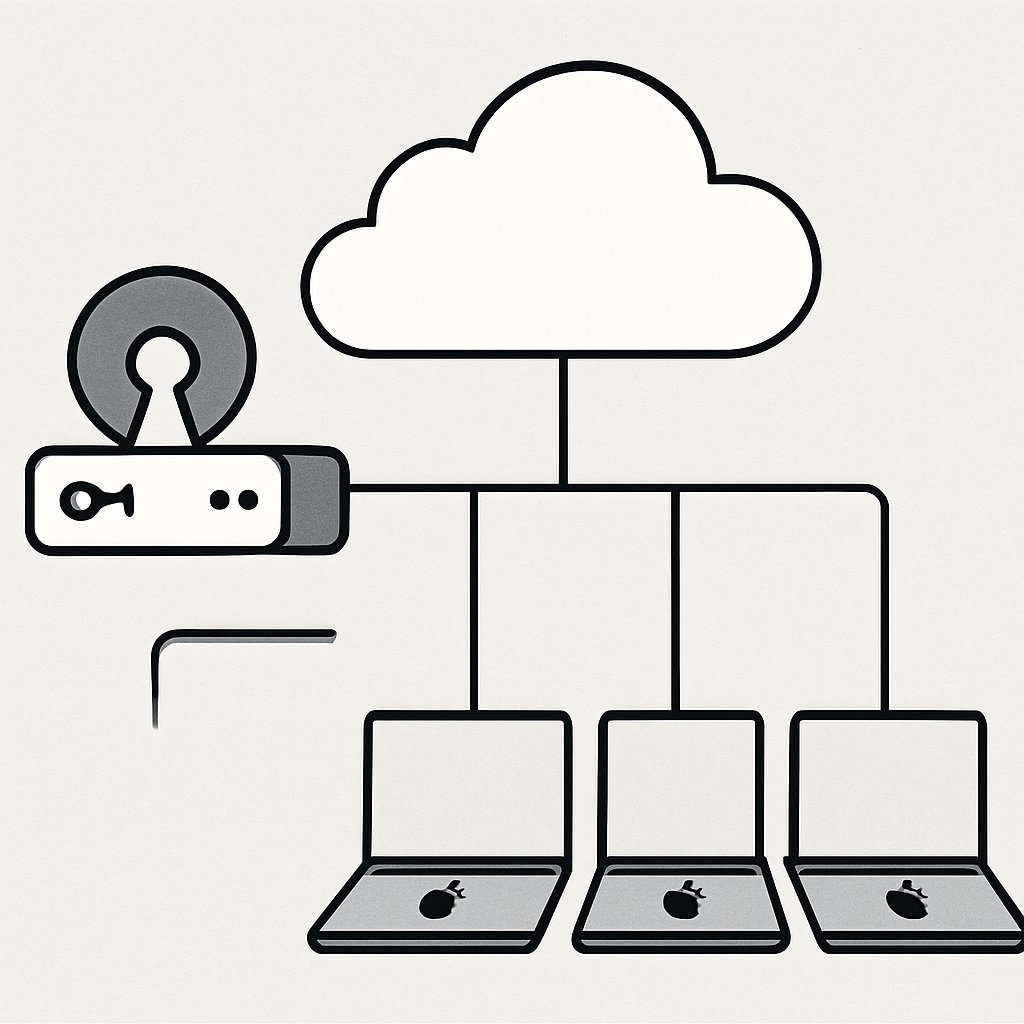
NanoMDM Architecture and Lessons for Small Mac Fleets
Explore a real-world NanoMDM deployment for managing small Mac fleets, covering architecture, setup, features, and trade-offs in a practical case study.
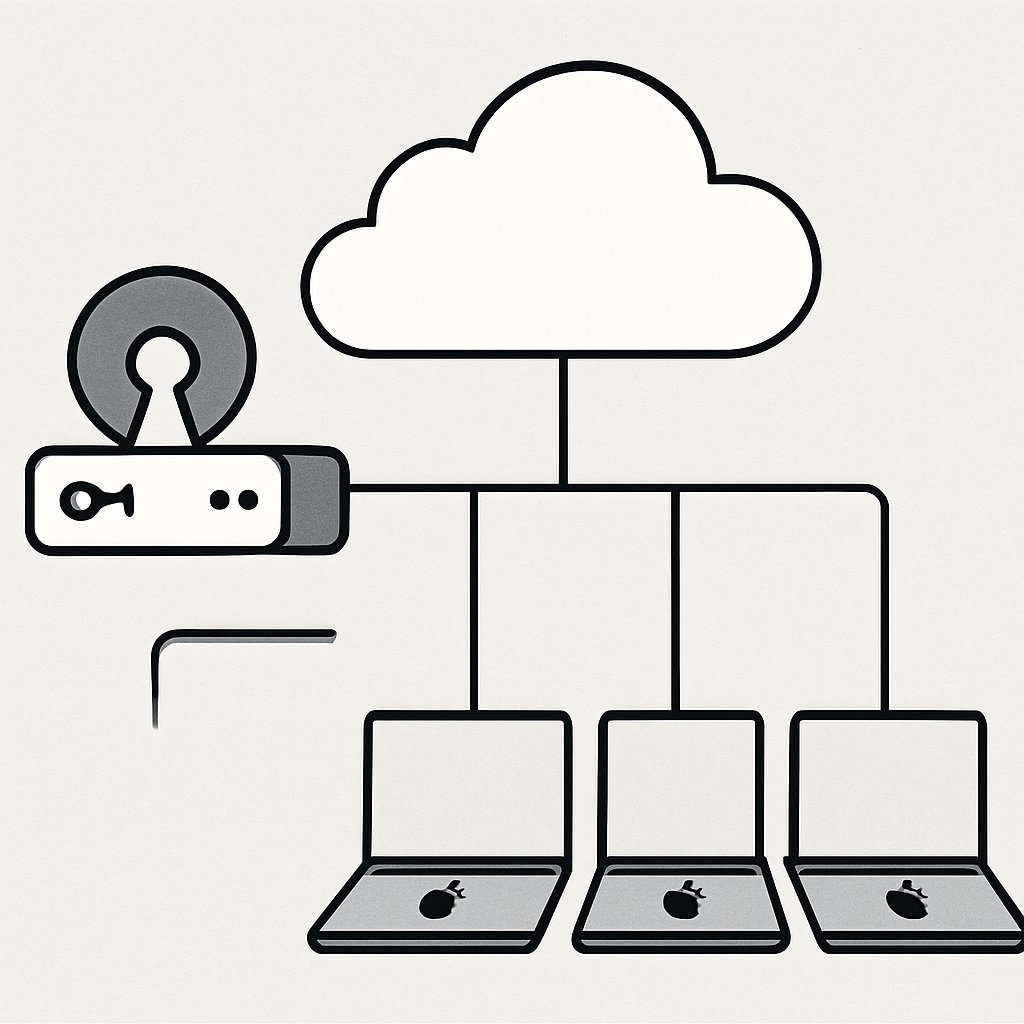
Explore a real-world NanoMDM deployment for managing small Mac fleets, covering architecture, setup, features, and trade-offs in a practical case study.

Explore how s@ enables decentralized social networking over static sites, focusing on privacy, security, and operational simplicity for trusted small groups.

Learn how to defend against modern, AI-powered social engineering attacks with technical controls, procedural safeguards, and behavioral strategies in 2026.

Organized entities like paper mills and brokers are fueling scientific fraud at scale, outpacing legitimate research and undermining trust in science.

Learn how to control AI and crawler traffic with Cloudflare’s advanced tools, ensuring security, performance, and SEO through granular policies and monitoring.

Learn how to build a practical data classification framework with clear levels, automation, and user training to improve data security and compliance.

Discover effective tools and compliance strategies for secure file sharing between China and international teams, overcoming the Great Firewall obstacles.

Learn how to secure file sharing with encryption, access controls, and audit trails to meet compliance standards and reduce risk in 2026.

Discover how your Bluetooth devices can leak personal information, from daily routines to private habits. Learn to protect your data effectively.

Discover how to create a real-time OSINT dashboard with actionable intelligence from 15 global feeds, enhancing your situational awareness.

Explore how a global SaaS provider enhanced security by leveraging a layered WAF architecture with ModSecurity, Cloudflare, and AWS WAF.
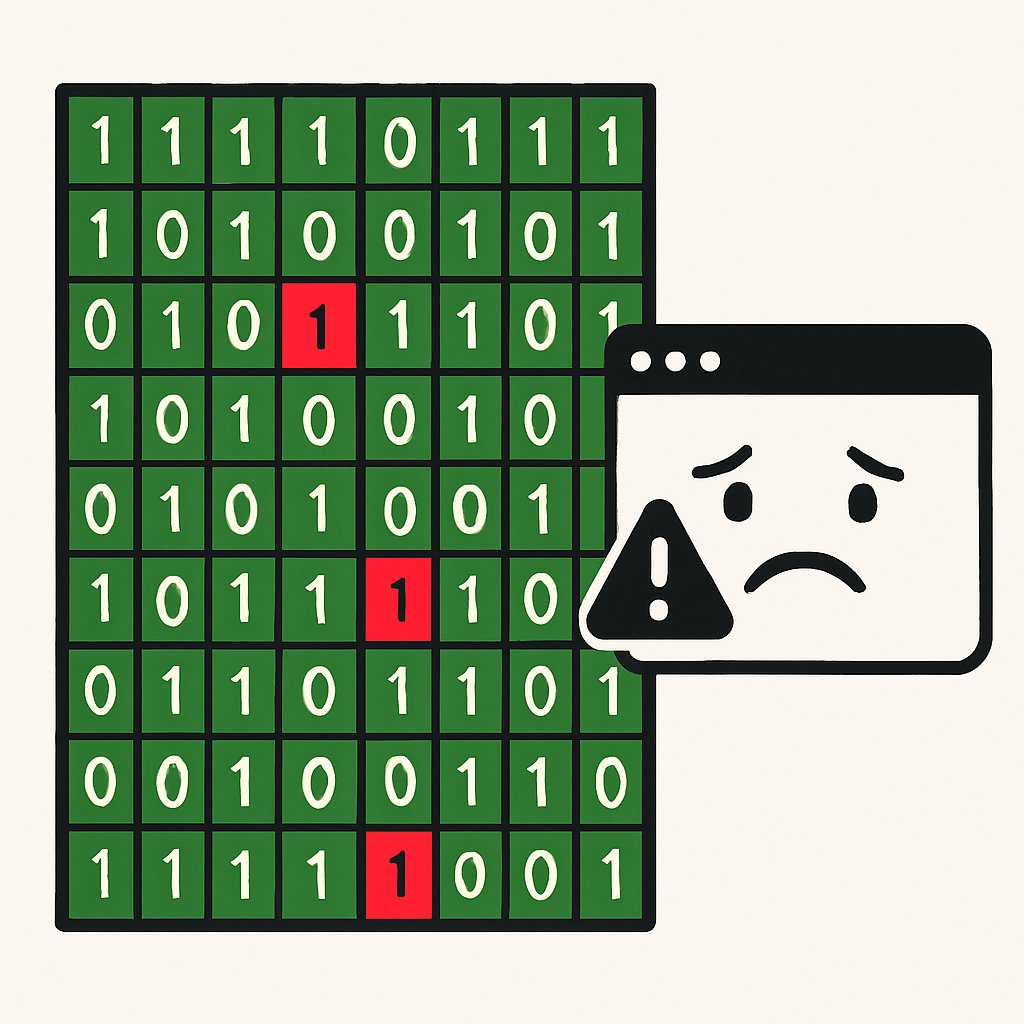
Explore how hardware-induced bitflips significantly impact Firefox crashes and learn effective mitigation strategies for browser stability.